How to Use an Identity Management API
Core Functions of an Identity Management API
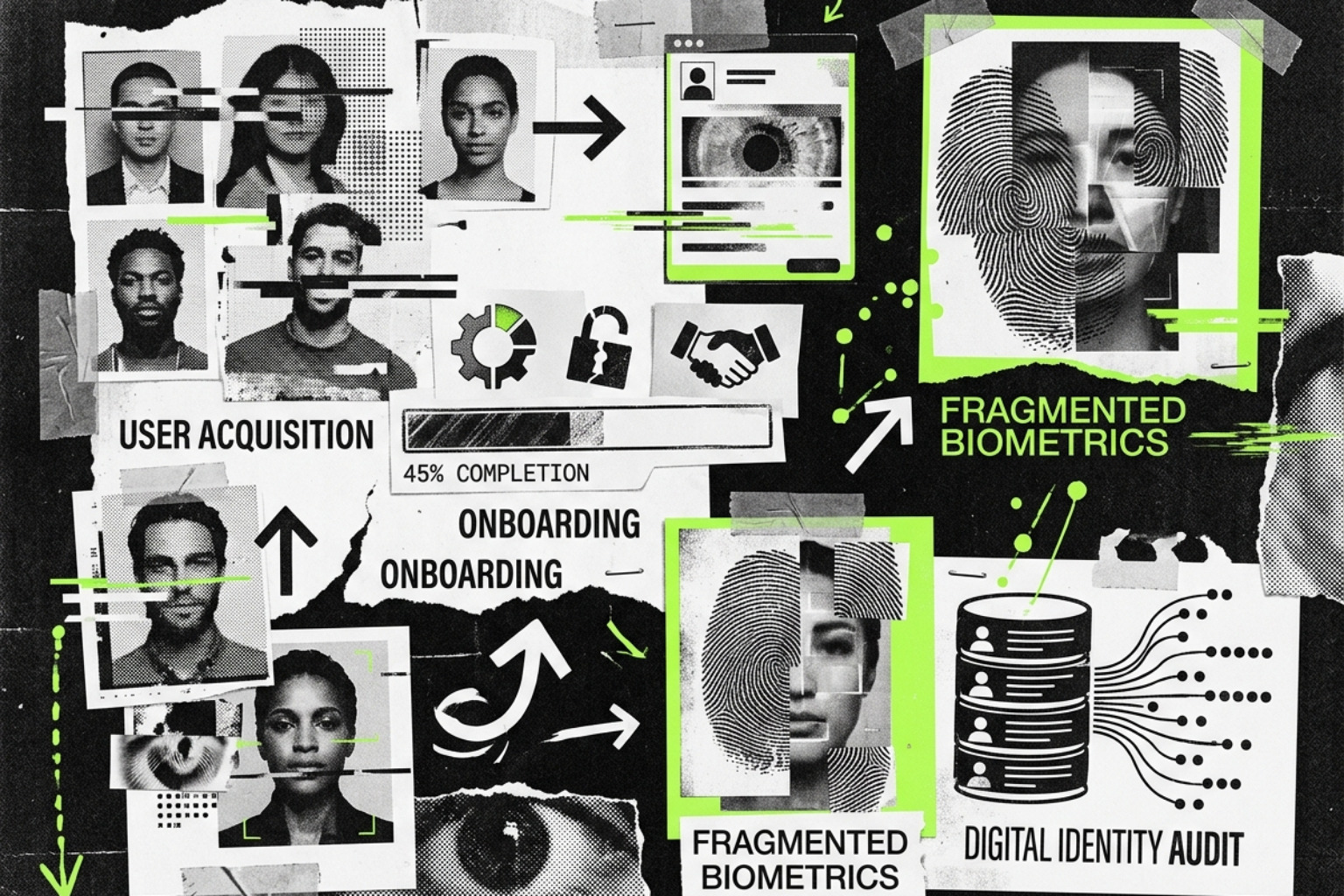
At its heart, an identity management API acts as the connective tissue between your core identity store and the applications that rely on it. Instead of an administrator clicking through a GUI to add a new hire, a script or an HR system integration sends a POST request to a /users endpoint. This automation is the foundation of modern Identity and Access Management (IAM).
The core functions provided by these APIs generally fall into four buckets:
- CRUD Operations: The basic Create, Read, Update, and Delete functions for user profiles.
- Group and Role Management: Programmatically creating groups and mapping users to them to enforce Role-Based Access Control (RBAC).
- Entitlement Mapping: Granularly defining what a user can do within a specific application, often handled via Identity Platform documentation.
- Credential Management: Handling password resets, MFA enrollment, and API key rotation.
By using these functions, enterprises can ensure that "one identity per individual" is maintained throughout the entire access lifecycle.
