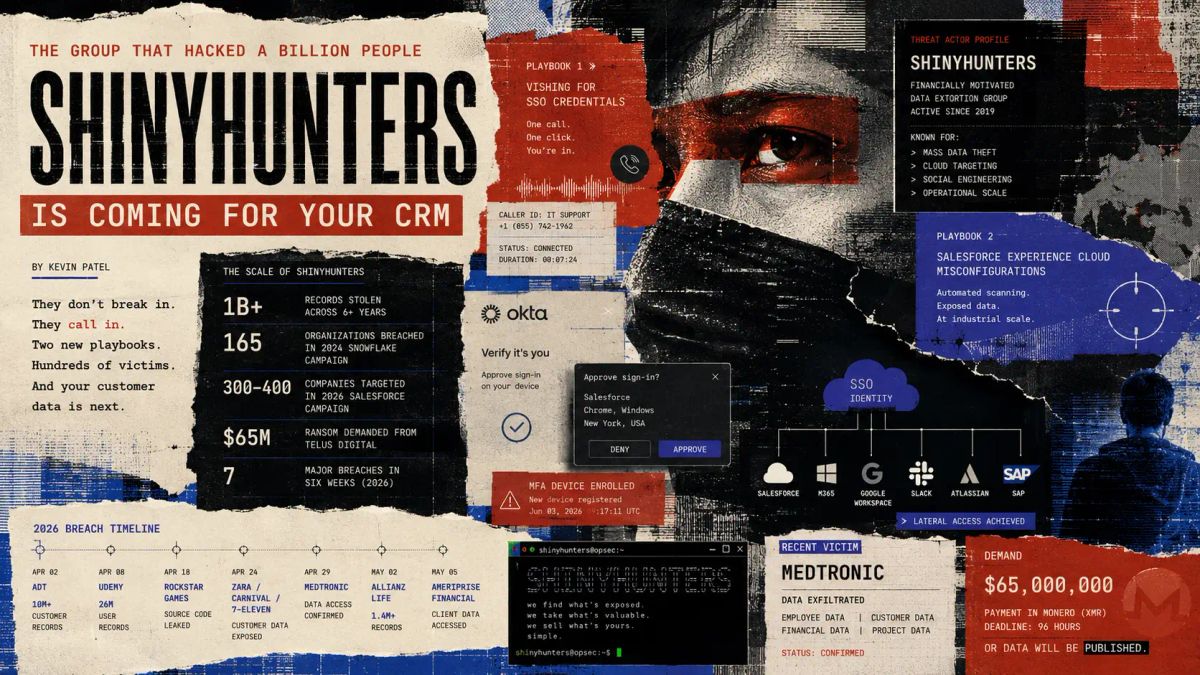
The ShinyHunters Playbook: The Group That Hacked a Billion People Is Coming for Your CRM
This week we break down the two attack playbooks ShinyHunters running right now, and what happened when they ran them against Medtronic, Allianz Life, and Ameriprise.
👋 Welcome to Unlocked
You've heard of ShinyHunters.
Ticketmaster. AT&T. Santander. A billion records across six years of operation.
What you may have missed is that they've completely changed how they operate — and the new method is specifically designed to beat the controls most security teams put in place after 2024.
This week we break down the two attack playbooks they're running right now, and what happened when they ran them against Medtronic, Allianz Life, and Ameriprise.
🔑 Who Is ShinyHunters?
ShinyHunters emerged around 2019 as a mass data theft operation — the kind that breaks into databases, vacuums up credential records, and sells them on dark web forums. Unglamorous, effective, highly profitable.
They graduated. Fast.
By 2024, they had become the primary threat actor behind one of the most consequential supply chain campaigns ever documented. They identified that Snowflake — a cloud data warehouse used by hundreds of enterprise companies — was being accessed by employees whose credentials had been harvested by infostealer malware. No zero-days. No sophisticated exploits. Just stolen usernames and passwords, and the absence of multi-factor authentication on those Snowflake accounts.
The results were staggering. At least 165 organizations were breached through this single campaign. Ticketmaster, AT&T, Santander, LendingTree, Advance Auto Parts, Neiman Marcus — the victim list reads like a Fortune 500 roll call. AT&T ultimately paid $370,000 in ransom just to have a group member delete the stolen data. Ticketmaster faced class-action lawsuits, congressional scrutiny, and a stock drop that the parent company is still managing.
