identity and access management
The Full Guide to Federated Identity Manager and Federated Identity Management
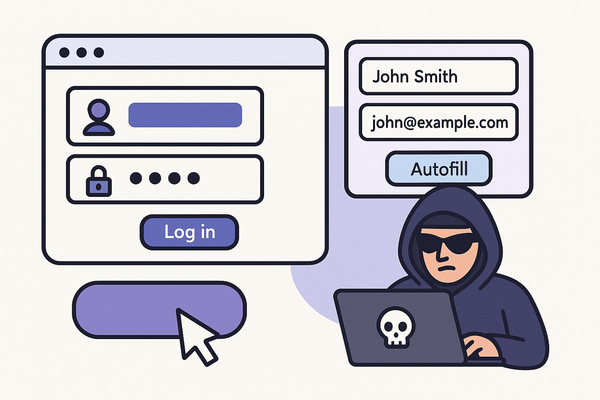
In an era where enterprises rely on multiple applications, third-party services, and multiple domains, managing user authentication and user access across platforms can be challenging. This is where a federated identity manager comes into play. By centralizing authentication and authorization across organizations and applications, federated identity solutions provide secure authentication,