Stop Playing Identity Crisis with Your Customer Data

Your Customer Data Is Fragmented — And Attackers Know It
Customer identity and access management (CIAM) is the technology framework that lets organizations securely register, authenticate, and manage external users — customers, citizens, or partners — across digital properties, while balancing security with a frictionless experience.
Quick answer for evaluators:
| What you need | What CIAM delivers |
|---|---|
| Secure customer login | MFA, passwordless, adaptive auth |
| Unified customer profile | Centralized identity directory |
| Regulatory compliance | GDPR/CCPA consent management |
| Scalability | Millions of users, thousands of auth events/min |
| Reduced friction | SSO, social login, progressive profiling |
| Fraud prevention | Risk scoring, behavioral biometrics, ATO detection |
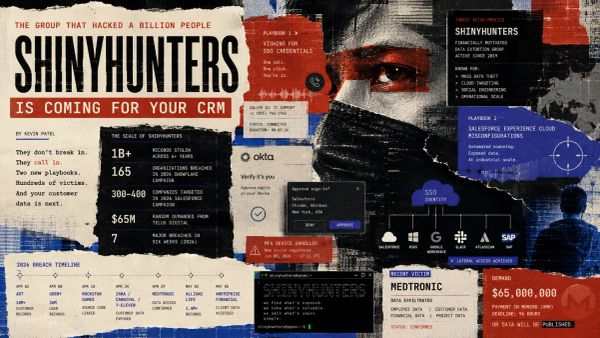
Here is the problem in plain terms: most organizations have customer data scattered across apps, portals, and databases with no single authoritative source. Marketing has one profile. The e-commerce platform has another. The mobile app has a third. None of them agree.
That fragmentation is not just an operational headache — it is a security liability.
Phishing and stolen credentials are behind the most damaging breaches in 2024 and 2025. The global average cost of a data breach hit $4.88 million in 2024. Meanwhile, 43% of consumers have already experienced fraud from stolen personal information online.
But here is what makes CIAM distinct from a pure security problem: it sits directly in the customer experience. A poorly designed login flow is not just annoying — it kills revenue. 54% of users have abandoned an account or service entirely because the login process frustrated them. Nearly half say they would switch to a competitor if that competitor offered a meaningfully better login experience.
That is not a UX problem. That is a churn problem.
CIAM is where security engineering, identity architecture, and customer experience intersect. Getting it right requires understanding all three dimensions — and choosing a platform that does not force you to sacrifice one for another.
This guide evaluates the core capabilities, architectural tradeoffs, and deployment considerations for modern CIAM platforms, so you can make an informed decision for your organization.
Defining Customer Identity and Access Management (CIAM) in 2026
In 2026, customer identity and access management is no longer just a "login box." It has evolved into a comprehensive digital identity layer that governs how external users interact with a brand across every touchpoint. Unlike internal systems designed for employees, CIAM is architected to prioritize the customer experience (CX) while maintaining enterprise-grade security.
At its core, CIAM governs the digital identities of users who sit outside the organization’s firewall. This includes not just traditional B2C customers, but also B2B partners, vendors, and even citizens accessing government services. By providing a unified identity layer, organizations can eliminate the "identity crisis" where a single customer appears as three different people across three different applications.
Business Value and ROI
Investing in a modern CIAM solution is a direct revenue driver. When the login process is seamless, conversion rates climb. Conversely, security friction leads to "cart abandonment"—a phenomenon where a user is ready to buy but leaves because they can’t remember their password or find the MFA process too cumbersome.
The benefits of modern identity management extend to customer loyalty and churn reduction. Statistics show that 87% of customers will walk away from a company with "sketchy" security policies. A robust CIAM platform signals to the user that their data is protected, building the trust necessary for long-term retention. Furthermore, by centralizing data, businesses reduce the operational costs associated with managing multiple disparate identity silos.
Core Capabilities of Modern Platforms
What should you look for in a 2026-era CIAM platform? The standard has shifted from simple authentication to a full-suite "identity fabric." Key features include:
- Self-Service Registration: Allowing users to create and manage their own accounts without IT intervention.
- Social Login: Enabling "Bring Your Own Identity" (BYOI) via Google, Apple, or Facebook to reduce sign-up friction.
- Unified Profile Management: A single source of truth for customer data that integrates with CRM and marketing tools.
- Scalability: The ability to scale to millions of users and handle unpredictable traffic spikes during major events.
Architectural Differences: Workforce IAM vs. CIAM
A common mistake among IT teams is assuming that the same platform used for employee logins can be used for customers. This often leads to architectural failure. The requirements for workforce IAM (managing employees) and CIAM (managing customers) are fundamentally different.
| Feature | Workforce IAM | CIAM (Customer Identity) |
|---|---|---|
| User Volume | Thousands (usually <150k) | Millions to Billions |
| Onboarding | HR-driven, mandated | Self-service, voluntary |
| UX Priority | Security first (employees must use it) | Experience first (users will leave) |
| Integrations | HRIS, Active Directory, SaaS apps | CRM, MarTech, E-commerce, Analytics |
| Traffic Pattern | Predictable (9-to-5) | Highly volatile (spikes during sales) |
For a deeper dive into these differences, see our complete guide to security access and credential management.
