Continuous Authentication: Persistent Access Assurance for Modern IT Environments
Traditional authentication stops at the login screen — continuous authentication keeps verifying identity throughout a session using behavioral signals, device context, and risk scoring. Discover how this approach closes the gap that stolen credentials leave wide open.

Continuous authentication is a method of verification aimed at providing identity confirmation and cybersecurity protection on an ongoing basis.
This article is intended for IT professionals and security leaders seeking to understand how continuous authentication can enhance security and user experience in modern organizations. As cyber threats become more sophisticated and attack surfaces expand, traditional authentication methods are no longer sufficient to protect sensitive data and user accounts. Continuous authentication offers a persistent, adaptive approach to identity assurance, ensuring that only legitimate users maintain access throughout their sessions — without disrupting productivity.
Introduction to Modern Authentication
Modern authentication has rapidly evolved to address the growing complexity of cybersecurity threats. Unlike traditional methods that rely solely on passwords or basic two-factor authentication, today’s authentication methods are designed to provide secure identity verification across the entire session. Organizations now recognize that static credentials are no longer sufficient to protect sensitive data and user accounts from sophisticated attacks. As a result, advanced authentication methods — such as continuous authentication — are being adopted to ensure that user identity is verified not just at login, but throughout every interaction. This shift not only strengthens security but also streamlines the user experience by reducing the need for repeated logins and minimizing workflow interruptions. In an era where cyber threats are constantly evolving, embracing modern authentication methods is essential for maintaining robust security and user trust.
Transitioning from traditional to modern authentication methods is crucial for organizations aiming to stay ahead of emerging threats. The next section explores how authentication has evolved over time.
Evolution of Authentication
The journey of authentication methods has seen a transformation from simple passwords to more complex and secure solutions. Initially, traditional authentication methods relied on single-factor authentication, such as a password, which quickly became vulnerable to cyber attacks. To enhance security, organizations introduced two-factor authentication and multi-factor authentication, combining something the user knows, something they have, and something they are — like biometric data. While these approaches provided enhanced security compared to traditional authentication, they still only verified the user at the point of login. This static approach left gaps that could be exploited during the session. Continuous authentication addresses these shortcomings by leveraging user behavior and biometric data to provide ongoing verification. By monitoring how a user behaves throughout their session, continuous authentication methods ensure that only legitimate users maintain access, offering a dynamic and adaptive layer of protection that traditional authentication methods cannot match.
This evolution has paved the way for continuous authentication, which we will explore in detail next.
Continuous Authentication
Continuous authentication shifts identity assurance from a single checkpoint to an always-on process that protects sensitive data without disrupting access. Unlike traditional authentication methods that validate a user only at login, continuous authentication remains vigilant throughout a user session, offering dynamic protection against unauthorized access. Continuous authentication shifts from one-time logins to persistent, risk-based user monitoring.
Behavioral Monitoring
Continuous authentication works by assessing user behavior patterns on an ongoing basis. Behavioral biometrics refer to unique patterns in user actions, such as typing rhythm, mouse movements, or how a user interacts with their device. Continuous authentication continuously assesses these behavioral biometrics to confirm identity throughout an online session.
