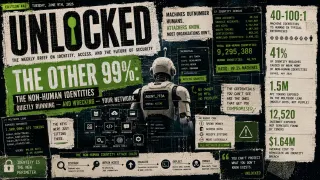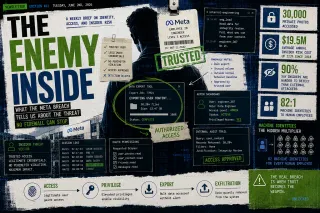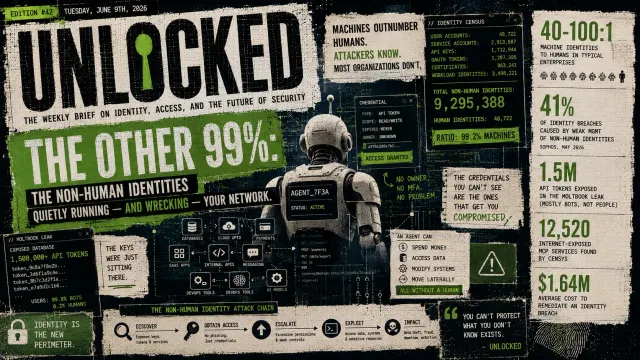
The Other 99%: The Non-Human Identities Quietly Running — and Wrecking — Your Network
An AI social network just leaked 1.5 million API keys belonging to its bots. It's a preview of the biggest blind spot in security: the non-human identities that now outnumber your people 40-to-1 — and the agents minting thousands more every day.