A Deep Dive into Privileged Access Governance Strategies

Why Privileged Access Governance Is a Top Security Priority
Privileged access governance (PAG) is the ongoing framework of policies, processes, and controls that ensures users and accounts retain only the minimum level of access required for their current role — and that this access is continuously reviewed, certified, and revoked when no longer needed.
In plain terms, PAG answers three questions at all times:
- Who has elevated access to critical systems right now?
- Should they still have it, given their current role?
- What did they do with it, and can you prove it to an auditor?
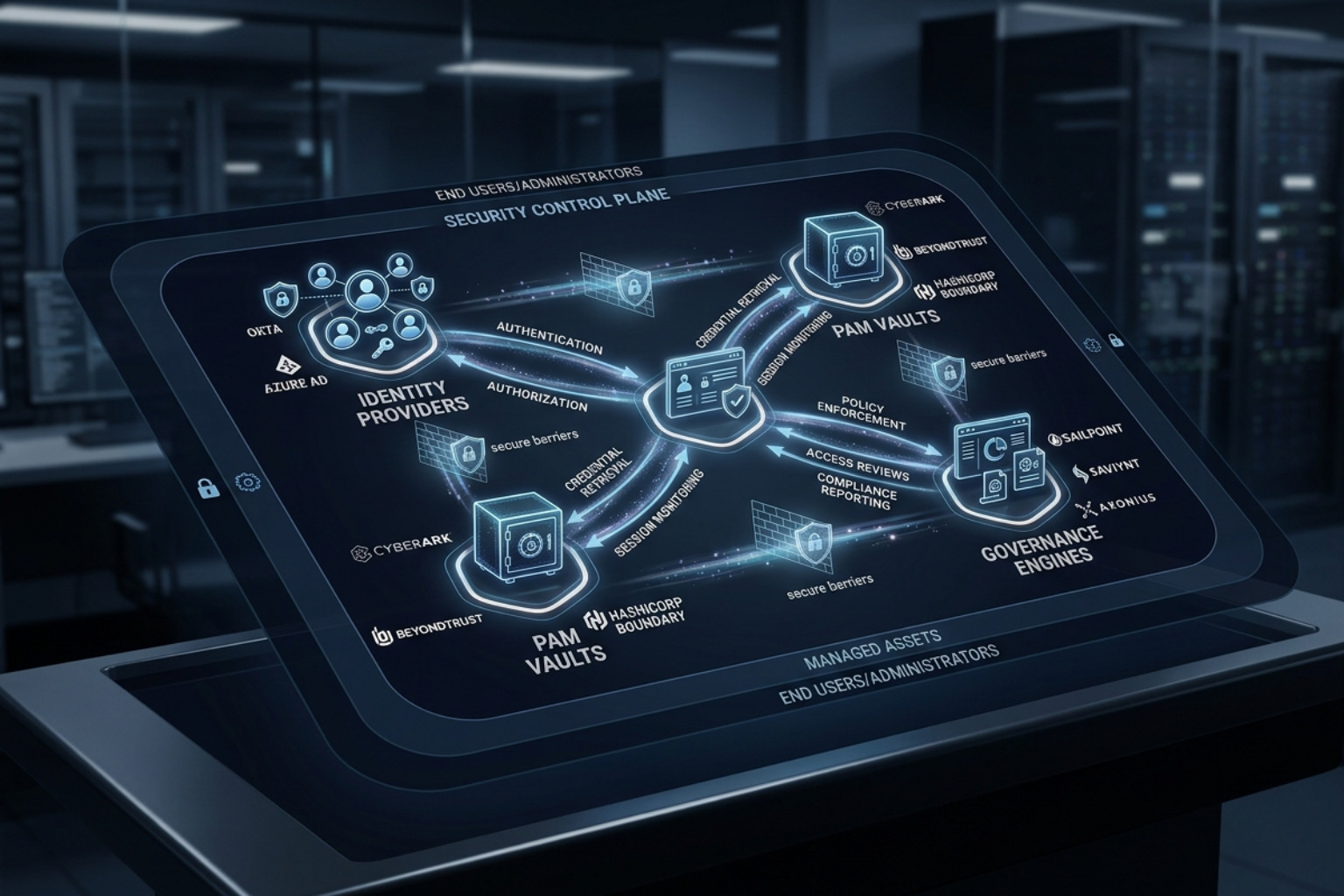
PAG sits at the intersection of two disciplines that organizations often run as separate silos: Privileged Access Management (PAM), which handles the technical controls like password vaulting and session recording, and Identity Governance and Administration (IGA), which handles the policy, lifecycle, and compliance layer. PAG is what happens when you bridge those two together.