Authentication Methods for Identity Management API
Securing the API itself is just as important as the identities it manages. You can't exactly leave the "keys to the kingdom" behind a simple password. Modern identity management APIs use several sophisticated authentication schemes:
- OAuth 2.0 and OpenID Connect (OIDC): The industry standard for web-based APIs. These use scoped tokens (like
okta.users.manage) to ensure the calling application only has the permissions it absolutely needs. The critical nature of securing these tokens was highlighted by the 'Midnight Blizzard' (APT29) attack in early 2024, where attackers exploited a compromised OAuth application to pivot into corporate environments. - API Tokens and SSWS: Some platforms, like Okta, use a custom HTTP authentication scheme called
SSWSfor their Core Okta API. - GSSAPI and Kerberos: Common in Linux-native environments like Red Hat IdM. This allows for seamless, ticket-based authentication that integrates with existing Active Directory or LDAP environments.
- JSON-RPC and API Keys: Older or specialized systems might use JSON-RPC calls authenticated via static headers or specialized tokens.
Key Endpoints and Operations
While every vendor has their own flavor, most RESTful identity APIs follow a predictable pattern. Common endpoints include:
/users: The primary endpoint for managing individual identities./groups: Used for bulk authorization and organizational structure./sessions: Allows developers to view or revoke active user sessions, a critical tool during a suspected breach./roles: Defines the permissions associated with specific administrative levels.
Advanced APIs also support bulk-upsert and start-import operations, allowing you to synchronize thousands of users from an HR source (like Workday or SAP) in a single session. To navigate these large datasets, developers use cursor-based pagination rather than page numbers to ensure stability. Many modern APIs also implement HATEOAS (Hypermedia as the Engine of Application State), providing HAL links in the response so the developer knows exactly which endpoint to call next (e.g., a "self" link or a "change-password" link).
Comparing Leading Identity Management API Architectures
Choosing an identity management API often depends on your existing infrastructure. A company built entirely on AWS will have different needs than a hybrid-cloud enterprise running Red Hat Enterprise Linux.
| Feature | Microsoft Entra | Okta | AWS Identity Store | Red Hat IdM |
|---|---|---|---|---|
| Primary API | Microsoft Graph | Okta Core / IGA | Identity Store API | JSON-RPC / Python |
| Auth Method | OAuth 2.0 / OIDC | SSWS / OAuth 2.0 | IAM Policies / SDK | Kerberos / GSSAPI |
| Best For | M365 & Azure | SaaS & CIAM | AWS Infrastructure | On-prem Linux / AD |
| Governance | Entra Governance | Okta IGA | Limited | Manual/Scripted |
For more on choosing a platform, see our guide on Leading IAM Solutions 2025-2026.
Microsoft Entra and Google Identity Platform
Microsoft leverages the Microsoft Graph API, a massive, unified endpoint that covers everything from user profiles to network access. It excels at multi-tenancy and workload identities (identities for software, not humans).
Google Cloud’s Identity Platform, meanwhile, acts as an enterprise extension of Firebase. It provides a REST API that supports custom claims, allowing developers to bake specific authorization logic directly into the user's identity token. This is particularly useful for developers building global-scale applications who want to avoid the latency of checking a database for every permission.
Red Hat IdM and Siemens MindSphere
On the more technical end of the spectrum, Red Hat IdM uses a JSON-RPC v1.0 interface. While you can send raw JSON, Red Hat strongly recommends using their Python API, which automates the discovery of the server's schema (which can be as large as 2MiB and should be cached for performance).
In the Industrial IoT (IIoT) space, Siemens MindSphere provides region-specific OpenAPI specifications. This is vital for compliance in highly regulated sectors like manufacturing, where data residency and private cloud deployments are non-negotiable.
Implementation Best Practices for Developers
Integrating an identity management API is a high-stakes task. A single bug in your provisioning script could accidentally grant admin access to every new user or, conversely, lock your entire workforce out of their accounts.
- Enforce Least Privilege: Never use a "Super Admin" API key for a simple user-creation script. Use scoped tokens that only have the permissions required for the specific task.
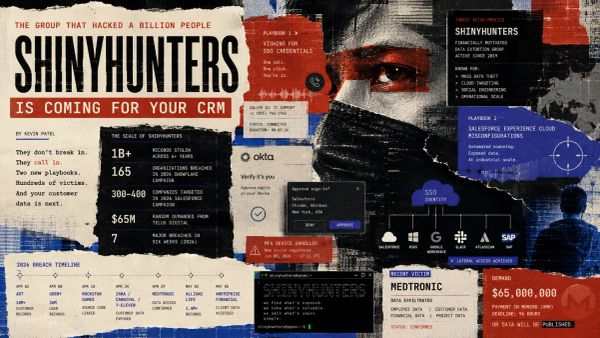
- Secret Management: Never hard-code API tokens in your source code. Use a vault (like HashiCorp Vault or AWS Secrets Manager). The 2024 Snowflake breach serves as a stark reminder of the risks associated with identity management; attackers targeted accounts lacking multi-factor authentication and robust credential rotation, leading to widespread data exfiltration.
