Types of Cyber Attacks in 2026: What IT Teams Must Know
Cyber attacks in 2026 are faster, smarter, and harder to attribute. This breakdown covers the most active attack types — ransomware, phishing, supply chain compromises, credential theft, and AI-assisted attacks — with what IT teams need to detect and defend against each one.

Introduction
The types of cyber attacks in 2026 are evolving to be faster, more automated, and highly personalized, driven by AI-powered “Agentic” systems and advanced social engineering. The cybersecurity threat landscape in 2026 is characterized by the increasing complexity and speed of attacks, often outpacing traditional defenses.
With the rapid evolution of cyber threats in 2026, IT teams must stay informed to effectively defend their organizations. Understanding the types of cyber attacks in 2026 is especially important for IT teams because it enables them to proactively protect sensitive data, maintain uptime, and respond effectively when incidents occur.
Internet attacks in 2026 include phishing, ransomware, malware, and DDoS. For IT professionals, understanding the types of cyber attacks in 2026 is critical for protecting sensitive data, maintaining uptime, and responding effectively when incidents occur. This guide is designed for IT professionals and teams who need to understand the evolving landscape of internet attacks in 2026.
The threat landscape in 2026 is rapidly changing, with new and sophisticated attack vectors emerging. An attack vector is any pathway or method used by cyber attackers to infiltrate organizations, including human factors (like social engineering), supply chain vulnerabilities, third-party dependencies, and technological weaknesses in infrastructure and software.
Understanding this evolving threat landscape and the various attack vectors is crucial for effective detection, defense, and mitigation strategies. It covers the most common attack types, their methods, and strategies for defense, helping organizations stay secure in a rapidly changing threat environment.
Internet connectivity has become foundational to modern business operations, cloud services, and government systems. At the same time, it has dramatically expanded the attack surface. Cybercriminals, nation-state actors, and opportunistic threat actors now exploit vulnerabilities across networks, applications, identities, and user behavior.
The protection of corporate data is more critical than ever, as insider threats, state-sponsored attacks, and espionage increasingly target sensitive corporate data.
AI-driven automation has made internet attacks faster and harder to detect as of 2026. In 2026, cyber attacks are evolving to be faster, more automated, and highly personalized, driven by artificial intelligence (AI)-powered “Agentic” systems and advanced social engineering. Artificial intelligence enables cybercriminals to conduct more sophisticated, adaptive, and personalized attacks, while also playing a dual role in both attack and defense strategies.
These advances are amplifying overall cyber risk, requiring security leaders to adapt their strategies and prioritize operational resilience. Adversaries weaponize and target AI at scale, forcing organizations to rethink how they secure access, users, and systems. AI-driven malware and tools can learn from their environment and adapt to evade detection, making them more dangerous than traditional threats. Self-evolving malware can analyze its environment in real-time and morph its own code to evade detection, while autonomous attack chains managed by AI swarms can collapse the time from compromise to action from hours to seconds.
Many cyberattacks are motivated by financial gain, such as stealing confidential information or demanding ransoms. Advanced persistent threats (APTs) are another significant concern, where threat actors maintain persistent access to organizational systems through sophisticated methods. Intellectual property theft is a key motivation for these advanced persistent threats, as nation-state actors and cybercriminals seek to steal valuable proprietary information for economic or geopolitical advantage. Understanding adversary tactics is essential, and frameworks like MITRE ATT&CK help map real-world attacker behaviors, techniques, and tactics to improve detection and defense strategies.
Major categories of internet attacks include malware, social engineering, DDoS, and injection attacks. Key threats in 2026 include sophisticated deepfake voice/video phishing, AI-driven malware, and ransomware-as-a-service, with a growing focus on software supply chain breaches, critical infrastructure disruption, identity theft, and the compromise of critical assets. These attacks use various attack methods, such as phishing, ransomware, and SQL injection, to infiltrate systems. They vary in sophistication, intent, and impact, but all aim to gain access, steal data, or disrupt operations.
The primary attack vector in 2026 is identity, as attackers increasingly target stolen credentials instead of bypassing technical defenses — attackers now log in rather than break in. Identity-based attacks have emerged as the predominant threat vector in 2026. 75% of breaches now involve compromised identities using valid credentials.
Effective risk management is essential for identifying, assessing, and mitigating cyber risk in this environment. Security leaders must prioritize security at every stage and level of their activities, including human factors, to mitigate cybersecurity threats and protect critical assets. Organizations must prioritize identity infrastructure modernization and FIDO2/WebAuthn adoption to combat identity-based attacks. Organizations that experience fewer credential-based incidents are those that consistently enforce phishing-resistant multi-factor authentication and apply strong identity management practices. Cyber hygiene improvement means the adoption of simple security practices like software updates, strong and unique passwords, and multi-factor authentication.