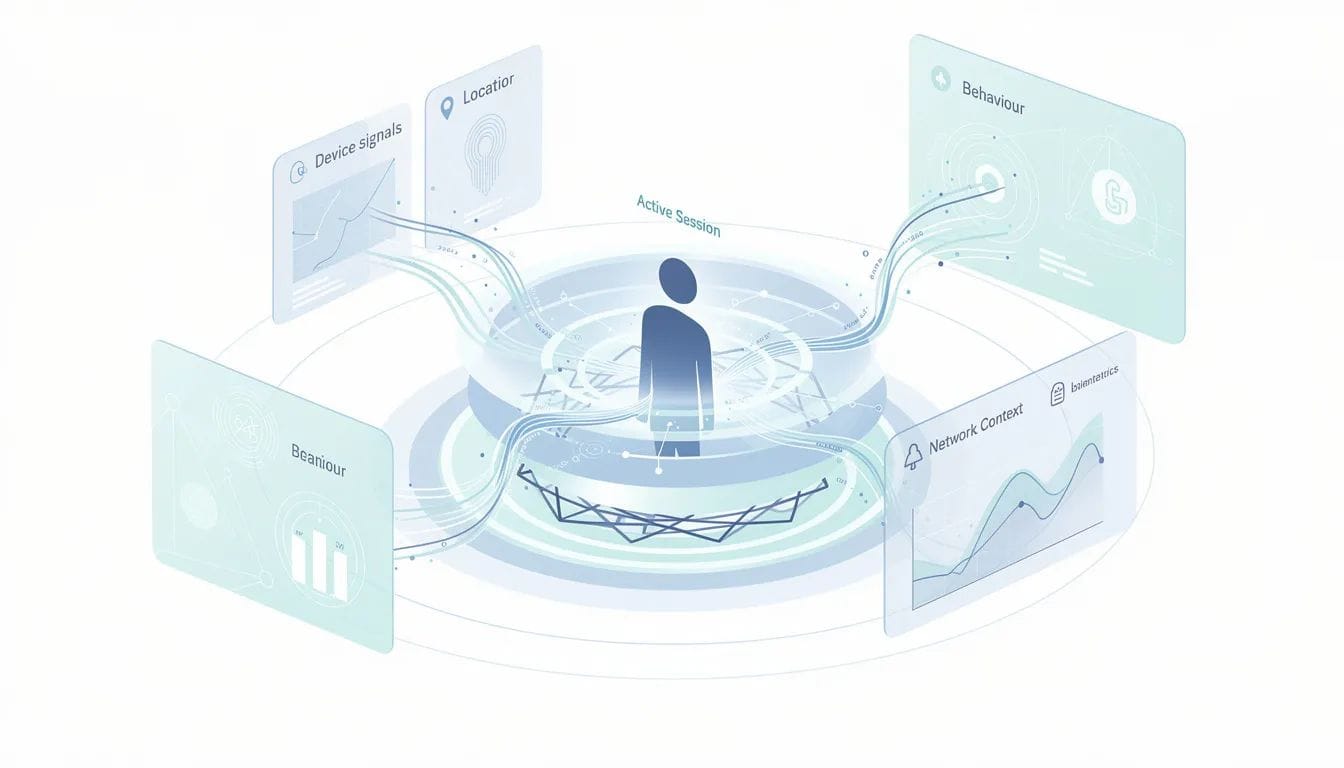
Real-Time Data Analysis
Continuous authentication monitors biometric, behavioral, and context-based data in real time to continually confirm the user’s identity. Context-based data includes information such as device location, network, and time of access. By analyzing these data streams, continuous authentication can detect potential threats or unauthorized access, such as insider threats or session hijacking.
User Experience
Continuous authentication allows organizations to monitor user activity from login to logout, delivering strong authentication without active participation from the user. It operates in the background, continuously assessing user behavior without direct user participation, which enhances usability. This approach provides a seamless user experience while maintaining security by monitoring user behavior and flagging anomalies without interrupting the workflow.
With a clear understanding of continuous authentication, it is important to compare it to traditional authentication methods to highlight its advantages.
Authentication Methods
Traditional authentication methods rely on static credentials such as a strong password, two-factor authentication, or biometric checkpoints like facial recognition or retina scans. These traditional methods successfully authenticate users at a single point in time, but they struggle to detect suspicious behavior once access is granted.

Continuous authentication represents an evolution in user authentication by providing ongoing verification and threat mitigation beyond the initial login. It addresses vulnerabilities of traditional methods like Multi-Factor Authentication (MFA) against session hijacking or credential theft by analyzing the entire context surrounding the user access request.
Now that we have compared traditional and continuous authentication, let’s examine how continuous authentication works in practice.
How Continuous Authentication Works
Continuous risk-based authentication is an advanced security approach that monitors user behavior throughout the session, rather than relying solely on one-time login verification. Its risk-based design leverages artificial intelligence and real-time data analysis to maintain security.
A risk engine is a system that analyzes these data streams — including behavioral biometrics and context-based data — to assess the likelihood of fraud or unauthorized access. Here’s how continuous authentication typically functions:
Step 1: Data Collection
- The system collects multiple streams of data throughout the user's session, including:
- Behavioral biometrics (e.g., typing rhythm, mouse movements)
- Context-based data (e.g., device location, network, time of access)
- Physiological biometrics (e.g., fingerprint, facial recognition)
Step 2: Profile Building
- Data from different parts of a user's session — such as device activity, movements, and interactions — are analyzed to build a behavioral profile unique to each user.
Step 3: Real-Time Analysis
- The risk engine continuously computes an authentication score to determine how certain it is that the account owner is the one using the device.
- It monitors for anomalies or deviations from the established behavioral profile.
