The Ultimate Framework for Scalable EDR Deployment Across Large Systems

Why EDR Scalability in Enterprise Environments Defines Your Security Posture
EDR scalability enterprise environments is one of the most pressing operational challenges facing security teams in 2026 — and the stakes have never been higher.
Here is what you need to know upfront:
| Factor | What It Means at Scale |
|---|---|
| Endpoint volume | 1,000+ devices demand automated deployment, not manual rollouts |
| Telemetry volume | Enterprise SOCs process up to 134,000 alerts per day |
| Architecture choice | Cloud-native EDR scales elastically; on-premises hits hard infrastructure limits |
| Agent overhead | Agents must stay below 7% CPU and 120 MB RAM to avoid production impact |
| Data retention | Storage costs compound fast — tiered policies are non-negotiable at scale |
| Integration | EDR must connect to SIEM, SOAR, and threat intel feeds without API bottlenecks |
The modern enterprise perimeter no longer exists. A hybrid workforce, multi-cloud infrastructure, and the steady growth of connected devices have pushed endpoint counts into the tens or hundreds of thousands at large organizations. Every one of those endpoints is a potential entry point.
Traditional antivirus cannot keep up. It matches known signatures — and today's attackers use fileless malware, living-off-the-land techniques, and zero-day exploits specifically designed to bypass it. EDR solves this by continuously collecting behavioral telemetry, baselining normal activity, and detecting Indicators of Attack (IOA) — the intent behind an action, not just its fingerprint.
But detection capability alone is not enough. An EDR platform that works for 500 endpoints will not automatically work for 50,000. The architecture, the agent design, the backend infrastructure, and the data pipeline all need to be engineered for scale — or your security posture degrades exactly when your organization needs it most.
This guide gives security engineers, IT administrators, and CISOs a practical framework for evaluating, deploying, and managing EDR at enterprise scale — without the vendor hype.
Core Challenges of EDR Scalability Enterprise Environments

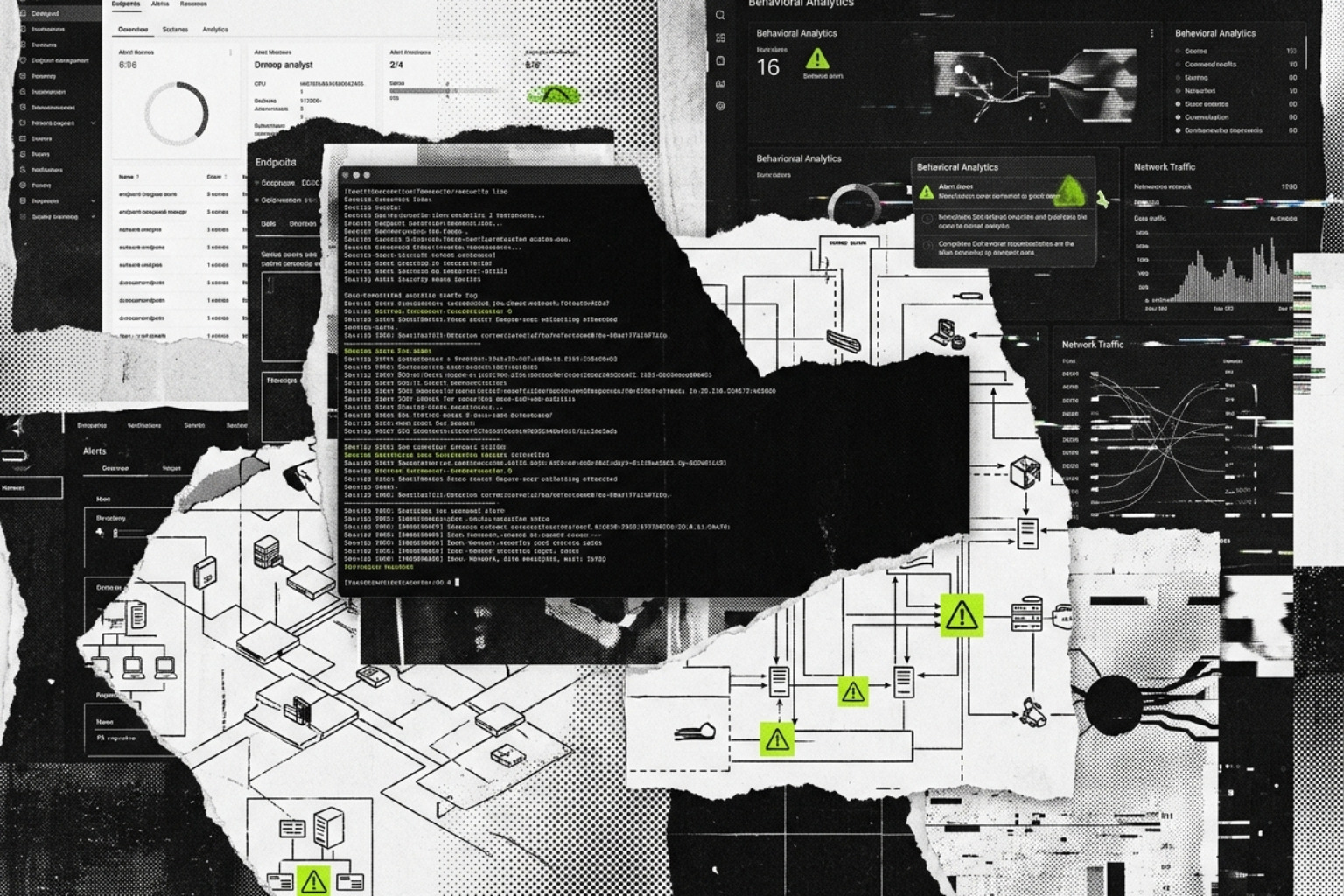
When scaling EDR, the first wall most organizations hit is not technical—it is operational. A Security Operations Center (SOC) in a global enterprise can face between 24,000 and 134,000 alerts daily. Research indicates that only about 0.01% of these alerts correspond to actual attacks, yet 64% of security teams report being overwhelmed by false positives. This "alert fatigue" is the primary reason breaches go undetected for months; the signal is simply buried in the noise.
Beyond the human element, technical bottlenecks often occur at the sensor and ingestion levels.
- Agent Performance: In large-scale environments, a poorly optimized agent can cripple production. Kernel-level sensors offer deep visibility but carry the risk of system instability (e.g., BSODs), while user-space sensors are safer but may miss low-level kernel exploits.
