Understanding Certificate Based Authentication: A Comprehensive Guide
A complete guide to certificate-based authentication, PKI infrastructure, user certificates, mutual authentication, and eliminating passwords in enterprise environments.

Certificate-based authentication (CBA) is a critical security technology for modern organizations seeking to protect sensitive data and systems. This guide explains how CBA works, its benefits, and how it is implemented in environments like Microsoft Entra. It is intended for IT professionals, security administrators, and anyone interested in secure authentication methods.
Certificate-Based Authentication
Certificate-based authentication (CBA) is a widely-used security measure that provides a reliable and secure way to authenticate users, devices, or servers before granting access to a network or application. CBA is one of several authentication methods that rely on digital certificates to verify identity and enhance security.
Certificate-based authentication uses digital certificates to verify the identities of users, devices, or servers before granting access to a network or application. Digital certificates are used in certificate-based authentication to verify the identities of users, devices, or servers.
How Certificates Work
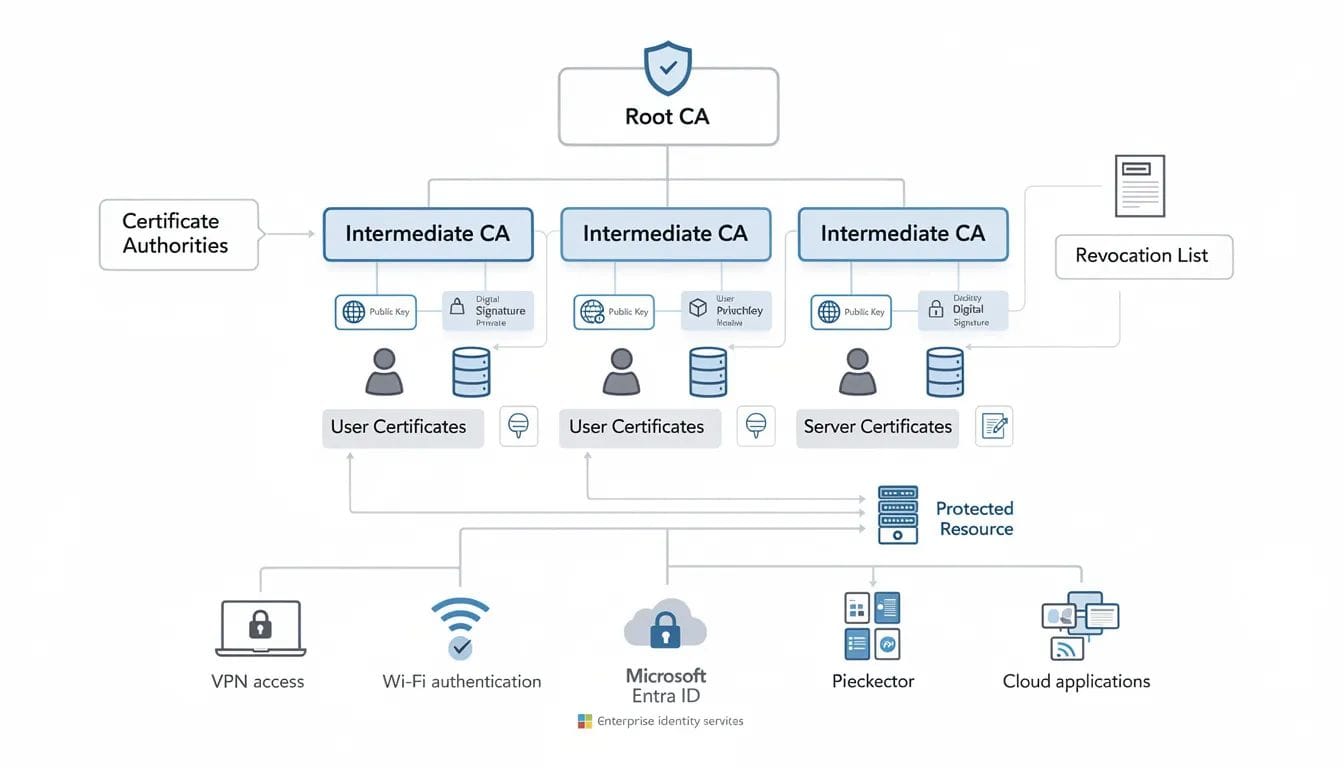
A digital certificate is like an electronic passport used to prove your identity by confirming your ownership of a private key. Digital certificates contain a public key, identification data used to verify the user's identity, and a digital signature. These certificates must be digitally signed by a trusted certificate authority (CA) to ensure their validity and authenticity.
Certificate-based authentication provides a much higher level of security than password-based credentials. By eliminating passwords, CBA streamlines authentication, increases security, and reduces vulnerabilities such as phishing or brute force attacks. Unlike password-based authentication and traditional username and password methods, which rely solely on what the user knows and are susceptible to guessing, phishing, and social engineering, certificate-based authentication uses cryptographic certificates that are difficult to forge or alter without detection, making CBA a tamper-proof authentication method.
