The Best Practices for Effective Application Authentication in 2026
A practical guide for IT professionals on modern application authentication methods, token security, and secure user access for web apps and APIs.

Securing Modern Web Apps and APIs
Application authentication is a foundational component of modern application security. As organizations deploy web apps, mobile apps, and distributed systems across cloud infrastructure, verifying a user’s identity before granting access has become essential.
This guide is intended for developers, IT professionals, and security architects seeking to understand and implement secure authentication in modern web applications and APIs. Effective authentication is critical for protecting sensitive data, ensuring regulatory compliance, and maintaining user trust in digital services.
Users authenticate to access secure systems using a variety of methods, and evolving technologies such as biometrics, multi-factor authentication, and adaptive authentication are enhancing this process.
Application authentication is the security process of verifying the identity of a user, device, or system trying to access an application. Authentication protects data integrity by confirming identity, which prevents unauthorized modification or theft of sensitive information.
Authentication prevents unauthorized access by stopping unauthorized users, malicious actors, and bots from accessing systems. Strong authentication is critical for modern access control and helps organizations meet compliance requirements tied to privacy, data protection, and auditability.
Modern authentication must do more than verify credentials; it needs to provide secure access and support frictionless user experiences.
Introduction to Authentication
Authentication is the cornerstone of digital security, ensuring that only legitimate users can gain access to web apps, APIs, and other protected resources. In the rapidly evolving landscape of modern apps, user authentication has become more sophisticated, moving beyond simple passwords to embrace a variety of authentication methods. Today’s modern authentication strategies include multifactor authentication (MFA), passwordless logins, and biometric verification, all designed to provide secure access while maintaining a seamless user experience.
Modern web apps must balance robust security with usability, supporting industry standard protocols such as OAuth 2.0 and OpenID Connect to verify identity and grant access efficiently. These protocols enable developers to implement secure authentication flows that protect sensitive data and streamline user management. Solutions like Frontegg empower engineering teams to quickly deploy secure, scalable login systems, ensuring that authentication keeps pace with the demands of distributed systems and cloud infrastructure. By adopting modern authentication methods, organizations can safeguard user identities and maintain trust in their digital services.
This guide is intended for developers, IT professionals, and security architects seeking to understand and implement secure authentication in modern web applications and APIs. Effective authentication is critical for protecting sensitive data, ensuring regulatory compliance, and maintaining user trust in digital services.
Application Authentication
Application authentication validates credentials like passwords, biometrics, or tokens (MFA) to ensure only legitimate users gain access. Application authentication methods are categorized by what a user knows, has, or is.
Multiple authentication methods are often combined to enhance security and user flexibility.
Modern application authentication strategies often combine methods into Multi-Factor Authentication (MFA) to balance security and usability. Authentication secures user accounts against credential theft, which is a primary goal for attackers trying to gain system access.
Seamless access is a key goal of modern authentication systems, providing users with a smooth and uninterrupted experience while maintaining strong security.
Using a single factor, especially a knowledge-based one, is no longer considered sufficient for sensitive systems.
Secure, robust authentication methods, such as Multi-Factor Authentication (MFA), build trust by ensuring that only verified entities interact with the application.
Modern user authentication is evolving to address sophisticated threats like phishing and identity sprawl.
Authentication Methods
Common application authentication methods include:
- Password-based authentication
- Multi-Factor Authentication (MFA)
- Biometric scans
- API keys for machine-to-machine communication
- Certificate-based authentication
Password-Based Authentication
Password-based authentication is the most familiar and widely used method for web applications. However, traditional passwords alone are vulnerable to phishing and credential theft.