In 2026, emerging threats are expected to challenge organizations further, especially as social engineering attacks increasingly exploit human behavior, making them difficult to detect and counter. Traditional defenses, such as perimeter security and reactive patching, are no longer sufficient against these evolving and sophisticated threats. Proactive, integrated security approaches that cover all stages of the software development lifecycle are now essential. AI-related vulnerabilities are reported as the fastest-growing cyber risk by 87% of organizations, aligning with broader cybersecurity predictions for 2026 that emphasize AI’s dual role in attack and defense. The growing demand for cybersecurity professionals highlights the need for expertise in areas like AI threat analysis, network defense, and evolving security challenges. Cybersecurity professionals must adapt to technological advances such as AI, cloud security, and quantum computing to effectively respond to the changing threat landscape.
As quantum computing advances, state-level actors are increasingly stockpiling encrypted data with the intention to decrypt it once quantum computers become viable — a strategy known as "Harvest Now, Decrypt Later." This means that encrypted data stolen today could be compromised in the future, making it critical for organizations to prepare cryptographic transitions to safeguard sensitive information against future decryption efforts.
Summary of Major Internet Attack Types
Below is a general overview of the most common and emerging types of internet attacks in 2026. This section provides a foundation before diving into specific attack types in detail.
- Malware Attacks: Harmful software such as viruses, trojans, ransomware, and spyware.
- Social Engineering Attacks: Manipulation of individuals to disclose confidential information.
- Phishing Attacks: Deceptive attempts to trick users into revealing sensitive data.
- Deepfake Phishing: Sophisticated phishing attacks using AI-generated voice or video to impersonate trusted individuals or executives, making social engineering more convincing and harder to detect.
- Ransomware Attacks: Malware that encrypts data and demands payment for release.
- Ransomware-as-a-Service (RaaS): A business model where cybercriminals lease ransomware tools to affiliates, enabling widespread and scalable ransomware attacks even by less technically skilled attackers.
- DDoS (Distributed Denial of Service) Attacks: Overwhelming systems with traffic to disrupt operations.
- Injection Attacks: Inserting malicious code (e.g., SQL injection) into vulnerable applications.
- Brute-Force Attacks: Repeated attempts to guess passwords or credentials.
- Man-in-the-Middle Attacks: Intercepting communications to steal information.
- Insider Threats: Malicious or accidental actions by individuals within the organization.
- Supply Chain Attacks: Compromising vendors or partners to infiltrate organizations.
- Software Supply Chain Attacks: Targeting the software development and distribution process by infiltrating software supply chains, including the vendor’s network, development pipeline, or through compromised tools and dependencies. The complexity and interconnectedness of modern software supply chains introduce significant security vulnerabilities.
Supply chain attacks have increased sharply, with incidents quadrupling over the past five years. In 2026, 70% of organizations express concern about cybersecurity risks in their supply chain.
Cyberattacks can target a wide range of victims from individual users to enterprises or even governments. When targeting businesses or other organizations, the hacker’s goal is usually to access sensitive and valuable company resources, such as intellectual property, customer data or payment details. Attackers often exploit vulnerabilities to compromise systems and gain unauthorized access.
Emerging Attack Types in 2026: What’s New?
2026 is defined by an AI arms race in cybersecurity.
- Cyber attacks are now faster, more automated, and highly personalized, driven by AI-powered “Agentic” systems and advanced social engineering.
- Key threats include:
- Deepfake voice/video phishing: AI-generated impersonations for highly convincing social engineering.
- AI-driven malware: Self-evolving malware that adapts to evade detection.
- Ransomware-as-a-Service (RaaS): Ransomware tools leased to affiliates, enabling scalable attacks.
- Software supply chain breaches: Attacks targeting third-party vendors and dependencies.
- Critical infrastructure disruption: Targeting essential services and utilities.
- Identity theft and compromise: Attackers increasingly log in with stolen credentials rather than break in.
- The cybersecurity landscape is now an AI arms race, with adversaries using automated, agentic AI to launch hyper-personalized social engineering and adaptive malware attacks.
Types of Cyber Attacks
Cyber attacks encompass any malicious activity designed to compromise computer systems, networks, or user accounts.
Malware
Malware is a general term for malicious software that infects a computer and changes how it functions, destroys data, or spies on the user. A malicious program, such as a Trojan horse, can disguise itself as a legitimate application to deceive users and infiltrate computer systems. Some malware is specifically designed to establish persistent backdoors or vulnerabilities, enabling attackers to exploit these weaknesses in future attacks.
Malware attacks can infiltrate systems, steal data, disrupt operations, or serve as a payload for other attacks.
Ransomware
Ransomware attacks can disrupt operations, encrypt data, and demand ransoms, causing significant financial losses to organizations.
Identity Attacks
Identity-based attacks have emerged as the predominant threat vector in 2026. Identity has replaced the network perimeter as the primary target, with attackers logging in rather than breaking in. Attackers increasingly use stolen credentials to gain unauthorized access, making identity protection a top priority for IT teams.