Scalability Requirements for Customer Identity and Access Management
Scale is perhaps the most significant differentiator. While a workforce IAM system might need to handle 50,000 employees logging in on Monday morning, a CIAM system for a major retailer must handle millions of concurrent users during Black Friday or a Super Bowl ad campaign.
Modern IAM platforms for 2026 utilize cloud-native, multi-tenant architectures to ensure that authentication latency remains in the milliseconds, even under extreme load. If your identity provider stutters during a peak traffic event, you aren't just losing access; you are losing revenue.
Friction vs. Security Balance
In the workforce, security is a mandate. If an employee finds MFA annoying, they still have to do it to get paid. In CIAM, friction is a "brand killer." With 54% of consumers reporting they've stopped using a service due to login frustration, the goal is to make security "invisible."
Leading CIAM solutions solve this by using adaptive policies. Instead of challenging every user with a complex MFA prompt, the system evaluates risk signals (device, location, behavior) and only adds friction when a login attempt looks suspicious.
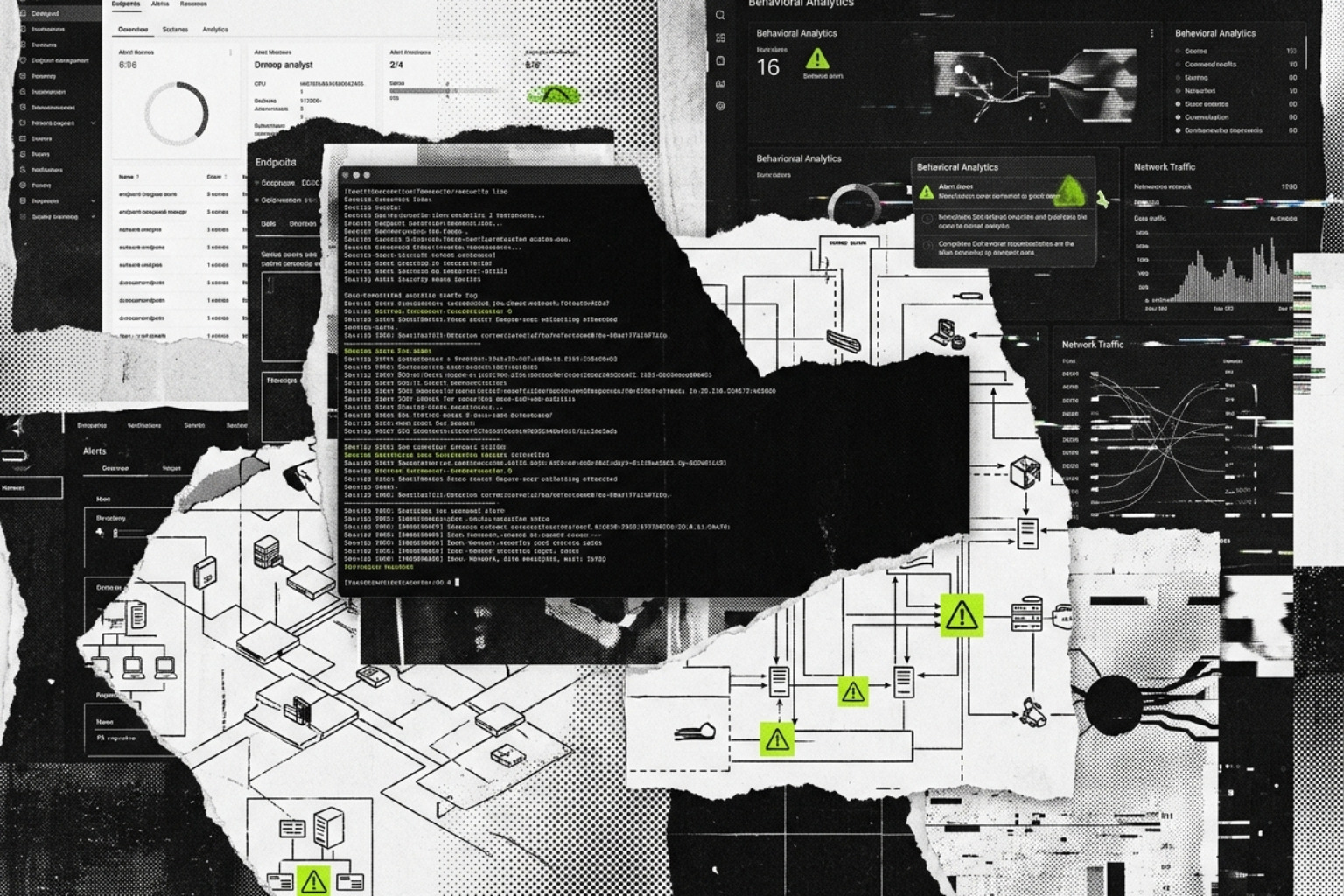
Security and Compliance: Mitigating the $4.88M Data Breach Risk
Security is the "back door" of the customer experience. While users want speed, they also demand protection. With the average cost of a data breach rising to $4.88 million, organizations cannot afford to treat CIAM as a secondary concern. Credential stuffing and account takeover (ATO) are the primary threats facing customer-facing portals today.