Common use cases for CBA include:
- Securing VPN connections
- Wi-Fi network access
- Protecting high-value corporate resources
Compared to other authentication methods, certificate-based authentication offers superior security and ease of use without the need for additional hardware or complex deployment, especially when combined with next-generation passwordless authentication methods that further reduce phishing-related risks tied to passwords.
User Certificates
User certificates bind identity information to a cryptographic key pair. Each user has a unique private key that is paired with a public key, and this unique private key is essential for establishing and verifying the user's identity during certificate-based authentication.
For certificate-based authentication to work properly, the user must have a unique private key that corresponds to the public key in a certificate. The unique private key used in certificate-based authentication should never leave the user’s possession to maintain security. The private key of the user should never leave the user’s possession to maintain security in certificate-based authentication.
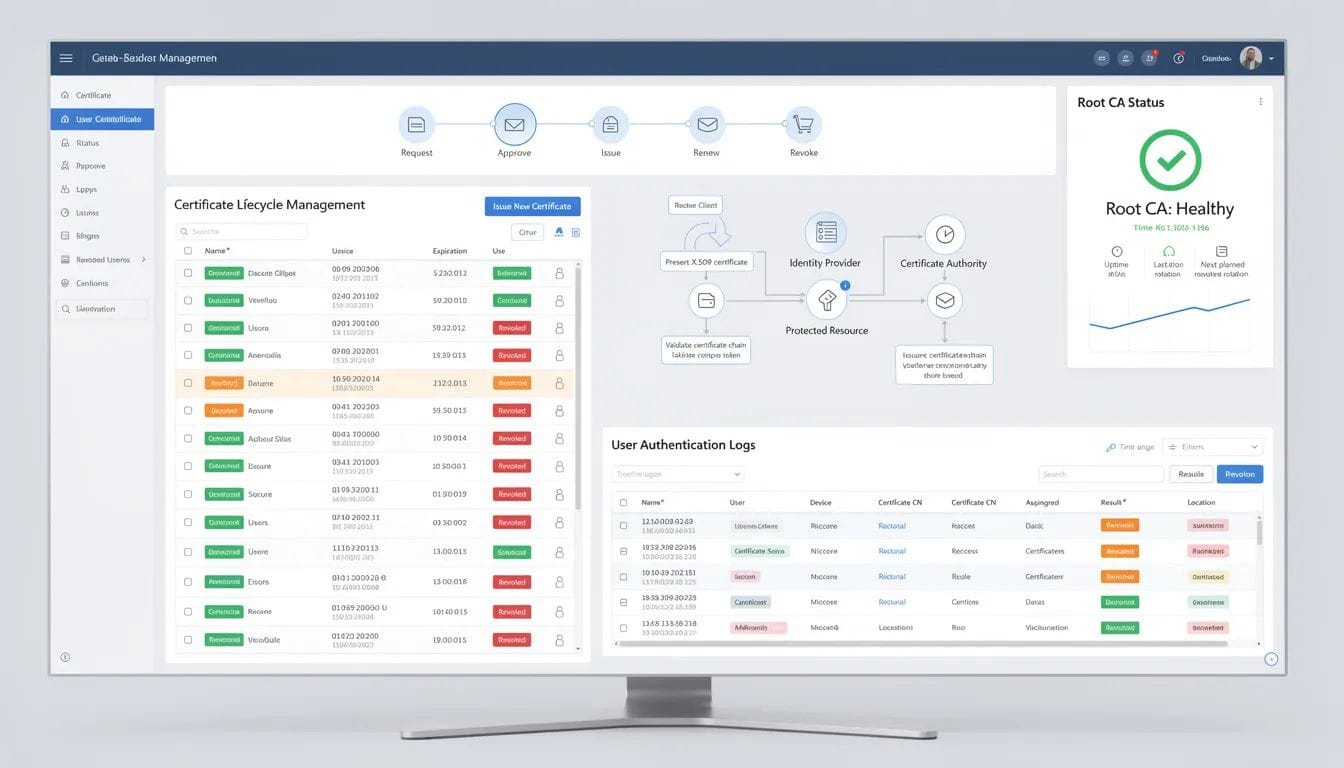
Certificate Revocation and Management
Certificates include expiration dates and can be revoked through certificate authorities or internal CAs. Organizations can revoke certificates instantly if compromise is suspected, strengthening access control and access management across user accounts, independent contractors, and external users as part of broader credential management best practices and user access management strategies.
Certificates allow users to be authenticated without having to remember several username and password combinations, increasing productivity. Certificate-based authentication can streamline the authentication process by allowing users to be authenticated without remembering multiple username and password combinations.
Certificate-Based
Certificate-based authentication utilizes a Public Key Infrastructure (PKI) to ensure that any attempt to modify the certificate will invalidate it. Public Key Infrastructure (PKI) is the framework that supports certificate-based authentication by managing digital certificates and public-private key pairs.