Strong identity controls, such as multi-factor authentication and continuous monitoring, are critical for limiting the impact of vulnerabilities and reducing the risk of initial access. Notably, 97% of identity-based attacks involve passwords, yet only 46% of organizations have comprehensive visibility into all identities in their environment.
While there is a growing shift from traditional network intrusion methods to more identity-focused breaches, network intrusion remains a relevant threat in the evolving cybersecurity landscape.
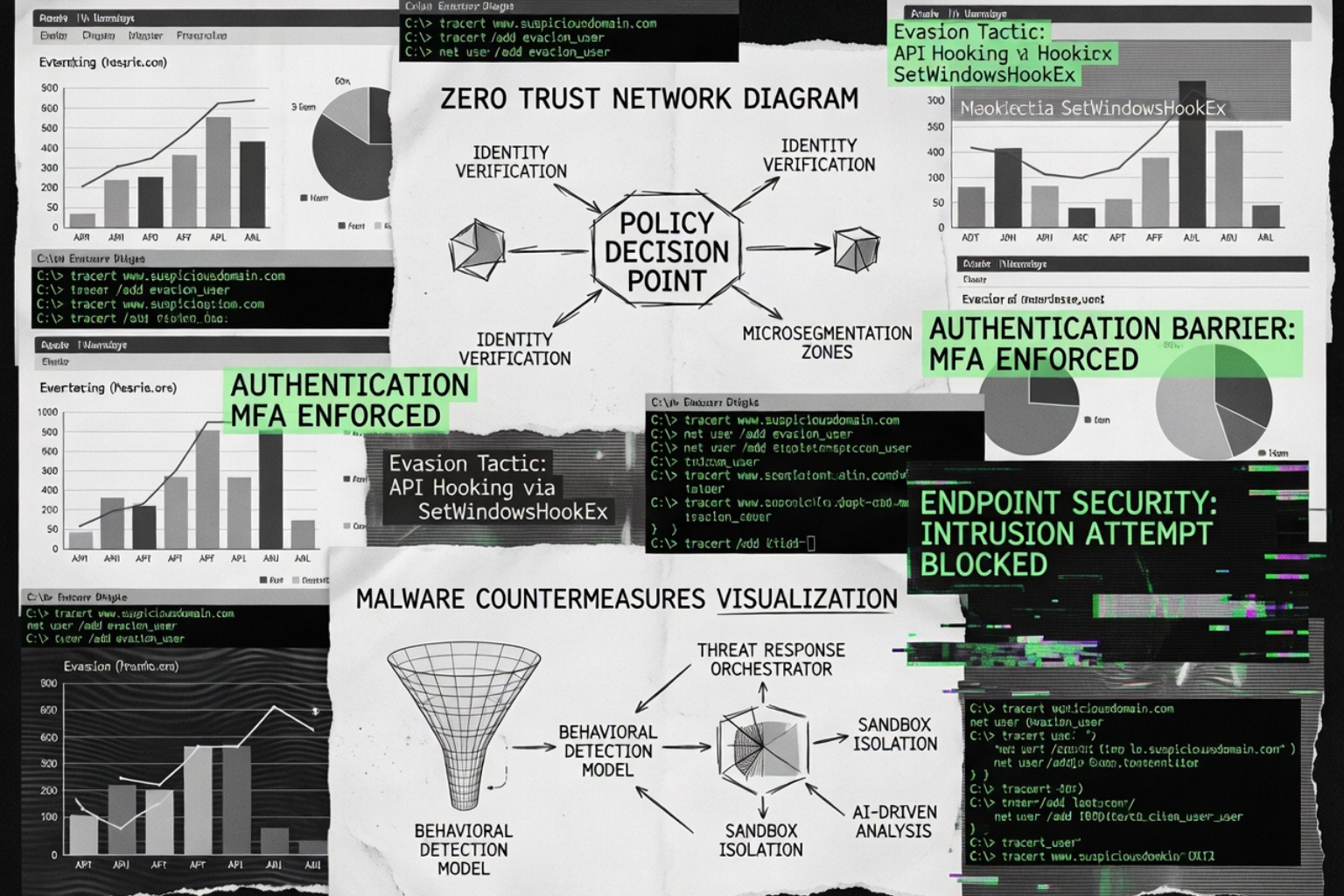
Employing a comprehensive cybersecurity strategy can help organizations prevent or quickly remediate cyberattacks and minimize the impact of these events on business operations. Adopting layered security practices — such as multi-factor authentication, Zero Trust architecture that requires continuous verification of user identities and access requests, and regular security awareness training — is essential to prevent and mitigate attacks. Zero Trust architecture has emerged as the primary response framework to identity-based attacks. It is also crucial to keep the operating system updated to prevent malware infections and cyberattacks that exploit system vulnerabilities.