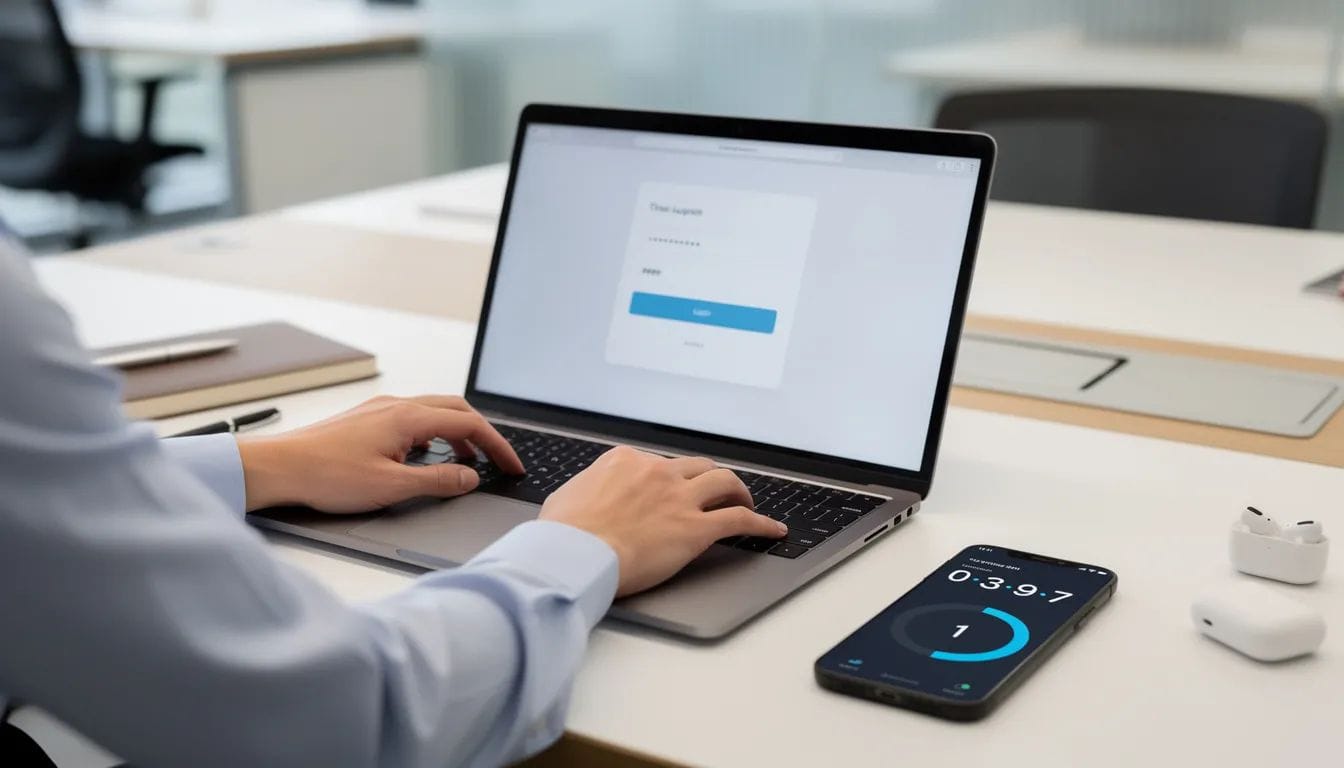
Multi-Factor Authentication
Modern authentication relies on a combination of factors to verify a user's identity, which fall into three main categories: something you know, something you have, and something you are.
Hardware keys offer maximum security but require physical management by the user.
Passwords and basic SSO are cost-effective and easy to deploy, while biometric systems and hardware tokens incur higher initial costs.
Combining methods, such as SSO with MFA, is considered the optimal balance between security and streamlined workflow.
Biometric Authentication
Biometric authentication uses unique physical characteristics, such as fingerprints or facial features, as identity credentials, and modern biometrics for authentication provide a secure and convenient alternative to passwords.
Biometric authentication is increasingly utilized for its security and user-friendly experience, with modern biometric systems transforming secure identity verification.
However, biometric systems can fail due to environmental factors or physical changes, necessitating a fallback method, usually a password.
Biometric data must be protected carefully because it represents permanent personal identifiers.
Token-Based Authentication
JSON Web Tokens are widely used in token-based authentication systems.
Token-based authentication is the go-to method for modern web apps and APIs. Token-based authentication methods, such as JWT, are foundational for stateless API security.
Tokens are signed and time-bound, supporting scalable, secure sessions across APIs and web apps. JWT tokens are signed by the identity provider using a private key, and the application verifies the token's authenticity using the corresponding public key, which is typically retrieved from the JWKS URI.
Token-based authentication is commonly used in modern web applications, allowing users to authenticate once and receive a token for subsequent requests. During token acquisition, the token endpoint is the URL where applications exchange authorization codes or credentials for tokens such as access tokens, ID tokens, and refresh tokens.
The token format contains identity claims that enable the server to validate user access without requiring session storage. The session ID should be long (128 bits) and generated randomly to avoid brute force attacks.
Certificate-Based Authentication
Certificate-based authentication uses digital certificates issued by trusted authorities to verify identity.
Certificate-based authentication relies on a trusted certificate authority and cryptographic keys to verify identity during authentication.