Step 4: Risk Response
- If the risk engine detects suspicious activity or a significant deviation, it can:
- Trigger additional verification steps
- Revoke access
- Alert security teams
By analyzing deviations in user behavior profiles in real time, continuous authentication systems can detect fraud and trigger additional verification steps to prevent unauthorized transactions. This process helps reduce the window of opportunity for malicious actors by continuously verifying user identity throughout a session.
With an understanding of how continuous authentication works, let’s explore the different types of methods used to implement it.
Types of Continuous Authentication Methods
Continuous authentication methods rely on a combination of behavioral biometrics, contextual signals, and physiological biometrics to provide ongoing verification.
Behavioral Biometrics
Behavioral biometrics refer to unique patterns in user actions, such as:
- Typing rhythm (keystroke dynamics)
- Mouse movements
- Swipe patterns on mobile devices
- Finger pressure
- User activity cadence
- How the user behaves across devices
Contextual Signals
Context-based data includes information such as:
- Device location
- Network type and status
- Time of access
- IP addresses
- Geographic data
Physiological Biometrics
Physiological biometrics may include:
- Fingerprint recognition
- Facial recognition
- Retina scans
Risk Engine
A risk engine is a system that analyzes these data streams to assess the likelihood of fraud or unauthorized access. It applies the appropriate level of authentication during the entire session based on real-time risk assessment.
By leveraging these methods, continuous authentication provides a dynamic and adaptive layer of protection that traditional authentication methods cannot match.
Next, we’ll look at the solutions available for implementing continuous authentication in organizations.
Continuous Authentication Solutions
Continuous authentication solutions are designed to be among the most secure authentication methods available today. As companies seek new ways to prevent unauthorized access to critical business data, continuous authentication is gaining attention.
Security Benefits
Continuous authentication helps reduce the risk of threats like brute force attacks, social engineering, and phishing. It also helps organizations comply with data protection regulations such as GDPR and HIPAA.
Integration and Presence-Based Solutions
When integrated thoughtfully, solutions that emphasize presence and proximity can reinforce access confidence without adding friction. Platforms such as EveryKey align with this approach by continuously confirming identity based on presence, ensuring access remains seamless while trust is always given and continuously verified.
Real-Time Monitoring and Adaptive Access
Additionally, continuous authentication functionality enables real-time monitoring of user behavior and physiological traits to verify identity, and can automatically revoke access if suspicious activity is detected. This functionality is especially effective when integrated with systems like IDS, firewalls, and SIEM, further enhancing overall security with adaptive access control.
With a variety of solutions available, organizations can tailor continuous authentication to their specific needs. The next section explains how continuous authentication maintains security throughout a user session.
Continuous Authentication Throughout the Session
Continuous authentication works by maintaining awareness across the entire session. It remains vigilant throughout a user session, offering dynamic protection against unauthorized access. For example, financial institutions can determine and apply authentication requirements that match the relative risk of the transaction as it is taking place.
These systems perform ongoing user identity verification by monitoring behavioral and contextual data throughout the session, further enhancing fraud detection and security. Continuous authentication enhances user experience by allowing employees to log in once and gain access to all their normal applications and resources without repeated logins.
Understanding how continuous authentication operates throughout a session highlights its value in identity verification, which we will discuss next.
Identity Verification in Continuous Authentication
Identity verification under continuous authentication is contextual and adaptive. By leveraging behavioral biometrics and context-based data, organizations can reduce friction for legitimate sessions by decreasing the authentication required for genuine interactions. This approach provides a seamless user experience while maintaining security by monitoring user behavior and flagging anomalies without interrupting the workflow.
This method supports secure identity verification while minimizing disruption across corporate applications, mobile devices, and online sessions.
Next, we’ll explore how behavioral biometrics further strengthen identity verification.
Behavioral Biometrics and Continuous Authentication
Behavioral biometric signals strengthen identity verification without requiring explicit action from the user. These signals include:
- Swipe patterns
- Keystroke dynamics
- Finger pressure
- Other behavioral data derived from individual users
Continuous authentication monitors biometric, behavioral, and context-based data in real time to continually confirm the user's identity and flag anomalies. It continuously computes an authentication score to determine how certain it is that the account owner is the one using the device.
As organizations move toward more secure architectures, continuous authentication plays a key role in Zero Trust strategies.
Continuous Authentication and Zero Trust
By 2026, continuous authentication has become a foundational element of Zero Trust architecture. Within this framework, continuous authentication supports ongoing verification rather than implicit trust. It achieves its full potential when integrated with other security systems, forming a multi-layered defense strategy against cyber threats. When higher risks are detected during ongoing monitoring, continuous authentication can trigger additional security measures to further protect sensitive resources.