Understanding the different forms of cyber attacks is the first step. Next, let’s explore what constitutes a cyber threat and how attackers exploit vulnerabilities.
Cyber Threat
A cyber threat refers to any circumstance or event with the potential to harm systems or data. Cybersecurity threats are constantly evolving, especially as cloud services, mobile devices, and remote work environments expand.
Attackers may send emails or links that appear to originate from the same organization to increase the likelihood of a successful phishing attack. Verifying that communications truly come from the same organization or domain is a crucial security measure to prevent such threats.
AI-Powered Threats
AI-powered attacks leverage AI and machine learning to gain access to networks or steal sensitive information. The deployment of 5G networks may lead to an uptick in IoT attacks as the number of connected devices grows.
Threat Intelligence and Detection
Threat intelligence helps security teams understand attacker tactics, techniques, and procedures so they can prioritize defenses. Comprehensive threat detection and proactive threat mitigation strategies, such as behavior-based monitoring and secure coding training, are essential for identifying and reducing advanced threats across multiple attack surfaces.
Security Awareness
Regular security awareness training is also critical, as it addresses the human element in breaches and significantly improves both threat detection and prevention.
Recognizing cyber threats is essential, but understanding how attackers gain access — such as through brute-force attacks — is equally important. Let’s examine brute-force attacks next.
Brute-Force Attacks
Definition
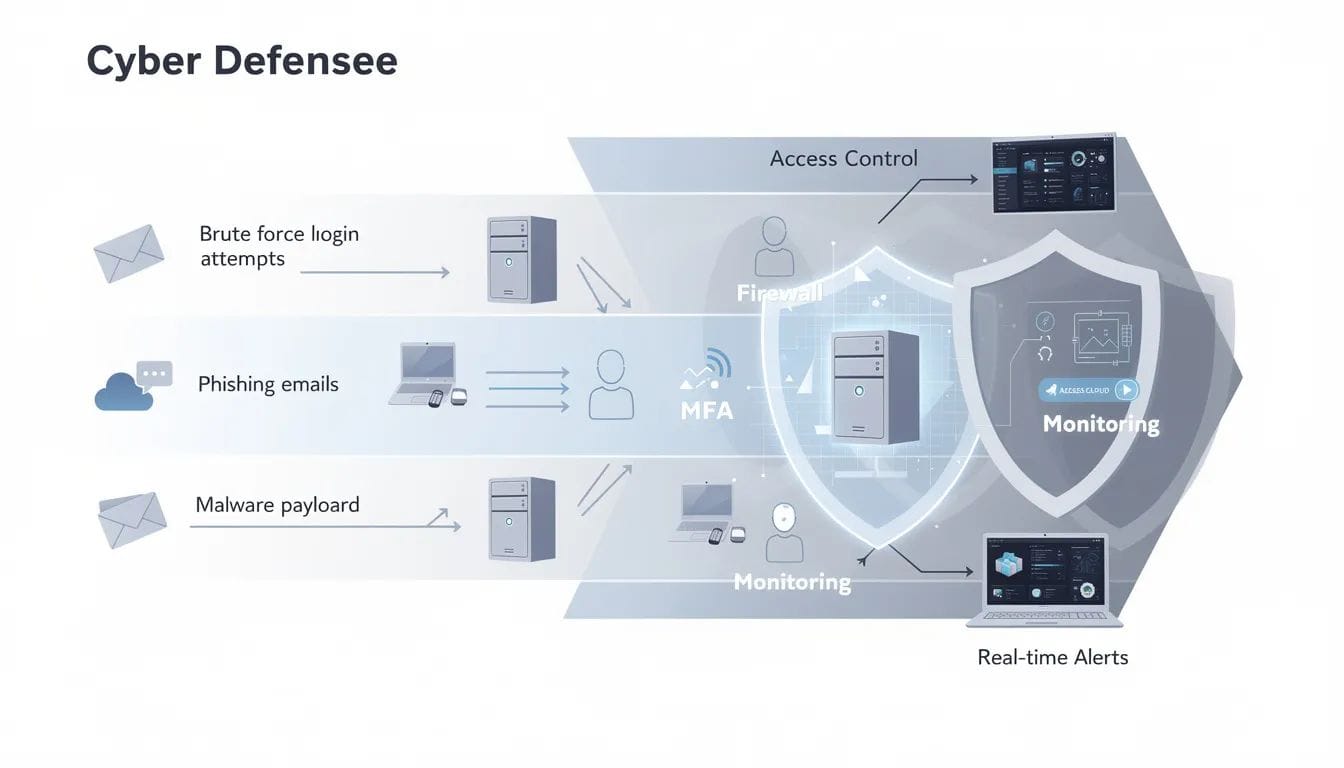
Brute-force attacks involve repeatedly trying different password combinations to gain unauthorized access to accounts. In a brute-force attack, the attacker simply tries to guess the login credentials of someone with access to the target system. These attacks are especially dangerous for remote users who rely on exposed logins, making MFA solutions for remote workers an important safeguard.