This approach is widely used in enterprise systems where strong authentication and mutual authentication are required, though it must be designed carefully to avoid common multi factor authentication vulnerabilities.
Identity Provider
An identity provider plays a central role in modern authentication architectures. Authentication solutions often need to support both internal users and external users, providing flexibility in managing access.
OpenID and OpenID Connect
OpenID is an HTTP-based protocol that utilizes an identity provider (IDP) to validate a user. OpenID Connect is an identity layer built on top of OAuth 2.0 that enables applications to verify a user’s identity and receive user profile information. OpenID is an HTTP-based protocol that utilizes an identity provider (IDP) to validate a user.
SAML
SAML allows identity providers to securely transmit authentication and authorization data to service providers. SAML (Security Assertion Markup Language) is an XML-based open standard used primarily for SSO in enterprise environments. In SAML-based SSO, the service provider is the application that relies on the identity provider for authentication claims.
SAML is often the choice for many commercial applications, while OpenID has dominated the consumer sector.
OAuth 2.0 and OpenID Connect
OAuth 2.0 and OpenID Connect are commonly used together to provide secure authentication and authorization. Active Directory is an enterprise-grade identity provider that supports centralized user management and integrates with systems via standard protocols like OAuth and LDAP.
The Microsoft identity platform supports both organizational accounts and Microsoft personal accounts. Personal accounts are a special kind of account, similar to a large Azure AD tenant with exceptions, which can affect authentication and access scenarios.
When using the Microsoft identity platform, the process of app registration in Azure Active Directory (Azure AD) is a foundational step for enabling authentication flows. This includes configuring redirect URIs, supported account types, and other essential settings within the Azure portal.
Multi Factor Authentication
Multi factor authentication adds additional authentication factors beyond a password, and modern MFA platforms and insights continue to evolve to address emerging threats.
Multi-factor authentication combines two or more authentication factors to enhance security and reduce the risk of unauthorized access, going beyond passwords alone to provide the benefits of multifactor authentication in modern security.
Multifactor authentication strengthens security by requiring users to pass multiple verification steps, which is especially important for MFA solutions securing remote workers.
MFA dramatically reduces the risk of unauthorized access, especially when layered with device verification or location awareness.
Multi-factor authentication is becoming a standard for applications that handle sensitive data, with a wide range of multi factor authentication use cases across regulated industries.
Implementing strong authentication is crucial for securing modern web applications, and organizations increasingly rely on multi-factor authentication for enhanced security.
API Token
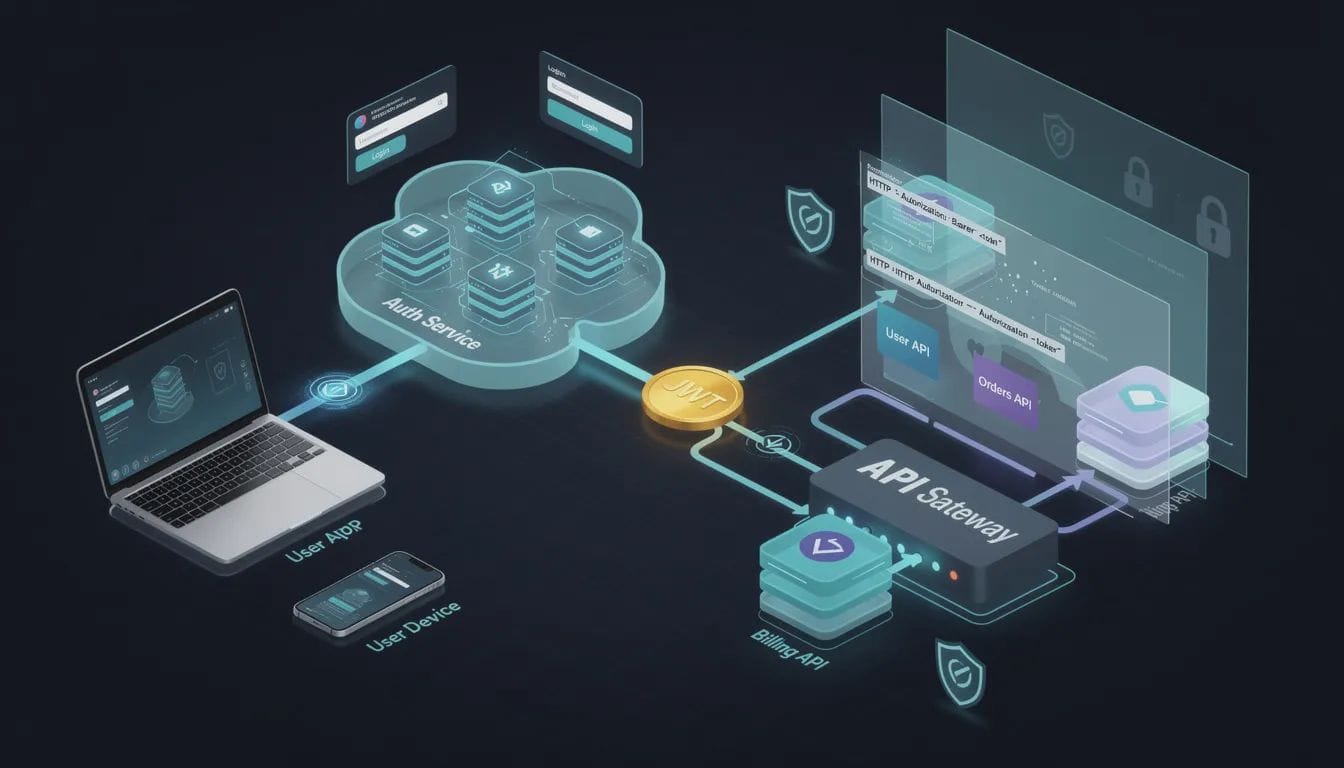
API tokens are used for machine-to-machine authentication.
An API token allows a service to access protected resources on a user's behalf or on behalf of an application, making secure handling crucial in delegated scenarios, just as authenticator apps protect online accounts in user-facing MFA flows.
Token-based authentication methods are particularly effective in modern web applications, especially single-page apps and APIs.