- Telemetry Ingestion: Moving billions of events from endpoints to a central console creates massive bandwidth and processing demands. Innovations like GraphWeaver: Billion-Scale Cybersecurity Incident Correlation attempt to solve this by using geo-distributed graph mining to correlate alerts before they reach the analyst's screen.
- Compliance and Data Sovereignty: For global enterprises, EDR scalability enterprise environments must account for GDPR and HIPAA. You cannot simply pipe all telemetry to a single global bucket; data residency requirements often mandate localized clusters or specific regional storage nodes.
Architectural Foundations for High-Volume Telemetry
The debate between on-premises and cloud-native architecture is settled for most large enterprises: cloud-native is the only way to achieve true elastic scale. However, understanding the underlying mechanics is vital for those managing hybrid environments or highly regulated air-gapped sectors.
Modern EDR backends typically utilize a microservices architecture, often orchestrated via Kubernetes, to allow for linear scaling of analytic throughput. For on-premises survivors, the Carbon Black EDR Architecture and Sizing provides a blueprint for horizontal scaling. This involves:
- Primary Nodes: Managing metadata, threat intelligence feeds, and the central console.
- Minion (Indexer) Nodes: Handling the heavy lifting of event data storage and indexing.
- Storage Technologies: Many platforms rely on Apache Solr for rapid event searching and Postgres for management databases.
| Feature | On-Premises EDR | Cloud-Native EDR |
|---|---|---|
| Scaling Mechanism | Manual hardware provisioning | Automated, elastic microservices |
| Maintenance | High (Patching, DB tuning) | Low (SaaS-managed) |
| Data Retention | Limited by physical disk space | Virtually unlimited (at a cost) |
| Performance | Can hit 10.5 TB per server limits | Scales across global data centers |
Evaluating Vendor Performance for EDR Scalability in Enterprise Environments
Selecting a vendor for a 50,000-endpoint rollout is vastly different than picking one for a small business. You need to look past the UI and evaluate the "plumbing." Key metrics include API rate limits—essential for SOAR integration—and throughput benchmarks. The Ultimate Guide To Cybersecurity Tools For Modern Organizations/ highlights that the best tools provide "zero-touch" deployment capabilities, allowing agents to be pushed via SCCM or Intune without user intervention.
Pricing also shifts at scale. While a basic EDR might cost $50-$100 per seat for small teams, enterprise pricing for 5,000+ endpoints often involves custom quotes with 20-40% volume discounts.
CrowdStrike Falcon and Zero-Touch Deployment
CrowdStrike remains a benchmark for EDR scalability enterprise environments due to its single-agent architecture. By avoiding "agent bloat," it maintains a lightweight footprint across Windows, macOS, and Linux. Its Linux-first design is particularly relevant in 2026, as cloud workloads increasingly rely on eBPF-based telemetry for high-fidelity monitoring without the stability risks of traditional kernel modules. Learn more about their positioning in the Best Cybersecurity Software Of 2026 Top 12 Tools For Endpoint Network Identity Protection/.