A brute-force attack can also include techniques like password spraying or credential stuffing. Credential theft often involves using stolen passwords to log in as legitimate users.
Implementing multi-factor authentication (MFA) can enhance user access security and mitigate potentially successful brute-force attacks. Weak authentication such as relying on simple passwords exposes systems to brute-force, phishing, and credential stuffing attacks.
Brute Force Techniques
Brute force techniques are particularly effective against reused or weak passwords. Using strong passwords and enforcing access controls significantly reduces the likelihood of success. Applying least privilege access principles further limits the risk of unauthorized access from brute-force attacks by ensuring users and third-party integrations only have the minimum permissions necessary.
Regular patch management is essential to fix software vulnerabilities and prevent their exploitation, especially when authentication systems rely on outdated components.
Brute-force attacks are just one way attackers compromise systems. Another common method is exploiting vulnerabilities in web applications, such as through cross-site scripting (XSS) attacks.
Cross-Site Scripting (XSS)
Definition
Cross-site scripting (XSS) attacks involve transmitting malicious scripts to a user's browser, which executes the script when the user interacts with it. These attacks often occur when applications fail to properly validate input.
XSS attacks can lead to stolen login credentials, session hijacking, and unauthorized access to internal systems.
Beyond brute-force and XSS attacks, organizations must also be aware of broader cybersecurity threats, including social engineering and phishing.
Cybersecurity Threats
Cybersecurity threats extend beyond malware. Social engineering manipulates individuals into disclosing confidential information. Phishing is a deceptive attack where cybercriminals impersonate legitimate entities to trick individuals into revealing sensitive information.
Phishing and Social Engineering
Phishing attacks combine social engineering and technology to trick individuals into revealing sensitive information. Business email compromise is a form of social engineering where attackers impersonate executives or trusted contacts to deceive employees into transferring funds or sensitive data. Attackers increasingly use AI tools to create sophisticated phishing and social engineering attacks, representing a new wave of AI-driven cyber threats. AI-generated phishing campaigns can produce highly personalized messages that are harder for recipients to detect.
Employee Training
Organizations can enable employees through security awareness and identity protection measures, helping to prevent fraud by combining informed users with strong technical controls. Security training for employees can raise awareness about phishing and social engineering attacks.
Phishing and social engineering are major threats, but attackers also use technical means to disrupt operations, such as DDoS attacks. Let’s look at how denial-of-service attacks work.
DDoS Attack
Definition
Denial-of-Service (DoS) attacks overwhelm a system with fraudulent traffic to disrupt operations. A denial-of-service (DoS) attack is designed to overwhelm the resources of a system to the point where it is unable to reply to legitimate service requests.
In a DoS attack, users are unable to perform routine and necessary tasks, such as accessing email, websites, online accounts or other resources that are operated by a compromised computer or network.
DoS attacks cost the organization time, money and other resources in order to restore critical business operations.
Denial of Service
A Denial-of-Service (DoS) attack is a malicious, targeted attack that floods a network with false requests in order to disrupt business operations. These attacks often target web services, APIs, or cloud platforms.
Monitoring network traffic is crucial for detecting threats and understanding their context and impact. Implementing network segmentation can further limit the spread and impact of attacks by containing malware and restricting lateral movement within the network.
Distributed Denial
Distributed Denial of Service (DDoS) attacks are similar to DoS attacks but originate from multiple systems, making them harder to block. A distributed denial-of-service (DDoS) attack is initiated by a vast array of malware-infected host machines controlled by the attacker.
Using firewalls and intrusion detection/prevention systems (IDS/IPS) can help filter network traffic and block unwanted connections.
Denial of Service Attack
Distributed denial-of-service (DDoS) attacks often leverage botnets composed of multiple computers across the same network or globally distributed environments.
Segregating your network into zones based on security requirements can limit the potential impact of an attack.
Denial of Service DDoS
DDoS attacks frequently target critical infrastructure, government agencies, and cloud services. Operational paralysis from attacks like ransomware can lead to massive revenue losses.
Organizations should implement incident response plans to regain control quickly.
DDoS attacks can cripple operations, but attackers also use code injection and other technical exploits. Next, we’ll explore injection attacks and other cybersecurity attack methods.
Cybersecurity Attacks
Injection Attacks
Code injection attacks involve inserting malicious code into a vulnerable application to change its behavior. A common example is the sql injection attack, where an attacker inserts malicious SQL code into a vulnerable application to exploit weaknesses in websites that rely on databases. This can lead to data leaks or system disruptions. Implementing a least-privileged access model is an effective way to mitigate the risk of sql injection attacks.
Drive-by attacks occur when a hacker embeds malicious code into an insecure website, which automatically infects a user’s computer upon visiting the site.
