best practices
Understanding Cryptographic Authentication: Methods and Best Practices
Explore key methods and best practices in cryptographic authentication to enhance your security.
best practices
Explore key methods and best practices in cryptographic authentication to enhance your security.

cyberattack
A technical analysis of the increase in cyberattacks, emerging cybersecurity threats, ransomware trends, AI driven threats, and strategies organizations can use to strengthen cyber resilience.

access control
Explore the latest access control tech solutions that boost security and streamline operations. Discover effective strategies to enhance your safety.

best practices
How the pillars of cybersecurity strengthen risk management, protect sensitive data, and support business continuity.
best practices
Discover the importance of two-factor authentication (2FA) for protecting your online accounts.

newsletter
🔓 Unlocked - Edition #28 - Tuesday, March 10th, 2026

cybersecurity policy
How a SOC for cybersecurity strengthens risk management, proves compliance, and improves organizational resilience.

privileged access management
Learn how Azure Privileged Identity Management enhances security by managing access and roles effectively.

cybersecurity professionals
Discover key cybersecurity terms every professional needs to know to enhance your understanding and protect your organization.

cyberattack
How nation-state cyber operations, advanced persistent threats, and cyber espionage groups target critical infrastructure and sensitive data.

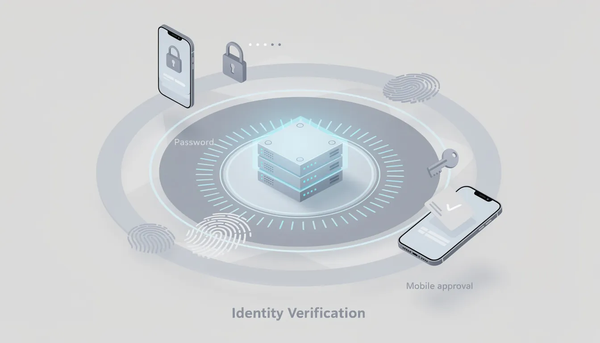
authentication
How continuous authentication improves identity verification, access confidence, and risk awareness across modern applications.

cybersecurity by industry
How financial institutions can test password effectiveness and strengthen access to protect sensitive financial data in a rapidly evolving threat landscape.