Applications send tokens in an authorization header during subsequent requests to verify access.
Short lived access tokens help reduce security risks by limiting the lifespan of credentials.
Refresh tokens allow applications to request new access tokens without forcing users to log in again.
Access Control
Access control determines whether authenticated users can perform specific actions within an application.
Strong access security control policies ensure that only authorized users can access sensitive operations and protected resources.
Authentication enables accountability, ensuring that all actions taken within the system can be traced back to a specific, verified user.
Strong authentication is critical for modern access control.
Authentication Factors
Authentication factors represent the different ways users verify their identity, and two-factor verification highlights how combining them strengthens account security in a high-threat world.
Application authentication methods are categorized by:
- Something you know: passwords or PIN codes
- Something you have: a mobile device, hardware key, or authenticator app
- Something you are: biometric data such as fingerprints or facial recognition
Multi-factor authentication combines multiple factors to strengthen verification and reduce security risks, making factor authentication a key to modern account security.
Based Authentication
Certificate-based authentication uses digital certificates issued by trusted authorities to verify identity.
Certificate-based authentication relies on a trusted certificate authority and cryptographic keys to verify identity during authentication.
This approach is widely used in enterprise systems where strong authentication and mutual authentication are required, though it must be designed carefully to avoid common multi factor authentication vulnerabilities.
Granting Access
Authentication is only the first step in granting access to protected resources.
The authentication server validates credentials and verifies identity before granting access to applications, APIs, or data.
Once authentication succeeds, the system issues an access token or session identifier that allows the user to access protected resources.
The authorization code flow is commonly used to call a web API from a web app on behalf of a user, storing acquired tokens in a token cache. Confidential client applications, such as daemon apps or web APIs, require a client secret to securely acquire tokens, while public client applications like single-page apps using PKCE typically do not.
OAuth 2.0 is an authorization protocol that allows applications to access user resources without exposing credentials, issuing short-lived access tokens for delegated access.
Authentication flows involve acquiring tokens on behalf of signed-in users or daemon apps that acquire tokens on behalf of themselves with no user, and they increasingly incorporate the future of passwordless, biometric, and adaptive identity solutions.
Multifactor Authentication
Single sign-on (SSO) provides seamless, centralized authentication across multiple applications by allowing users to authenticate once and gain access to all connected services without re-entering credentials. This approach simplifies user authentication management by centralizing control of access permissions and security policies through a trusted identity provider, and following single sign-on best practices helps maintain both security and usability.
Multifactor authentication plays a major role in protecting modern applications.
Strong authentication methods significantly reduce the risk of compromised credentials and account takeover attacks.
While SSO prioritizes convenience, it can create a single point of failure if the master account is breached.