Technical exploits like injection attacks are dangerous, but attackers can also intercept communications. Let’s review man-in-the-middle attacks and network-based threats.
Man-in-the-Middle Attacks
Definition
Man-in-the-Middle (MITM) attacks involve intercepting communications between two parties to steal sensitive information. In a man-in-the-middle attack, the attacker positions themselves in the middle of the communication between two parties to intercept data.
Session hijacking is a type of man-in-the-middle attack where the attacker takes over a session between a client and the server.
Network-based attacks can be subtle and hard to detect. Next, we’ll look at DNS and network attacks that can redirect or exfiltrate data.
DNS and Network Attacks
DNS tunneling is a technique used by attackers to bypass network security by encapsulating non-DNS traffic within DNS packets. This technique is often used by malicious actors to facilitate data theft and exfiltration of sensitive information. In a DNS spoofing attack, a hacker alters DNS records to send traffic to a fake or spoofed website.
Using deception technology can help detect threats by creating decoys across the network to observe attackers’ plans and techniques.
While external threats are significant, organizations must also guard against risks from within. Insider threats are a growing concern.
Insider Threats
Definition
Insider threats involve individuals within an organization who misuse their access or privileges to harm the organization. Insider threats may also be unintentional or intentional, with unintentional threats involving accidental leaks of sensitive information.
Organizations should implement a comprehensive cybersecurity training program that teaches stakeholders to be aware of any potential attacks, including those potentially performed by an insider.
Insider threats can be difficult to detect, but supply chain attacks can bypass even the best internal controls. Let’s examine how attackers exploit third-party relationships.
Supply Chain Attacks
Definition
Supply chain attacks target an organization's vendors or partners to compromise their products or services. These attacks often bypass perimeter defenses and exploit trust relationships.
Regular audits and vendor assessments help reduce exposure to this risk.
Supply chain attacks are on the rise, but malware remains a persistent threat. Next, we’ll break down the types of malware and how to defend against them.
Malware Attacks
Definition
Malware is a common type of cyberattack that encompasses various harmful software, including ransomware, trojans, and viruses.
Malware attacks are a persistent and evolving threat to organizations of all sizes. These attacks use malicious software to infiltrate computer systems, steal data, or disrupt operations. Cyber criminals deploy malware through various channels, such as phishing emails, compromised websites, or by exploiting vulnerabilities in legitimate software.
Types of Malware
Common types of malware include:
- Viruses: Malicious code that attaches to legitimate files and spreads to other files or systems.
- Worms: Self-replicating malware that spreads across networks without user intervention.
- Trojans: Malicious programs disguised as legitimate software.
- Ransomware: Encrypts files and demands payment for their release.
- Spyware: Silently collects sensitive information from user devices.
Prevention Measures
To defend against malware attacks, organizations should:
- Implement up-to-date antivirus solutions and firewalls.
- Regularly patch operating systems and applications.
- Conduct proactive monitoring for suspicious activity.
- Educate employees to prevent the installation and spread of harmful software.
Malware is a broad category, but phishing attacks are among the most common entry points. Let’s look at how phishing works and how to prevent it.
Phishing Attacks
Definition
Phishing is a deceptive attack where cybercriminals impersonate legitimate entities to trick individuals into revealing sensitive information.
Phishing attacks remain one of the most prevalent social engineering techniques used by cyber criminals to steal sensitive information. These attacks typically involve phishing attempts via email, text messages, or phone calls that impersonate trusted organizations or individuals.
Methods
- Directing users to fake websites that mimic legitimate ones.
- Requesting login credentials, financial details, or confidential information.
- Installing malicious software on user devices through deceptive links or attachments.
Prevention
To reduce the risk of falling victim to phishing attacks, organizations should:
- Educate employees about recognizing suspicious messages.
- Encourage the use of multi-factor authentication.
- Ensure all software is regularly updated to close security gaps.
- Employ layered security controls for defense.
Phishing attacks can lead to major incidents. Having a robust incident response plan is essential for minimizing damage and recovering quickly.
Incident Response Planning
Incident response planning is essential for organizations to effectively address and recover from cyber attacks. Integrating risk management into incident response planning helps organizations identify, assess, and mitigate cybersecurity risks, ensuring that response strategies are aligned with evolving threats and regulations. A well-developed incident response plan enables security teams to quickly identify, contain, and remediate various types of cyber threats, minimizing damage and downtime.
Key Components
- Clear procedures for detection, containment, eradication, and recovery.
- Guidelines for communication and post-incident analysis.
Training and Simulation
- Regular training and simulation exercises to prepare security teams for evolving threats.
- Continuous updates and testing of incident response strategies to strengthen security posture.
Incident response is critical, but proactive cloud security measures are also necessary as organizations increasingly rely on cloud infrastructure.