Microsoft Defender XDR and Billion-Scale Correlation
Microsoft leverages its massive footprint to perform billion-scale correlation through geo-distributed computation. By integrating EDR with identity (Entra ID) and email (Defender for Office 365), it creates a unified fabric. For enterprises, the distinction between Plan 1 (preventative) and Plan 2 (full investigation/hunting) is critical for budget mapping. Its integration with Microsoft Sentinel provides a cohesive ecosystem, as detailed in our guide to the Best Security Platform Of 2026 A Complete Guide To Unified Cloud Native Protection/.
SentinelOne and Autonomous AI for EDR Scalability in Enterprise Environments
SentinelOne's "ActiveEDR" approach focuses on reducing the workload of the SOC through autonomous AI. Its Storyline technology automatically stitches together related events into a single visual narrative, which significantly lowers the Mean Time to Respond (MTTR). In 2026, the addition of Purple AI allows analysts to use natural language queries to hunt through petabytes of data, a feature explored in the Best Security Solution Of 2026 Cybersecurity Platforms And Strategies For Modern Enterprises/.
Strategic Implementation for EDR Scalability in Enterprise Environments
Successful deployment follows a rigid, phased approach. You cannot "flip a switch" on 100,000 devices without risking a network-wide outage.
- Preparation & Assessment: Inventory every asset. Use Infrastructure-as-Code (IaC) tools like Ansible or Terraform to ensure consistent configurations.
- Pilot Phase (10-20%): Deploy to a representative sample of devices in "detect-only" mode. This allows you to capture telemetry and tune out false positives without blocking legitimate business processes.
- Cluster Configuration: If using on-premises components, refer to Multiple Cluster Environments and Cluster Sizing guides to ensure your backend can handle the incoming load.
- Full Rollout & Optimization: Gradually move to "prevention" mode. Monitor for "exception sprawl"—where too many allow-listed items create blind spots for attackers to exploit.
Future Trends: XDR Integration and Agentic AI for 2026+
The future of EDR is its evolution into XDR (Extended Detection and Response). As noted in Enterprise XDR: 5 Critical Ways to Stop Threats, the goal is to break down silos between endpoint, network, and cloud telemetry.
Key trends for 2026 and beyond include:
- Agentic AI: Autonomous agents that don't just alert, but actively triage, investigate, and remediate threats across the cyber kill chain.
- OT/ICS Passive Monitoring: Scaling EDR into industrial environments requires a "do no harm" approach. Passive monitoring ensures safety systems aren't disrupted while still providing visibility into legacy OS vulnerabilities.
- Retrospective Security: The ability to apply new threat intelligence to old logs. If a new C2 IP is identified today, a scalable EDR can instantly scan the last 90 days of telemetry to see if that IP was ever contacted.
- GenAI Integration: As discussed in Best Cybersecurity Software For 2026 Top Tools For Network Security Endpoint Protection And Ai Power/, GenAI is becoming the primary interface for security analysts, turning complex SQL-like queries into simple English questions.
Frequently Asked Questions
How does endpoint volume impact EDR pricing?
EDR pricing is heavily tiered. Small deployments (1-99) pay the highest per-unit cost. At the enterprise level (5,000+), custom pricing typically applies. Organizations can expect 20-40% discounts at high volumes, but must account for "hidden" costs like data egress fees in multi-cloud environments and long-term storage for compliance.
What is the performance impact of EDR agents on legacy systems?
Modern, lightweight agents are designed to consume less than 7% of CPU and 120MB of RAM. However, legacy systems (Windows Server 2012 R2 or older) may experience higher overhead. In these cases, choosing a user-space agent over a kernel-mode driver can prevent system instability, though it may limit some deep-visibility features.
Can EDR scale to OT and industrial environments?
Yes, but it requires a specialized approach. In Operational Technology (OT) environments, traditional active scanning or aggressive agent behavior can crash sensitive PLC/SCADA systems. Scalable enterprise EDR solutions for OT focus on passive monitoring and have specific support for legacy protocols and air-gapped management consoles.
Conclusion
Achieving EDR scalability enterprise environments is a journey of operational maturity. It requires moving away from reactive, tool-based thinking toward a framework-driven approach that prioritizes automated telemetry correlation and lightweight agent performance. By focusing on architectural resilience and vendor-neutral evaluation, organizations can build a security posture that doesn't just grow with the business but actively protects its future.
For more technical deep dives into the 2026 security landscape, Sign up for the Unlocked Cybersecurity Portal.