PKI Challenges and Considerations
Implementing a Public Key Infrastructure (PKI) for CBA can be complex and time-consuming. Operational costs associated with PKI management can be high, especially for smaller organizations.
CBA introduces new management demands despite offering enhanced security compared to traditional passwords. To implement certificate-based authentication, organizations should manage the technologies and processes that enable it effectively within a secure identity and access management framework.
Based Authentication
Authentication Process Details
Certificate-based authentication involves both the client and the server in a cryptographic exchange.
The authentication process typically involves these steps:
- The server sends a challenge encrypted with the public key.
- The client must decrypt the challenge with its private key to prove ownership.
- The server verifies the response to authenticate the client.
The entire authentication process in certificate-based authentication is performed in the user's browser and the server they are interacting with, making it one of several techniques discussed in multi-factor authentication vulnerabilities and strengths.
Web browsing over HTTPS relies on server certificates to ensure legitimacy. The same digital signature validation process applies to user authentication and secure access to protected resources.
How Certificate-Based Authentication Works
Certificate-based authentication works by validating cryptographic proof instead of shared secrets. The private key used in certificate-based authentication should never leave the user’s possession, ensuring greater security.
Endpoints and Use Cases
Certificate-based authentication can be used for any endpoint, including:
- Servers
- Personal computers
- E-passports
- Devices classified under the Internet of Things (IoT)
It enables computers to securely identify each other across a digital network infrastructure. Additionally, certificate-based authentication can be used to grant access to networks, applications, devices, and other resources within an organization's IT infrastructure as part of a broader access security control strategy.
Certificate-based authentication is a phishing-resistant cryptographic technique that enables computers to use digital certificates to securely identify each other across a network.
To enable the certificate-based authentication method in Microsoft Entra, administrators must configure CBA in the admin center; only users set up for CBA can authenticate using an X.509 certificate.
Secure Access
Secure authentication requires strong identity verification and trusted devices.
CBA can enhance security under the Zero Trust model by requiring a device-level signal alongside identity information about the authenticated user. This improves security posture and strengthens access privileges before granting access to a protected resource, aligning with modern Zero Trust security architecture and the broader Zero Trust approach to continuous verification.
Certificate-based authentication reduces insecure password practices and eliminates vulnerable passwords across enterprise environments.
Mutual Authentication
Mutual authentication ensures that both the client and the server validate each other’s certificates, functioning effectively as a certificate-based form of multi-factor authentication in modern identity security.
Digital certificates are difficult to forge or alter without detection, making certificate-based authentication tamper-proof. Mutual authentication protects against impersonation and fake website attacks while safeguarding sensitive information, which is especially valuable for remote workers who depend on strong MFA solutions for secure access from anywhere.
Microsoft Entra CBA
Microsoft Entra ID allows for certificate-based authentication using X.509 certificates issued from a trusted Public Key Infrastructure (PKI). Government agencies have long relied on certificate-based authentication to protect sensitive information in high-security environments.
Agencies can achieve certificate-based authentication functionality with Microsoft Entra joined devices or other vendor’s Mobile Device Management products. Microsoft Entra CBA integrates with Active Directory Federation Services and hybrid identity environments.
Microsoft Entra ID
Microsoft Entra ID strengthens multi-factor authentication strategies by introducing phishing-resistant authentication through certificate validation, contributing to a broader identity security strategy focused on Zero Trust and passwordless access.
Certificates are issued through trusted certificate authorities and validated against root CA hierarchies. Administrators can manage certificates centrally and revoke certificates when necessary to protect corporate data and identity information.
Microsoft Entra
Microsoft Entra extends certificate-based authentication across cloud applications, VPN gateways, and enterprise systems.
Because certificates are managed centrally, organizations gain greater security and eliminate vulnerable passwords while enhancing access management.
Conclusion
For the end user, certificate-based authentication simplifies access. There is no need to remember complex passwords or manage password combinations across systems.
Forward-thinking organizations may also layer certificate-based authentication with presence-driven identity validation platforms like EveryKey, which continuously confirms user proximity across devices and applications. This kind of Bluetooth-based multi-factor authentication aligns well with MSPs offering frictionless access and security and supports the broader move toward passkey-style passwordless authentication. Access follows the user, supporting Zero Trust principles while maintaining a seamless experience.
FAQ
What is certificate-based authentication?
Certificate-based authentication (CBA) uses digital certificates to verify the identities of users, devices, or servers before granting access to a network or application.
Is certificate-based authentication phishing-resistant?
Yes. Digital certificates are difficult to forge or alter without detection, making certificate-based authentication a phishing-resistant authentication method.
Does certificate-based authentication require PKI?
Yes. Public Key Infrastructure manages digital certificates and key pairs required for CBA.
Can Microsoft Entra ID support certificate-based authentication?
Yes. Microsoft Entra ID allows certificate-based authentication using X.509 certificates issued from a trusted PKI.
What are common use cases for CBA?
Common use cases for CBA include:
- Securing VPN connections
- Wi-Fi network access
- Protecting high-value corporate resources




