
Authentication
Best Authentication Methods of 2026: MFA, Biometrics, Passkeys & More
How identity-first security, passwordless access, and adaptive authentication are shaping the future of secure access.

Authentication
How identity-first security, passwordless access, and adaptive authentication are shaping the future of secure access.

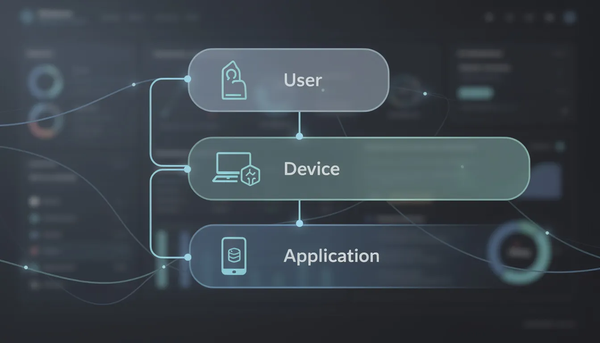
Identity and Access Management
A practical guide to how identity, access, and permissions work in modern digital systems.
Best Practices
A practical reference for modern authentication, identity verification, and secure access

Cyberattack
🔓 Unlocked - Edition #25 - Tuesday, February 17th, 2026

Cyberattack
A practical guide to modern cyber threats, attack methods, and how organizations defend against them.

Authentication
How forms-based authentication works, security risks, and best practices For modern web applications.

Best Practices
Practical password memory strategies for IT professionals and security-minded users.
Authentication
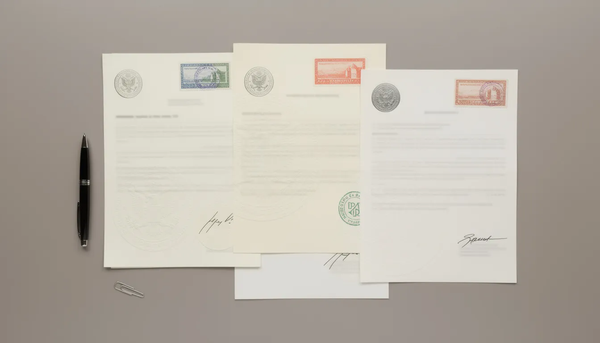
How document authentication, apostilles, and notarization enable legal recognition across borders.

Authentication
How authenticator apps protect online accounts with modern two factor authentication.Last updated: March 2026
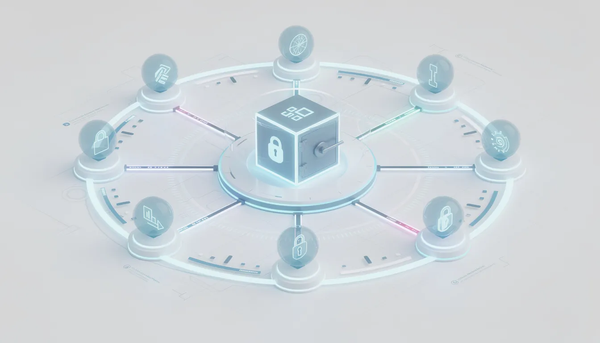
Privileged Access Management
A practical guide to PAM for IT professionals managing modern access risk.

Newsletter
🔓 Unlocked - Edition #24 - Tuesday, February 10th, 2026
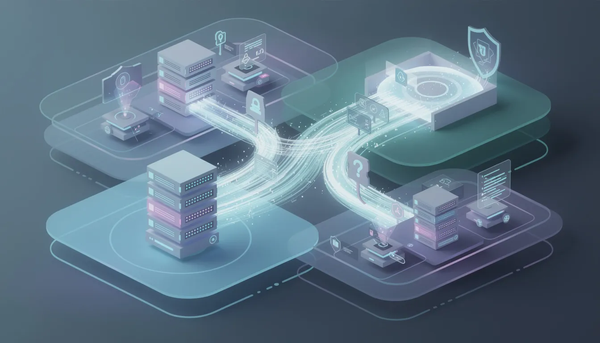
Cybersecurity Tools
An objective overview of technologies shaping modern cyber defense.