Having established its role in Zero Trust, let’s revisit the limitations of traditional methods and how continuous authentication addresses them.
Limitations of Traditional Methods
Traditional methods struggle to address modern cybersecurity risks because they validate identity only once. Continuous authentication addresses vulnerabilities of traditional authentication by detecting abnormal behavior after access is granted, helping to prevent unauthorized users from maintaining access to sensitive systems. It provides a more secure alternative by analyzing the entire context surrounding the user access request.
To further enhance its effectiveness, continuous authentication leverages machine learning and AI.
Machine Learning in Continuous Authentication
Machine learning enables continuous authentication to scale and adapt. Machine learning algorithms can analyze large amounts of transaction data to detect anomalies in real time based on risk scores. These algorithms evaluate data sources, user types, and risk factors to generate the most accurate risk score possible.
AI-powered systems can be integrated with firewalls, intrusion detection systems, and Security Information and Event Management (SIEM) platforms to:
- Enhance adaptability and response to potential threats
- Flag abnormal behavior in real time, even if the user is authenticated
- Create a unified dashboard for monitoring multiple security events
When combined with machine learning, continuous authentication helps mitigate many attack vectors such as credential stuffing, phishing, and session hijacking, reducing the risk of various cybersecurity threats.
With the technical foundation established, let’s discuss how organizations can implement continuous authentication.
Implementing Continuous Authentication
Successfully implementing continuous authentication solutions begins with a thorough assessment of an organization’s unique security requirements and risk landscape. Selecting the right technology partner and establishing the necessary infrastructure are foundational steps to ensure seamless integration. Equally important is training both stakeholders and end users to foster user acceptance and maximize the effectiveness of continuous authentication.
Ongoing continuous monitoring and regular risk assessments allow organizations to adapt to new threats and refine their authentication process over time. Integrating continuous authentication with existing security systems — such as event management platforms and security information and event management (SIEM) solutions — enables real-time detection and response to suspicious activity. This holistic approach ensures that continuous authentication not only strengthens security but also supports efficient event management and comprehensive oversight of user activity.
After implementation, organizations should consider the financial impact and return on investment.
Cost Implications and ROI
Implementing continuous authentication involves upfront investments in technology, infrastructure, and personnel. However, these direct costs are often outweighed by the substantial indirect savings realized through reduced data breaches, minimized operational downtime, and increased user trust. Data breaches can result in significant financial losses, legal liabilities, and reputational damage — costs that can far exceed the initial investment in robust authentication solutions. By proactively preventing unauthorized access and safeguarding sensitive data, continuous authentication delivers a strong return on investment. For organizations, the ability to prevent even a single major data breach can justify the cost of deploying continuous authentication, making it a strategic decision that protects both users and the business as a whole.
While the financial benefits are clear, organizations must also address privacy and adoption considerations.
Privacy and Adoption Considerations
Continuous authentication raises data privacy concerns due to passive and constant monitoring of user behavior and biometrics. Privacy concerns can arise from continuous monitoring, leading to user resistance against its implementation. User acceptance is a significant challenge for continuous authentication, as some users may feel uncomfortable with being passively monitored.
False positives can occur in continuous authentication systems, where genuine user actions are misidentified as anomalies, leading to unnecessary security measures. Technical hurdles exist in implementing continuous authentication, requiring advanced tech infrastructure and skilled personnel for seamless integration. Balancing privacy concerns and security benefits is key to the acceptance of continuous authentication.
To address common questions, the following section provides concise answers for IT professionals and security leaders.
Frequently Asked Questions
What is continuous authentication?
Continuous authentication is a method of verification aimed at providing identity confirmation and cybersecurity protection on an ongoing basis throughout an entire session.
How does continuous authentication improve security?
Continuous authentication enhances security by continuously validating users' identities throughout their session and detecting suspicious behavior in real time.
How does continuous authentication differ from traditional authentication?
Unlike traditional authentication methods that verify identity once, continuous authentication continuously monitors user behavior and context during the entire session.
Does continuous authentication impact user experience?
Continuous authentication operates in the background and enhances user experience by reducing repeated logins and minimizing friction for legitimate users.
Is continuous authentication part of Zero Trust?
Yes. By 2026, continuous authentication has become a foundational element of Zero Trust architecture, supporting persistent verification and adaptive access.