
cyberattack
Understanding Cryptojacking: Dangers, Prevention, and Real-World Cases
Discover the risks of cryptojacking, how to prevent it, and explore real-world cases in order to stay informed and protect your devices.
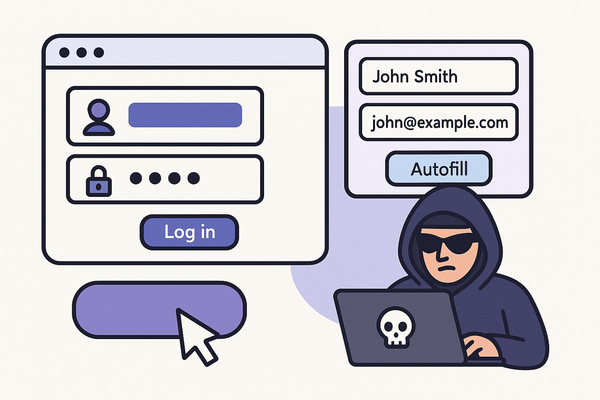
Phishing remains the most common entry point for cyberattacks. Coverage of email-based phishing, smishing, vishing, AI-generated lures, and the email security, awareness training, and authentication controls that meaningfully reduce the success rate of these attacks against organizations.

cyberattack
Discover the risks of cryptojacking, how to prevent it, and explore real-world cases in order to stay informed and protect your devices.

newsletter
🔓 Unlocked - Edition #15 - Tuesday, December 9th, 2025

newsletter
🔓 Unlocked - Edition #2 - Tuesday, September 9nd, 2025
newsletter
🔓 Unlocked - Edition #1 - Tuesday, September 2nd, 2025

phishing
Key Takeaways * Cybersecurity is a multi-layered defense strategy protecting systems, networks, and data from digital threats that could cost the global economy $10.5 trillion annually by 2026 * Modern cyber threats include ransomware, phishing, AI-powered attacks, and social engineering, requiring comprehensive protection across people, processes, and technology * Essential cybersecurity components

multi-factor authentication (mfa)
Why Phishing Is Still The #1 Threat – And Why Passwords Make It Worse Despite advances in cybersecurity, phishing attacks continue to dominate the threat landscape – and passwords remain the weak link that makes these attacks so effective. Even with security awareness training and multi-factor authentication (MFA), many organizations still fall