SIM Swapping: How Hackers Steal Your Phone Number — and Your Life
🔓 Unlocked - Edition #12 - Tuesday, November 18th, 2025

In partnership with

👋 Welcome to Unlocked
This week, we’re breaking down one of the fastest-growing cybercrimes affecting everyday people — and one of the least understood.
You lock your doors. You protect your passwords.
But what if a criminal could steal your identity with nothing more than a phone call?
That’s the reality of SIM swapping, a technique that lets attackers take control of your phone number, intercept your text messages, bypass your multi-factor authentication, and reset your most sensitive accounts — all without touching your device.
It’s fast. It’s silent. And you often don’t know it’s happened until the damage is done.
Let’s unpack how SIM swapping works, why it’s exploding right now, and what security leaders — and everyday users — must do to stay protected.
✉️ Our Sponsor
Free email without sacrificing your privacy
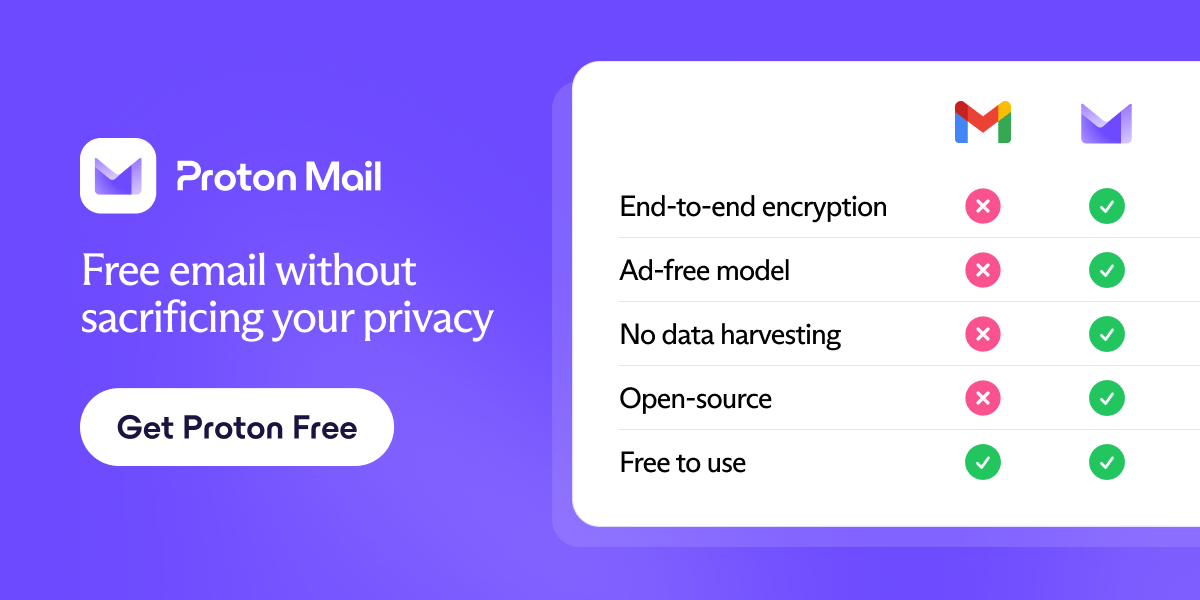
Gmail is free, but you pay with your data. Proton Mail is different.
We don’t scan your messages. We don’t sell your behavior. We don’t follow you across the internet.
Proton Mail gives you full-featured, private email without surveillance or creepy profiling. It’s email that respects your time, your attention, and your boundaries.
Email doesn’t have to cost your privacy.
📲 SIM Swapping 101: When Your Phone Number Is the Weakest Link
SIM swapping (also called SIM hijacking) happens when a criminal convinces your mobile carrier to transfer your phone number to their SIM card.