- Implement Rate Limiting and Error Handling: Identity APIs are often heavily rate-limited to prevent DoS attacks. Your code must handle
429 Too Many Requestserrors gracefully with exponential backoff. - Use SCIM for Provisioning: Whenever possible, use the System for Cross-domain Identity Management (SCIM) standard. It provides a vendor-neutral way to automate user provisioning across different platforms.
Lifecycle Management via Identity Management API
Modern APIs go beyond simple CRUD. They manage the entire "Joiner, Mover, Leaver" (JML) process. For example, the Okta Identity Governance API allows you to automate access reviews and campaigns.
A key distinction here is between Request Status (is the manager okay with this?) and Grant Status (did the technical integration actually work?). If an API call to add a user to a downstream app group fails, the governance system can trigger an automated alert for manual intervention, preventing "silent failures" that leave users without access.
Schema Discovery and Performance Optimization
Because identity systems are complex, their APIs are often "self-documenting" through schema discovery. In Red Hat IdM, you can use the schema method to see every available command. However, because these schemas are large, caching is essential.
Other optimizations include:
- X-Okta-Request-Id: Always log the unique request ID returned in headers to correlate your API calls with the vendor's system logs during troubleshooting.
- CORS Registration: If you are calling an identity management API from a browser-based application, you must register your origin in the vendor's admin console to prevent Cross-Origin Resource Sharing (CORS) blocks.
- UTF-8 Limitations: Be aware that some APIs (like Okta’s) only support a subset of UTF-8, excluding four-byte characters. This can cause unexpected errors if your user data includes certain emojis or rare scripts.
Advanced Security and Compliance in API-Driven IAM
Using an identity management API is a prerequisite for achieving a Zero Trust Architecture. As CISA points out in their Continuous Diagnostics and Mitigation (CDM) guidance, you cannot "verify explicitly" if your identity data is out of sync or managed manually.
By automating IAM, organizations can meet strict regulatory requirements like GDPR (right to erasure), HIPAA (access controls for health data), and SOX (audit trails for financial systems). The benefits of modern IAM extend far beyond just security—they are the bedrock of digital compliance, aligning with frameworks like NIST SP 800-207.
Risk-Based Authentication and PAM
Advanced identity management APIs support risk-based authentication. This means the API can ingest signals—like an unusual IP address or a new device—and programmatically trigger adaptive MFA or step-up authentication.
Furthermore, Privileged Access Management (PAM) APIs enable "Just-in-Time" (JIT) access. Instead of a sysadmin having permanent root access, they use an IAM tool to request access via API. The system grants the permission for a limited window (e.g., 4 hours) and then automatically revokes it, significantly shrinking the attack surface.
Emerging Trends: AI and Agentic Security
Looking toward the future, we are seeing the rise of AI-driven governance. Imagine an AI agent that monitors API logs and notices that users in the "Marketing" group never actually use their "Financial Database" entitlement. The agent can then use the identity management API to suggest (or automatically execute) a revocation.
Other trends include:
- Agentic Security: Autonomous security "agents" that can provision and de-provision identities based on real-time threat intelligence.
- Universal Identity API: A push for a decoupled, "universal" API layer that sits above multiple IdPs, allowing developers to "mix and match" identity recipes like ingredients.
- Blockchain Consent: Using APIs to store user consent on a decentralized ledger, giving users more control over their personal data.
Frequently Asked Questions about Identity Management APIs
What is the difference between the Authentication API and the Management API?
The Authentication API is used at runtime when a user tries to log in (handling credentials and MFA). The Management API (or Identity Management API) is used by administrators or automated systems to configure the environment, create users, and manage permissions. You use the Management API to set up the user so they can later use the Authentication API.
How does SCIM simplify identity management API integrations?
SCIM (System for Cross-domain Identity Management) is a standardized API schema. If both your HR system and your Identity Provider (IdP) support SCIM, you can connect them with minimal custom coding. It "translates" user data into a common language that both systems understand.
Why is cursor-based pagination preferred over page-numbering in IdM APIs?
In a large, active identity store, users are constantly being added or deleted. If you use page numbers (e.g., "Give me page 5"), and a user is deleted on page 2 while you are reading, the results will "shift," and you might skip a user or see a duplicate. Cursor-based pagination uses a unique pointer to a specific record, ensuring you get a consistent, stable view of the data as you scroll through it.
Conclusion
The identity management API has evolved from a niche tool for sysadmins into the backbone of enterprise security. Whether you are automating employee onboarding with Microsoft Graph or securing industrial sensors with MindSphere, understanding the underlying API architecture is critical.
By moving away from manual processes and embracing an API-first approach, organizations can reduce help-desk costs, eliminate human error, and build a resilient Zero Trust environment. For more technical deep-dives into IAM, explore our guide on how to Centralize User Access and Governance with Identity Manager.