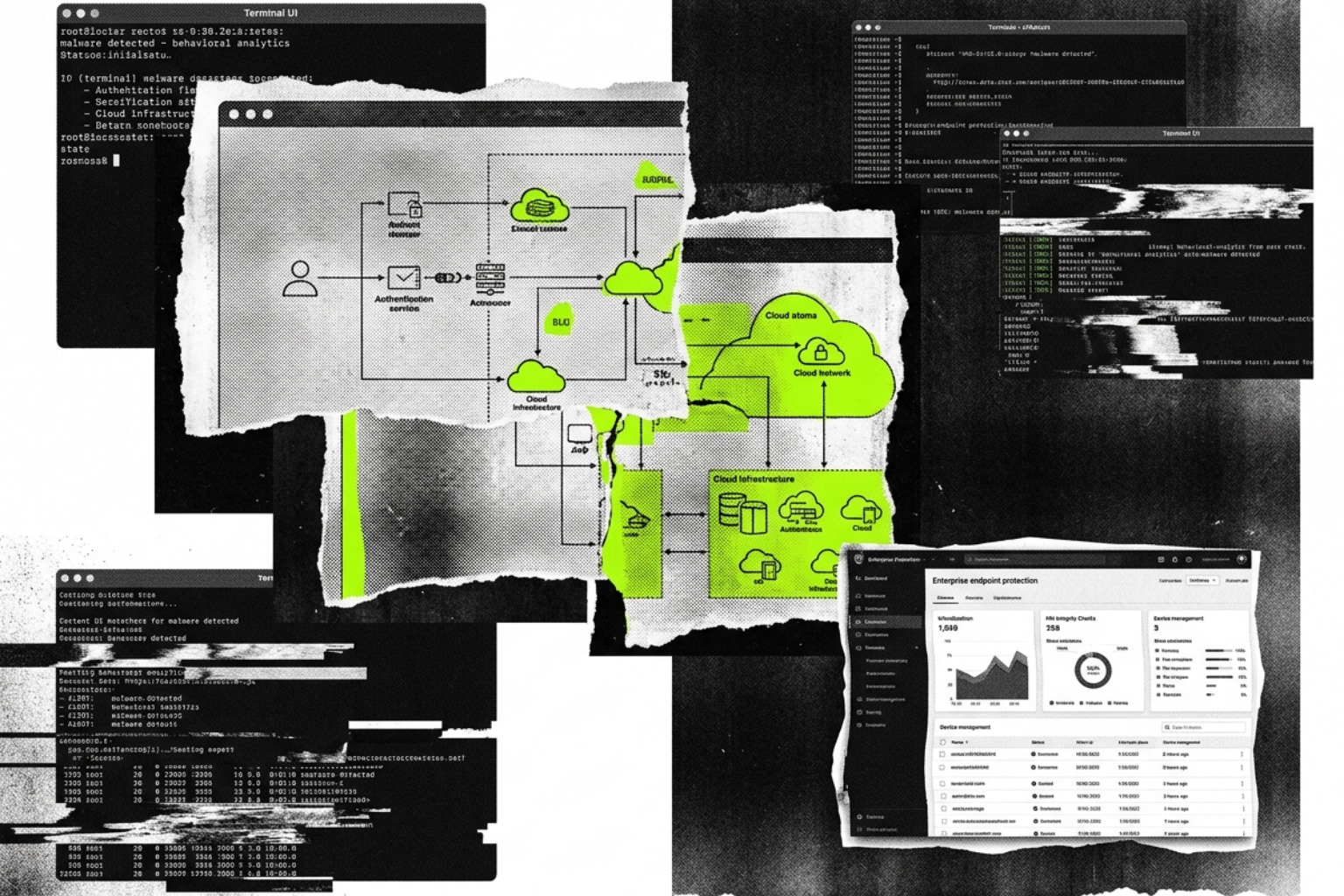
Cloud Security Measures
As organizations increasingly rely on cloud computing, robust cloud security measures are vital to protect against cyber threats. Protecting critical assets — such as sensitive data and essential business resources — in cloud environments is essential, as misconfigurations or mismanaged identities can expose these assets to breaches.
Effective cloud security involves:
- Implementing multi-factor authentication to secure access.
- Encrypting sensitive data both in transit and at rest.
- Regularly reviewing cloud configurations for vulnerabilities.
- Strong configuration management, including centralized monitoring and automation, to reduce misconfiguration risks and ensure system security.
Continuous monitoring of cloud resources helps detect suspicious activity and enables rapid incident response to potential breaches. Continuous verification of user identities, device integrity, and access permissions is a key component of Zero Trust architecture, helping to prevent identity-based attacks and reduce security blind spots. Implementing a Zero Trust architecture, which assumes a breach and requires ongoing continuous verification, is a proactive step toward reducing the risks associated with remote work.
Recognize that cloud security is a shared responsibility between the provider and the customer — both must take proactive steps to secure their respective environments.
By adopting best practices and maintaining a strong incident response plan, organizations can safeguard their cloud assets against unauthorized access and other cybersecurity threats.
