
best practices
Password Strength Test: How to Check If Your Passwords Are Truly Secure
A practical guide to password strength tests, password security, and best practices for protecting online accounts from modern attacks.
Cybersecurity best practices distilled from incident response, vendor research, and frameworks like NIST and CIS. Coverage spans identity, endpoints, cloud, email, and the operational habits that consistently differentiate organizations that hold up under attack from those that don't.

best practices
A practical guide to password strength tests, password security, and best practices for protecting online accounts from modern attacks.

best practices
How identity providers, MFA, and centralized identity management strengthen security while delivering seamless access across modern enterprises.

best practices
Best practices for creating strong passwords, using password managers, and protecting online accounts from modern cyber threats.
best practices
A modern breakdown of the CIS password policy, failed login controls, MFA adoption, and best practices for securing user accounts against evolving cyber threats.
best practices
How modern technical cyber security protects cloud environments, networks, endpoints, and identities against evolving cyber threats in an increasingly complex digital world.
best practices
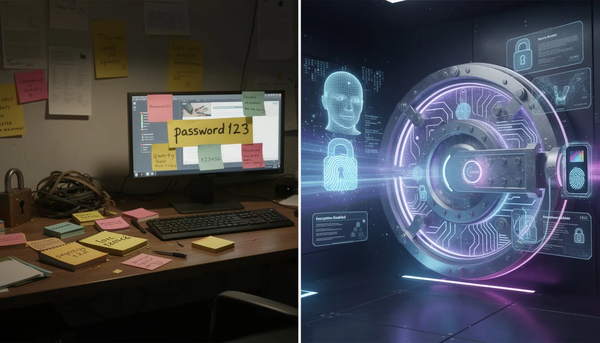
When pen-and-paper password habits collide with modern password managers and MFA.

best practices
Why password length, randomness, and modern security practices matter more than ever.

best practices
How to strengthen authentication, improve usability, and safeguard sensitive data with smarter SSO implementation.

best practices
How the National Institute of Standards and Technology (NIST) reshaped password security to reduce friction and strengthen digital trust.

best practices
How mobile identity solutions use device intelligence, biometrics, and AI to protect users, prevent fraud, and deliver secure digital experiences.

best practices
Explore how InfoSecurity integrates technology, governance, and training to protect digital assets, align with business objectives, and manage risk in a rapidly evolving cybersecurity landscape.

best practices
Passwords are still the first line of defense for many online accounts, from social media accounts to online banking. Yet, weak passwords remain one of the most commonly used entry points for hackers in a data breach. Understanding how to create strong passwords — and how to maintain them across multiple