The stakes are high. According to the Verizon Data Breach Investigations Report, 68% of data breaches involve a human element — misuse, misconfiguration, or mishandled credentials. Meanwhile, Microsoft processes over 8 trillion security signals per day, a figure that underscores just how relentlessly privileged accounts are probed and targeted.
What makes privileged access especially dangerous is the gap between when access is granted and when it is revoked. Users accumulate permissions over time — through role changes, project assignments, and one-off admin requests — without systematic review. This is called privilege creep, and it silently expands your attack surface.
Without a governance layer, even a well-configured PAM solution leaves a critical question unanswered: should this person still have this access at all?
This guide is written for security engineers, IT administrators, and CISOs who need to build or mature a PAG program — covering framework design, IGA integration, cloud environments, automation, and compliance alignment.
Defining Privileged Access Governance (PAG) vs. PAM
In the security world, we often use acronyms interchangeably, but when it comes to What Is Privileged Access Management and privileged access governance, the distinction is vital. Think of PAM as the "how" and PAG as the "why" and "who."
PAM focuses on the technical enforcement layer. It provides the vault to store credentials, the proxy to record sessions, and the rotation mechanism to change passwords every 24 hours. However, PAM by itself is often blind to the business context. It doesn't know if a Database Administrator (DBA) who was transferred to the Marketing department yesterday should still have "root" access to the SQL server today.
This is where privileged access governance steps in. It provides the strategic oversight, ensuring that the technical controls align with organizational policy. PAG is concerned with the historical review, the attestation (certification) of access, and the overall risk scoring of an identity.
Comparison: PAM Technical Controls vs. PAG Strategic Oversight
| Feature | PAM (Technical Controls) | PAG (Strategic Oversight) |
|---|---|---|
| Primary Goal | Secure and monitor active sessions | Validate and govern access rights |
| Key Mechanism | Credential Vaulting, Session Recording | Policy Enforcement, Access Certification |
| Focus Area | Real-time execution | Lifecycle and historical review |
| Compliance Role | Audit trails and session logs | Attestation and evidence of review |
| Handling Changes | Password rotation | Automated provisioning/deprovisioning |
PAG moves the organization toward a post-access governance model. It isn't just about granting the key; it's about checking the lock every quarter to see if the keyholder still works there. This includes evaluating risk assessments and scoring based on behavior—if a privileged user suddenly begins accessing systems they haven't touched in years, PAG frameworks flag this as a governance violation.
Core Components of a Modern PAG Framework
A robust PAG framework isn't built on a single tool but on a series of integrated processes that manage the lifecycle of a privileged identity from "creation to closure." To effectively mitigate risks, organizations must move away from "standing privileges"—where an admin has 24/7 access—and toward a model of Zero Standing Privileges (ZSP).
Key components include:
- Request-Release Mechanisms: Instead of having permanent access, users must request permissions for a specific window. This is often paired with Multi-party Approval (Dual Control), where a second authorized individual must sign off on the request before access is granted.
- Entitlement Management: This involves mapping exactly what a "privileged" role entails. It’s not enough to say someone is an "Admin." You must define the granular entitlements (e.g., can they read logs, or can they delete the database?).
- Lifecycle Automation: This handles "Joiner, Mover, Leaver" (JML) logic. When an employee changes departments (a "Mover"), the PAG system should automatically trigger a review of their privileged rights to prevent Managing Privileged User Access And Security Risks associated with legacy permissions.
Just-In-Time (JIT) Access Workflow
The gold standard of PAG is Just-In-Time access. In this workflow, an identity has zero permissions by default. When a task arises, the user requests elevated rights. The system validates the request against policy, perhaps checks a ticket in an ITSM tool (like ServiceNow or Jira), and grants a temporary, ephemeral token. Once the time limit expires, the access is automatically revoked.
Automating Privileged Access Governance Reviews
One of the biggest Privileged Access Management Benefits For Enhanced Security is the elimination of manual, spreadsheet-based access reviews. Manual reviews are prone to "rubber-stamping," where managers simply click "Approve All" because the list is too long to read.
Automation enhances PAG by:
- Triggering Recertification Cycles: Automatically sending review requests to resource owners every 90 days.
- Evidence Collection: Generating audit-ready reports for frameworks like NIST 800-53, ISO 27001, and SOC2.
