
cybersecurity tools
Computer Software Security in 2026: A Practical Guide to Protecting Software Systems
A best-of-2026 guide to computer software security, secure access, and protecting software systems throughout the development lifecycle.
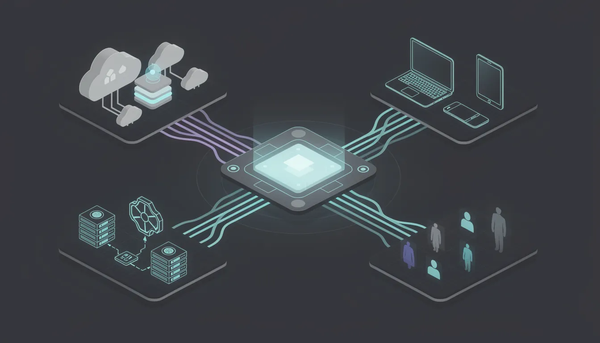
Coverage and comparisons of cybersecurity tools across identity, endpoint, network, cloud, and SOC categories. Analysis of vendor selection, integration architecture, deployment realities, and the buying decisions IT and security leaders face when assembling a defensive stack that holds up in production.

cybersecurity tools
A best-of-2026 guide to computer software security, secure access, and protecting software systems throughout the development lifecycle.

cybersecurity tools
A practical guide to the cybersecurity services, platforms, and capabilities enterprises rely on to stay resilient in 2026.
cybersecurity tools
How modern security platforms unify cloud security, threat detection, automation, and access control to reduce risk and scale protection across the entire environment.

cybersecurity tools
A 2026 Buyer’s Guide to Antivirus, Identity Protection, and Modern Threat Defense Across Every Device.

iam
How modern IAM tools protect identities, control access, and help organizations meet security and compliance requirements.

cybersecurity tools
Discover why users are moving beyond traditional password vaults like Norton — and how passwordless, proximity-based authentication is redefining digital security.

cybersecurity tools
Explore the best alternatives to the Authy app — from traditional two factor authentication tools to next-generation passwordless solutions that keep your accounts secure across every device.

cybersecurity tools
Cybersecurity is no longer a luxury for modern businesses — it’s a necessity. With sensitive data spread across endpoints, networks, mobile devices, and cloud resources, the challenge of protecting digital assets has grown more complex. Cybersecurity tools give organizations the ability to detect, respond to, and prevent cyber threats, while

security keys
Introduction to Authentication Authentication is the essential process that helps users, devices, or systems prove who they are before accessing online accounts, sensitive information, or secure systems. In today’s digital world, authentication is the backbone of security, protecting us from unauthorized access, data breaches, and a host of cyber