That was the old playbook. Full victim timeline →
📉 The Numbers
- 1B+ individual records attributed to ShinyHunters across their entire operation
- 165 organizations breached in the 2024 Snowflake campaign alone
- 560M Ticketmaster customer records exposed — one of the largest consumer data breaches ever
- 110M AT&T wireless customers had their call records stolen
- 300–400 companies targeted through their 2026 Salesforce Experience Cloud campaign
- $65M — the ransom demanded from TELUS Digital after ShinyHunters claimed nearly 1 petabyte of stolen data
- 7 major organizations breached in roughly six weeks across 2026 — ADT, Udemy, Rockstar Games, Zara/Carnival/7-Eleven, Medtronic, Allianz Life, Ameriprise
🔍 The New Playbook: They're Not Breaking In. They're Calling In.
Here's what changed.
After the Snowflake campaign, ShinyHunters didn't slow down — they evolved. Researchers at Google's Threat Intelligence Group formally documented the shift: the group had pivoted from credential stuffing and supply chain database theft toward a more scalable, more human, and frankly more alarming approach.
Playbook 1: Vishing for SSO credentials.
An employee receives a call from someone claiming to be internal IT support. The call is professional. The caller ID is spoofed. The caller has just enough internal context — your name, your team, the software you use — to sound legitimate. They tell you there's a sync issue with your account and walk you through "resolving it" by approving an MFA prompt or providing a one-time code.
That's it. That's the breach.
Once the attacker has those credentials, they're not in your system — they are your system. They enroll new MFA devices, authenticate as you, and walk laterally through every SaaS platform your SSO connects to: Salesforce, Microsoft 365, Google Workspace, Slack, Atlassian, SAP, Zendesk. The corporate CRM — the one that holds every customer name, contract value, and support ticket — is typically the first stop.
ADT discovered this in April 2026, when ShinyHunters impersonated IT support, phished an employee's Okta SSO credentials, and extracted over 10 million customer records directly from ADT's Salesforce instance. No malware. No zero-day. One phone call. Full breakdown of the ADT breach →
Playbook 2: AuraInspector and the Salesforce misconfiguration sweep.
Starting in September 2025, ShinyHunters began targeting Salesforce Experience Cloud environments at scale using a modified version of AuraInspector — an open-source security audit tool — to automatically scan public-facing Salesforce sites for misconfigured guest user profiles with excessive permissions.
When a Salesforce Experience Cloud site is misconfigured, unauthenticated guest users can access far more data than intended. ShinyHunters weaponized this at industrial scale. By March 2026, they claimed to have breached between 300 and 400 organizations through this method alone — including McGraw Hill (13.5 million records), Cisco (3 million records containing PII tied to FBI, DHS, IRS, and NASA procurement), and the European Commission (350 GB of internal data). BleepingComputer's coverage of the Salesforce campaign →
These two playbooks share one core characteristic: neither requires breaking anything. They require finding what's already unlocked.
🎯 One Breach a Week: The Assembly Line
Here's what makes ShinyHunters genuinely different from most threat actors: they don't stop between breaches. They treat data exfiltration like a production operation.
Look at the 2026 timeline alone. In April, they hit ADT — 10 million customer records via a single vishing call to an Okta SSO user. Days later, Udemy — 1.4 million records, same vishing method, same Salesforce exfiltration chain. Then Rockstar Games — 78 million records via a stolen analytics token, leaked publicly after the studio refused to pay ransom. Then Zara, Carnival, and 7-Eleven simultaneously — a coordinated "pay or leak" ultimatum across three global brands at once. Then Medtronic — 9 million records from one of the world's largest medical device companies. Then Allianz Life and Ameriprise. Then Instructure — their second breach in eight months.
That's seven major organizations in roughly six weeks. Each one a household name. Each one a different industry. Each one breached using a variation of the same two playbooks.
This is the part that should concern your leadership team more than any individual breach: ShinyHunters has industrialized the attack. They're not selecting targets based on vulnerability research or deep reconnaissance. They're running the playbook repeatedly, at volume, and waiting to see who hasn't closed the gap. The Salesforce misconfiguration sweep literally automated the target selection — AuraInspector scanned hundreds of organizations and flagged the ones with open doors. ShinyHunters just walked through them in sequence.