- Reducing Script Reliance: Replacing fragile, custom-written PowerShell or Python scripts with standardized API-driven workflows.
Strategic Integration: IGA, Cloud, and Hybrid Models
In the modern enterprise, the "Control Plane" has shifted to the cloud. Governing access to a Windows Server in a basement is one thing; governing permissions across AWS, GCP, and Microsoft Entra ID is another.
Modern PAG must address Cloud Infrastructure Entitlement Management (CIEM). In cloud environments, permissions are often granted through complex combinations of Roles, Policies, and Service Control Policies (SCPs). A PAG strategy ensures these don't conflict and that "Shadow Admin" accounts aren't created through permission escalation.
The Role of Privileged Access Governance in IGA
PAG acts as the bridge that connects high-level Identity Governance and Administration (IGA) with deep-level PAM. Without this integration, identity silos form. The HR system might know an employee has left (IGA), but the "root" password on a legacy Linux box might never get changed (PAM).
Integrating PAG into your IGA strategy allows for:
- Segregation of Duties (SoD) Conflict Detection: Ensuring the person who requests a payment cannot also be the person who approves it.
- 360-Degree Visibility: A single pane of glass to see standard user access and privileged access side-by-side.
- Non-Human Identity (NHI) Governance: Managing the "secret" keys used by service accounts and APIs. These accounts often have high privileges but are rarely reviewed, making them a prime target for lateral movement.
For organizations heavily invested in the Microsoft ecosystem, Azure Privileged Identity Management (PIM) serves as a primary example of how governance can be baked directly into the identity provider to manage JIT access and role elevation.

Overcoming Implementation Challenges and Best Practices
Deploying privileged access governance is rarely a "set it and forget it" project. Organizations often face resistance from IT staff who find JIT workflows "too slow" or encounter legacy systems that don't support modern API-based governance.
Common Challenges
- Privilege Creep: The gradual accumulation of access rights as users move through different roles.
- Legacy Systems: Older mainframes or proprietary hardware that doesn't integrate with MFA or modern PAM vaults.
- Stakeholder Buy-in: Convincing senior leadership that the "friction" of a request-approval workflow is worth the security gain.
Best Practices for Success
- Phased Deployment: Don't try to govern every account at once. Start with your "Tier 0" assets—Domain Controllers, Root Cloud Accounts, and Core Financial Databases.
- Enforce MFA Everywhere: Multi-factor authentication is the baseline. No privileged session should ever start without a second factor.
- Continuous Auditing: Don't wait for the quarterly review. Use behavioral analytics to flag anomalies (e.g., an admin logging in from an unusual IP at 3 AM).
- Regulatory Alignment: Map your PAG controls directly to GDPR, HIPAA, or SOX requirements to ensure that when the auditors arrive, the data is already organized.
You can explore more specific strategies in our Tag/Privileged Access Management section.
Frequently Asked Questions about Privileged Access Governance
How does PAG differ from standard Identity Governance?
Standard Identity Governance (IGA) manages the lifecycle of all users (onboarding, email access, basic apps). PAG is a specialized subset that focuses specifically on high-risk, "privileged" accounts that have the power to change configurations, access sensitive data, or bypass security controls.
What are the primary triggers for an out-of-cycle access review?
While most reviews are scheduled (quarterly/annually), certain events should trigger an immediate review:
- Employee termination or resignation.
- A department transfer ("Mover" event).
- Detection of a security incident involving that account.
- A significant change in the system's risk profile (e.g., moving a database to the public cloud).
How does PAG enforce Just-In-Time (JIT) access and ephemeral tokens?
PAG tools integrate with the Identity Provider (IdP) to grant permissions only when a valid request is approved. Instead of a permanent password, the system might issue a short-lived token or a dynamic SSH key that expires automatically after the session ends, leaving no "standing" credentials for an attacker to steal.
Conclusion
As the threat landscape evolves toward more sophisticated, human-operated ransomware and credential theft, the "set it and forget it" approach to admin rights is no longer viable. Privileged access governance provides the necessary framework to ensure that high-trust access is never permanent and always justified.
By advancing your Zero Trust maturity through PAG, you move beyond simple password management and toward a holistic model of identity security. This not only protects your most critical assets but also streamlines compliance and reduces the manual burden on your IT teams.
For more on how to centralize these efforts, see our guide on Identity Manager: Centralizing User Access and Governance in the Enterprise.