Combining single sign-on with MFA is often considered the optimal approach for enterprise access management, which is why many organizations deploy a centralized single sign-on portal.
Modern Apps
Modern web applications operate across cloud infrastructure and distributed systems.
Single-page applications (SPAs) acquire tokens by a JavaScript or TypeScript app running in the browser, often using frameworks like Angular, React, or Vue. The user's browser plays a key role in storing session cookies, managing tokens, and interacting with identity providers during login flows.
Modern web applications rely heavily on OAuth 2.0 and OpenID Connect for secure authentication. Establishing and verifying a user's identity through tokens and identity claims is essential in these authentication protocols.
The Microsoft identity platform supports authentication for different kinds of modern application architectures based on OAuth 2.0 and OpenID Connect.
Modern authentication systems must adapt to complex use cases without compromising user experience. Session security is crucial for creating secure web applications, and Bluetooth-based MFA devices demonstrate how Bluetooth MFA is changing authentication while preserving usability. All session-based applications should use HTTPS communication.
Adaptive authentication methods are being implemented to provide context-aware security measures.
The future of authentication includes AI-powered security and quantum-resistant encryption.
Net Core
Modern enterprise applications frequently use .NET Core to build scalable web applications and APIs.
.NET Core supports OAuth 2.0, OpenID Connect, and token-based authentication workflows for secure user authentication and authorization.
Developers often implement authentication middleware within .NET Core applications to handle identity verification, token validation, and secure session management.
Secure application authentication is essential for protecting sensitive systems and maintaining secure access to enterprise resources.
Modern access platforms are also exploring passwordless approaches. Solutions like EveryKey focus on simplifying access by verifying identity through trusted device presence and proximity, illustrating why every online account needs a multi-factor authentication app. This allows organizations to support Zero Trust access models where identity verification occurs continuously while users maintain a seamless experience.
Best Practices for Authentication
To implement secure authentication in modern web apps, it’s essential to follow best practices that minimize security risks and enhance the overall user experience.
Key Best Practices
- Use multiple authentication factors: Combine something the user knows (like a password), something they have (such as a security token or authenticator app), and something they are (biometric data like fingerprints or facial recognition). This layered approach significantly reduces the risk of unauthorized access, even if one factor is compromised.
- Implement token-based authentication: Use JSON Web Tokens (JWTs) or similar mechanisms to manage secure sessions across APIs and web apps. By issuing time-limited security tokens, applications can verify user credentials without exposing sensitive data or relying on persistent sessions.
- Enforce strong password policies: Require complex passwords, regular password changes, and prevent the use of common or compromised passwords.
- Utilize secure password storage techniques: Store passwords using strong hashing and salting algorithms.
- Protect client secrets: Ensure that secrets and credentials are never exposed in client-side code or public repositories.
- Regularly update authentication systems: Patch vulnerabilities and keep authentication libraries and dependencies up to date.
- Monitor user logs for suspicious activity: Set up alerts and monitoring to detect and respond to unauthorized access attempts.
By adhering to these best practices, developers can implement secure authentication that protects sensitive data, supports seamless user experiences, and meets the security requirements of modern web applications.
Conclusion
In summary, authentication is a vital element of modern web apps, serving as the first line of defense against unauthorized access to protected resources and sensitive data. By leveraging a range of authentication methods — including password-based, token-based, and biometric authentication — developers can tailor their security strategies to the unique needs of their applications. Implementing multifactor authentication, secure password storage, and token-based authentication not only strengthens security but also helps ensure compliance with industry standards.
Staying current with protocols like OAuth 2.0 and OpenID Connect is essential for maintaining secure and scalable authentication flows. Platforms such as Frontegg offer robust solutions for managing user authentication, enabling organizations to implement secure access controls efficiently. By prioritizing strong authentication practices, developers can protect user identities, prevent security breaches, and deliver a seamless, secure user experience in their modern web apps.
FAQ
What is application authentication?
Application authentication is the process of verifying the identity of a user, device, or system before granting access to an application.
What are common authentication methods for web applications?
Common methods include password authentication, multi-factor authentication, token-based authentication, biometric authentication, and certificate-based authentication.
Why is multi-factor authentication important for applications?
MFA reduces the risk of unauthorized access by requiring additional authentication factors beyond a password.
What is token-based authentication?
Token-based authentication allows users to authenticate once and receive a token that is used for subsequent requests to APIs or web applications.
What protocols are commonly used for modern application authentication?
Common protocols include OAuth 2.0, OpenID Connect, and SAML.