Cloud environments are not the only area of concern. The rapid growth of IoT devices introduces new security challenges that organizations must address.
IoT Security Considerations
The rapid growth of Internet of Things (IoT) devices introduces new security challenges for organizations. These devices, from smart sensors to industrial controllers, can be targeted by cyber attacks aiming to gain unauthorized access, steal data, or disrupt operations. Many IoT devices connect directly to cloud infrastructure, which increases the risk of security vulnerabilities that attackers can exploit if proper protections are not in place.
Common Threats
- Exploiting weak default passwords.
- Attacking outdated firmware or unpatched vulnerabilities.
- Moving laterally within the same network after compromising IoT devices.
Prevention
To address these evolving threats, organizations should:
- Enforce strong authentication for all IoT devices.
- Regularly update device software and firmware.
- Segment IoT devices from critical internal systems.
- Conduct regular security assessments and deploy IoT-specific security solutions.
IoT security is just one aspect of a comprehensive defense. Next, we’ll summarize key defense and prevention strategies for all types of cyber attacks.
Defense and Prevention Strategies
Employing a comprehensive cybersecurity strategy can help organizations prevent or quickly remediate various security threats, including different types of internet attacks. Security breaches can result from vulnerabilities, insider threats, or cyber attacks, and highlight the importance of proactive security measures to protect data integrity.
A layered defense should include comprehensive security tools, not just single-point solutions, to address evolving threats and vulnerabilities. Organizations cannot defend against threats they cannot see, making visibility into third-party connections essential. In fact, 85% of Chief Information Security Officers (CISOs) lack complete visibility into their threat landscape, making supply chain attacks particularly dangerous.
Key Layered Defenses
- Identity and Access Controls:
- Implement strong identity management practices.
- Enforce phishing-resistant multi-factor authentication.
- Apply Zero Trust principles with continuous verification of user identities, device integrity, and access permissions.
- Use credential managers and identity-first access platforms.
- Training and Awareness:
- Conduct regular security awareness training for employees.
- Run simulation exercises and incident response drills.
- Technical Controls:
- Utilize network security controls (firewalls, IDS/IPS).
- Apply regular software updates and vulnerability management.
- Monitor networks and systems for threats.
- Segment networks to limit lateral movement.
- Incident Response:
- Develop and maintain incident response plans.
- Test and update response strategies regularly.
- Supply Chain and Development Security:
- Implement systematic controls across all development stages.
- Audit vendors and third-party dependencies.
Access-based controls play a growing role. Platforms like EveryKey support identity-first access by continuously confirming presence and user legitimacy, helping reduce the risk of stolen credentials being used to gain unauthorized access.
By implementing these layered defenses, organizations can significantly reduce their risk exposure and improve their resilience against the evolving threat landscape of 2026.
Conclusion
Internet attacks are growing in scale, speed, and sophistication. From brute-force attacks and phishing to ransomware and DDoS, organizations face constant pressure to protect systems, data, and users.
Understanding the types of internet attacks allows IT professionals to design better defenses, improve response times, and reduce overall risk. Strong access controls, employee training, continuous monitoring, and identity-focused strategies remain essential in 2026 and beyond.
As cyber threats evolve, organizations must adopt comprehensive security programs that integrate the latest security tools and practices. This includes implementing identity and access management solutions that enforce least privilege access and require continuous verification to prevent unauthorized entry. Security strategies should also focus on mitigating risks from third party compromises and supply chain attacks, which are increasingly exploited by threat actors to gain access to critical infrastructure and sensitive data.
Moreover, fostering a culture of security awareness through regular training empowers employees to recognize and respond to social engineering attacks, reducing the human element vulnerability. Leveraging AI-driven threat intelligence and continuous monitoring enhances the ability of security teams to detect and respond to actual attacks swiftly.
In this dynamic threat landscape, adopting modern attacks defense mechanisms such as Zero Trust architecture and cloud security best practices is vital. Organizations that proactively manage their attack surface and continuously update their security posture will be better positioned to withstand the sophisticated cyber attacks of 2026 and beyond.
FAQ: Types of Internet Attacks
What are the most common types of internet attacks?
The most common types of internet attacks are:
- Malware
- Phishing
- Brute-force attacks
- DDoS
- Injection attacks
How do attackers usually gain access?
Attacks gain access primarily through:
- Stolen credentials
- Phishing
- Weak passwords
- Misconfigurations
- Exploited vulnerabilities
Why is MFA important?
Implementing multi-factor authentication (MFA) can enhance user access security and mitigate potentially successful brute-force attacks.
Are insider threats always malicious?
No. Insider threats may also be unintentional, such as accidental data sharing or misconfigurations.
How can organizations reduce risk?
Organizations can reduce risk by:
- Training employees
- Patching systems
- Network monitoring
- Identity-based access controls
- Incident response planning