It's not a campaign. It's a conveyor belt. And it's still running.
🛡️ What This Means for Your Access Layer
The ShinyHunters story is often told as a ransomware story, or a data theft story, or a corporate espionage story. It's all of those things. But for practitioners running identity and access controls, there's a simpler and more actionable frame:
Every breach in the ShinyHunters playbook begins with a single legitimate credential.
Not a zero-day. Not an unpatched system. A username and password — or an approved OAuth token — that belonged to a real employee or sat dormant in a third-party integration. The attacker's entire operation is downstream of that single moment of access.
That means the controls that actually matter here are identity-layer controls:
Phishing-resistant MFA
Standard push-notification MFA is now a liability in the ShinyHunters threat model. Their vishing campaigns are specifically designed to socially engineer employees into approving MFA prompts or reading out one-time codes. Hardware-bound credentials and passkeys — which require physical possession of the authenticating device — break this attack chain entirely. There is no phone call that tricks a passkey. For a deeper look at why identity is now the primary battlefield, see Edition #32: The $20 Billion Login.
SaaS OAuth token auditing
ShinyHunters' Salesforce campaign ran for months — from September 2025 through at least March 2026 — using stolen OAuth tokens to silently exfiltrate data from hundreds of connected organizations. Most of those organizations had no visibility into which third-party apps held active OAuth tokens with production data access. If you're not auditing your connected apps and revoking dormant tokens, you have blind spots that look exactly like this.
Salesforce guest user profile review
If your organization runs a Salesforce Experience Cloud site, this is the week to check your guest user profile permissions. The AuraInspector campaign exploits a configuration error — not a software flaw — and Salesforce has published specific remediation guidance. Varonis has a practical walkthrough of exactly what to check → The attack is preventable with a settings review that takes hours, not weeks.
Third-party access governance
The TELUS breach began with credentials stolen from Salesloft's GitHub environment. The Snowflake campaign began with infostealer-harvested credentials from employee machines. In both cases, the breach originated in the supply chain — not the target organization directly. Every third-party tool in your stack that holds an authenticated session into your systems is an extension of your attack surface. We covered this dynamic in depth in Edition #29. Treat it accordingly.
🔑 The Bottom Line
Patch Tuesday won't save you from this one.
ShinyHunters doesn't need a CVE. They need one employee to pick up a phone, or one Salesforce guest profile with too many permissions.
Check your OAuth tokens.
Check your Experience Cloud config.
And brief your help desk on what a vishing call sounds like — because your employees are currently the last line of defense, and most of them don't know it yet.
💡 Unlocked Tip of the Week
Ask your team this week: "If a ShinyHunters affiliate called one of our help desk staff right now and claimed to be an employee locked out of their account — what would happen?"
Walk through it honestly. Would the help desk ask for verification? What does that verification actually look like? Could it be spoofed with information available on LinkedIn? If the answer involves anything other than a hardware-bound credential or an in-person confirmation, that's the gap. It's not hypothetical — it's exactly how ADT lost 10 million records in April.
🔥 Final Takeaway
ShinyHunters didn't get more sophisticated. They got more patient — and they found that the controls most organizations put in place after 2024 have a consistent blind spot: the human on the other end of the phone.
A billion records. Seven major organizations in six weeks. Hundreds of Salesforce environments silently drained. None of it required a single novel exploit.
The organizations that come out of this threat cycle in better shape won't be the ones that patched fastest. They'll be the ones that made their identity layer impossible to social engineer — hardware-bound credentials, phishing-resistant MFA, and access controls that don't depend on an employee making the right call under pressure.
Because ShinyHunters is betting they won't.
Stay ready. Stay resilient.
Until next time,
The EveryKey Team
← Last Week: The Overnight Exploit: What Mythos Means for Your Access Layer
🙋 Author Spotlight
Meet Kevin Patel — Cybersecurity Researcher & Digital Risk Analyst
Kevin Patel brings a strategic eye to the evolving threat landscape, specializing in how emerging technologies change the "math" of digital risk. With a background in threat intelligence and identity security, Kevin focuses on bridging the gap between technical vulnerabilities and the human psychology that attackers weaponize. He believes that in 2026, the only way to beat machine-speed fraud is through cryptographically-backed trust and relentless anomaly detection.