Once they do, they instantly gain access to:
- Your text message–based MFA codes
- Password reset links
- Banking and crypto logins
- Email and social accounts tied to your number
Most victims first realize something is wrong when their phone suddenly loses service, showing “SOS,” “No Network,” or “Emergency Calls Only.”
By then?
The attacker already owns your identity.
(See: FBI PSA – SIM Swapping Threat Alert)
⚠️ The Real-World Impact: Millions Lost, Identities Taken
SIM swapping isn’t theoretical — it has already cost victims hundreds of millions of dollars across banking, crypto, and fintech platforms.
One Ohio investor lost $24 million in cryptocurrency in under 30 minutes after a successful SIM hijack.
And according to the FBI, SIM swap complaints jumped 400% in a single year — with losses now exceeding ransomware in some categories.
Why so effective?
Because your phone number is still treated as proof of identity — even though attackers can socially engineer it away in minutes.
(See: Thomson Reuters - A deep dive into the growing threat of SIM swap fraud)
🧠 Why SIM Swapping Works So Well
Attackers don’t break in — they call in.
They exploit:
- Overworked carrier support reps
- Publicly leaked personal data
- Systems that still rely on SMS MFA
- The myth that “my phone = my identity”
With nothing more than a spoofed caller ID and your name, an attacker can claim:
“Hi, I lost my phone. Can you activate my new SIM?”
…and walk right into your bank accounts.
(See also: Our Blog – The Benefits of Multifactor Authentication in a Modern Security Landscape)
🧩 The Cybersecurity Angle: SMS MFA Is Now an Attack Surface
From a security perspective, SIM swapping exposes a deeper truth:
SMS is no longer a secure-multi factor option.

If your identity stack relies on:
- 2FA text message codes
- Password reset SMS links
- Phone-number-based identity verification
…you’ve already ceded control to telecom support desks.
Even major platforms like Coinbase, Microsoft, and PayPal now warn customers not to rely solely on SMS authentication.
Organizations must start treating phone numbers like volatile, high-risk credentials, not trusted identity anchors.
🔐 How to Protect Yourself from SIM Hijacking
Security teams and individuals should take these steps today:
1️⃣ Add a Carrier Port-Out PIN
Call your mobile provider and set a manual authorization PIN required before transferring your number.
Most users never do — attackers count on that.
2️⃣ Replace SMS MFA With App-Based or Proximity MFA
Use app-based authentication such as Authy or Microsoft Authenticator — or proximity-based MFA like Everykey Echo.
If a hacker steals your number, app-based codes still won’t work.
➡️ Read more:
Credential Management: Protecting Digital Access in a Zero Trust Era
3️⃣ Lock Down Financial & Crypto Platforms
Ensure your bank, brokerage, and crypto exchange accounts do not rely on SMS for recovery.
4️⃣ Turn on Account Alerts
If someone logs in, resets a password, or changes a setting — you’ll know instantly.
🏢 What It Means for Security Leaders
Security teams should ask:
- How many internal systems still rely on SMS MFA?
- Do we store employee phone numbers as primary identity factors?
- If an engineer’s SIM is hijacked at 2 AM, can our admin panel be taken over?
SIM swapping is not a consumer scam — it is a supply-chain access threat.
Attackers don’t just steal crypto — they steal infrastructure.
(See: Microsoft – Defending against evolving identity attack techniques)
🧠 The Bigger Trend: Identity Theft Without Malware
SIM swapping proves a shift already underway:
Hackers no longer need code.
They just need customer service.
Modern identity crime increasingly uses social engineering, support desk exploitation, and authentication gaps instead of malware.
The future of cybersecurity won’t just be about patching vulnerabilities — it will be about eliminating the weak points in human-centered systems.
💡 Unlocked Tip of the Week
Take 3 minutes today and call your mobile carrier.
Ask to add a "SIM port protection PIN" or "Number transfer lock."
It is the single best defense against SIM swapping — and most people still don’t know it exists.
📊 Poll of the Week
Have you ever received a suspicious SIM-related alert or lost cell signal unexpectedly? |
🙋 Author Spotlight
Meet Kaden Rourke - Senior Security Engineer
Kaden Rourke is a Senior Security Engineer with 12+ years of experience designing and implementing secure authentication systems used by millions of users worldwide. Before joining Everykey, Elias led identity engineering initiatives at two venture-backed SaaS companies and contributed to open-source projects focused on hardware-backed cryptography and decentralized access control.
✅ Wrapping Up
Your phone number is no longer just a point of contact — it’s the key to your digital identity.
That’s why SIM swapping has become one of the most dangerous cybercrimes of the decade — and why security leaders must move away from SMS-based authentication before attackers move in first.
Lock your number. Upgrade your MFA. And don’t let a phone call be the reason you lose everything.
Stay alert. Stay protected.
Until next time,