Effective strategies for managing IAM risks involve moving beyond static passwords to a multi-layered defense.
Privacy Regulations and Consent Management
Compliance is no longer optional. With GDPR in Europe, CCPA in California, and similar laws emerging globally, CIAM platforms must act as the "consent engine" for the enterprise. This includes:
- Version-Controlled Consent: Keeping a precise audit trail of which version of the Privacy Policy a user agreed to.
- Data Residency: Ensuring customer data is stored in specific geographic regions to comply with local laws.
- Self-Service Privacy: Giving users a dashboard to view, export, or delete their data (the "Right to be Forgotten").
Failure to manage these security threats defining 2026 can result in massive fines and permanent brand damage.
Adaptive Authentication and Fraud Prevention
The most effective way to secure a CIAM environment is through Zero Trust authentication. Modern platforms use AI and machine learning to calculate a "risk score" for every login.
If a user logs in from their usual iPhone in Chicago, they might go straight to their dashboard. If that same user suddenly appears to be logging in from an unrecognized Linux server in a different country, the CIAM system triggers Adaptive MFA. This might include behavioral biometrics—analyzing how a user types or moves their mouse—to distinguish a human from a bot without the user even knowing they are being screened.
Evaluating Modern CIAM Solutions: Core Capabilities and Orchestration
As the identity landscape becomes more complex, the "identity fabric" approach has gained traction. This involves using specialized IAM tools that can orchestrate workflows between different services.
Orchestrating Customer Identity and Access Management Workflows
Modern CIAM is moving toward "no-code" or "low-code" orchestration. This allows security teams to build complex logic—such as "If the user is from a high-risk IP, trigger identity verification via a third-party service"—using a drag-and-drop interface.
An effective IAM tool guide will emphasize the importance of APIs and SDKs. Developers shouldn't have to write custom code for every login screen; they should be able to "plug in" the identity layer so they can focus on building the actual product.
Advanced Authentication: Passwordless and Passkeys
The "death of the password" has been predicted for years, but in 2026, it is finally a reality. Technologies like FIDO2, WebAuthn, and Passkeys allow users to log in using their device's biometrics (FaceID or fingerprint). This provides a secure IAM experience that is both more secure than a password and significantly faster for the user.
Deployment Models and Integration Strategies
When choosing a customer identity and access management solution, the deployment model is a critical decision.
- SaaS (Software as a Service): The most common choice for CIAM, offering the highest agility and automatic updates.
- Hybrid Cloud: Useful for organizations that need to keep certain data on-premise for compliance while using the cloud for the authentication front-end.
- On-Premise: Rarely seen in modern CIAM due to scalability limitations, but sometimes required in highly regulated sectors like defense.
Choosing the best identity access management solution of 2026 requires a buyer’s guide approach that looks at your specific integration needs.
Standards-Based Interoperability
To avoid vendor lock-in, your CIAM platform must support open standards. This ensures that you can easily manage user permissions across different applications. Key protocols include:
- OpenID Connect (OIDC): The modern standard for authentication.
- SAML 2.0: Often used for B2B federation.
- OAuth 2.0: The gold standard for authorization.
Emerging Trends: Decentralized Identity and AI Agents
Looking toward the future of leading IAM solutions, two trends are dominating the conversation:
- Decentralized Identity: Using digital wallets and verifiable credentials so customers can own their data and only share what is necessary (e.g., proving they are over 21 without sharing their birth date).
- AI Agent Authorization: As AI agents begin to perform tasks on behalf of users (like booking a flight), CIAM systems must learn how to authorize these non-human entities securely.
Frequently Asked Questions about CIAM
How does CIAM differ from a CRM?
A CRM (Customer Relationship Management) system is designed for sales and marketing tracking—it records what a customer does. A CIAM system is a security tool designed for authentication and authorization—it proves who the customer is. While they often sync data, a CRM cannot securely handle passwords, MFA, or complex security protocols.
What is progressive profiling in CIAM?
Progressive profiling is a technique to reduce friction by only asking for data when it is needed. Instead of a 20-field registration form, you might only ask for an email and password at sign-up. Later, when the user goes to make a purchase, you ask for their shipping address. This "just-in-time" data collection improves conversion rates.
Can CIAM handle B2B and B2C users on one platform?
Yes, modern platforms use multi-tenancy and delegated administration. This allows a company to manage their direct consumers (B2C) while also giving a business partner (B2B) the ability to manage their own employees' access to a shared portal.
Conclusion
In 2026, your customer's identity is your most valuable asset and your greatest risk. By moving away from fragmented silos and adopting a unified customer identity and access management strategy, you protect your organization from multi-million dollar breaches while simultaneously driving growth through better user experiences.
Unlocked is here to help you navigate this landscape with technically precise, vendor-neutral insights. To take the next step in your journey, centralize your user access and governance with our comprehensive identity manager guide.