
iam
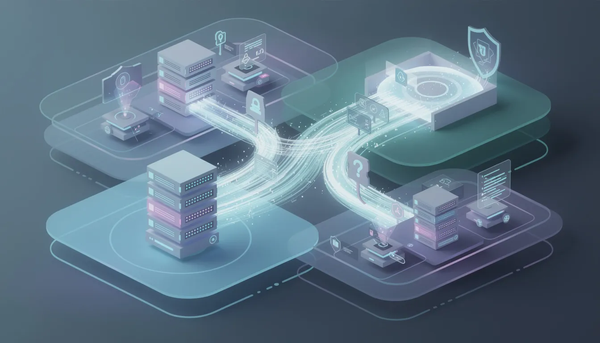
Best IAM Solutions of 2026: Top 10 Identity & Access Management Platforms Compared
Explore our comprehensive comparison of the top 10 IAM solutions of 2026 to find the best identity access management platform for your needs. Read more!
Coverage and comparisons of cybersecurity tools across identity, endpoint, network, cloud, and SOC categories. Analysis of vendor selection, integration architecture, deployment realities, and the buying decisions IT and security leaders face when assembling a defensive stack that holds up in production.

iam
Explore our comprehensive comparison of the top 10 IAM solutions of 2026 to find the best identity access management platform for your needs. Read more!

credential management
Discover top alternatives to Keeper for effective password management. Explore features, pros, and cons to find the best fit for your needs. Read more!

credential management
Explore top alternatives to Bitwarden for better password security in 2026. Find the right solution for your needs and enhance your online safety today!

credential management
Dashlane has raised its prices, and its free tier no longer offers much room to work with — so IT teams are actively looking for better options.

credential management
Discover the best alternatives to RoboForm for effective password management. Find the right solution for your security needs — read the article now!

credential management
Discover reliable alternatives to NordPass for effortless and secure password management. Explore your options and choose the best fit for your needs.

privileged access management
Enterprise password storage solutions for IT leaders: best practices, vault software, compliance strategies, and security essentials for 2026.

cybersecurity tools
A practical guide to the best enterprise security solutions for 2026, covering data security, cloud security, network protection, endpoint defense, and AI-powered detection and response.

cybersecurity tools
A practical guide to the best cybersecurity software in 2026, including AI-powered cybersecurity platforms, endpoint protection tools, network security systems, and identity protection solutions for modern organizations.

privileged access management
Learn how Azure Privileged Identity Management enhances security by managing access and roles effectively.
cybersecurity tools
An objective overview of technologies shaping modern cyber defense.

cybersecurity tools
Better ways to test password strength, reduce risk, and protect access.