This guide is designed for enterprise IT and security leaders seeking to understand the evolving landscape of cloud identity management, the challenges of multi-cloud environments, and the leading solutions available in 2026. Choosing the right cloud identity manager is foundational to enterprise security, operational efficiency, and regulatory compliance in 2026.
Cloud Identity Management (CIM) refers to the frameworks and technologies that ensure the right individuals have appropriate access to technology resources in cloud environments. Cloud IAM centers on three primary concepts: Identity, authentication, and authorization. Cloud IAM enables organizations to securely control user access to resources through a comprehensive framework of policies, processes, and tools.
Cloud Identity Manager

The best cloud identity manager platforms in 2026 are built for scale, flexibility, and unified identity governance. Cloud-based solutions, such as third-party IDaaS platforms, offer centralized identity management across multiple cloud environments, unifying authentication, access control, and governance through a single cloud-hosted console.
Cloud IAM centers on three primary concepts: Identity, authentication, and authorization. These platforms manage digital identities and provisioning users as part of the identity lifecycle, enabling secure, scalable, and centralized identity governance and access management. Cloud IAM solutions help organizations manage user identities across multiple platforms, improving security and compliance.
Cloud identity managers scale to support millions of identities without additional hardware, unlike traditional on-premises systems. These solutions help organizations manage access efficiently and securely at scale. Cloud IAM solutions reduce CapEx by eliminating the need for on-premise servers and software, and they often provide more predictable OpEx through subscription-based pricing.
Cloud-native architectures allow for agility and scalability, adapting easily to growing workforces and new application integrations.
Next, we examine the unique challenges and requirements of managing identities in diverse cloud environments.
Cloud Environments
Managing user identities and access permissions has become a critical component of organizational security in multi-cloud environments.
Organizations face challenges in managing identities effectively in multi-cloud environments due to fragmented identity silos and inconsistent policies. Integrating cloud IAM with existing on-premises systems can expand the attack surface and complicate identity synchronization across environments. Additionally, compliance management becomes more complex in multi-cloud environments, requiring unified auditing and automated compliance checks.
A centralized approach to identity governance is essential in multi-cloud environments to maintain consistent access control policies and control access to cloud infrastructure and resources across all platforms. Implementing centralized identity governance is essential in multi-cloud environments to maintain a single source of truth for identity information.
Unified identity governance is essential in multi-cloud environments to maintain a single source of truth for identity information and ensure consistent access control policies.
With these challenges in mind, let’s explore how cloud identity is defined and managed across platforms.
Cloud Identity
Cloud identity refers to digital representations of user identities, devices, and services across cloud platforms.
Federated identity solutions allow users to authenticate through a trusted identity provider, enabling secure access across multiple cloud platforms. Federated identity management allows users to authenticate through a trusted identity provider, eliminating the need to maintain separate credentials for each cloud environment.
Technologies such as Security Assertion Markup Language and OpenID Connect enable single sign-on (SSO) best practices across multiple systems and multiple platforms. Single Sign-On allows users to access multiple applications with one set of credentials, reducing password fatigue.
Cloud IAM solutions should integrate with existing directories and identity providers to enable centralized identity management. A centralized identity repository integrates with on-premises directories, syncing user profiles and attributes across the organization.
Understanding identity management is the next step in building a secure and efficient cloud environment.
Identity Management
Implementing effective Cloud Identity Management enhances security and improves operational efficiency by streamlining access controls and reducing the risk of unauthorized access, aligning closely with broader identity and access management (IAM) practices. Multi-Factor Authentication (MFA) adds security by requiring two or more verification factors, such as biometrics or one-time codes.
Cloud IAM helps reduce an organization’s attack surface by tightening access controls and enforcing the principle of least privilege. Implementing least privilege access reduces organizational risk by ensuring users only have the access necessary to perform their tasks. The growing integration of AI and machine learning into cloud IAM systems enables more intelligent and proactive identity management.
Cloud IAM frameworks provide enhanced security postures by enforcing the principle of least privilege to limit potential breaches. Regular access reviews help identify violations of least privilege or dormant accounts.
Compliance and governance are critical challenges in cloud IAM, as organizations must demonstrate that access security controls are applied consistently and effectively. Biometric authentication methods are expected to rise sharply in adoption within cloud IAM platforms as they offer a combination of security and convenience.
The zero trust security model is also emerging as a key trend in cloud IAM, emphasizing strict access controls, continuous verification, and contextual policies.
With a solid understanding of identity management, let’s review the solutions that help enterprises address these needs.
Cloud Identity Management Solutions
The best cloud identity management solutions for enterprises in 2026 combine strong access management, identity governance, and seamless integration across multiple clouds.
Cloud IAM solutions help organizations manage user identities across platforms, addressing the complexity introduced by multiple cloud services.
Compliance readiness is facilitated by detailed logging and auditing required for regulations like GDPR and HIPAA. Every access decision in a cloud IAM system is recorded in immutable logs, aiding compliance and enabling real-time detection of anomalies. Audit logging and monitoring ensure traceability, accountability, and compliance in cloud IAM systems.
Identity as a Service is evolving into holistic access orchestration, managing identity lifecycle, policy enforcement, and risk analysis through advanced IAM tools.
Now, let’s look at the leading cloud identity management solutions available to enterprises in 2026.
Leading Cloud Identity Management Solutions for Enterprises in 2026
Below are the most widely adopted and enterprise-proven cloud identity management solutions in 2026, along with their key strengths.
Solution | Key Strengths |
|---|---|
Microsoft Entra ID | Deep integration with Microsoft 365 and Azure cloud infrastructure; Built-in multi-factor authentication and conditional access; Strong role-based access control and privileged access management; Identity governance and access reviews; Hybrid integration with existing systems. Ideal for enterprises heavily invested in Microsoft cloud platforms. |
Okta Workforce Identity Cloud | Robust identity provider capabilities; Extensive single sign-on (SSO) integrations; Automated user provisioning and lifecycle management; Context-aware access; Strong API and cloud services integration. Often selected for heterogeneous environments and multi-cloud strategies. |
Google Cloud IAM and Google Cloud Identity | Fine-grained access control within Google Cloud; Policy-based access management IAM; Native cloud identity controls; Scalable cloud infrastructure integration. Best suited for enterprises operating primarily in Google Cloud environments. |
Ping Identity | Strong federation and authentication mechanisms; Multi-cloud identity support; Identity governance capabilities; API security for multiple platforms. Well suited for regulated industries requiring strong identity verification. |
SailPoint Identity Security Cloud | Advanced identity governance; Continuous monitoring; Automated remediation tools; Detailed entitlement analytics. Strong choice for enterprises prioritizing compliance and governance. |
CyberArk Identity | Strong privileged access controls; Adaptive authentication; Detailed monitoring and logging; Risk-based access decisions. Ideal for enterprises managing sensitive data and privileged access. |
AWS IAM and AWS Identity Center | Deep integration with AWS cloud infrastructure; Fine-grained role-based access control; Native cloud provider policy management; Federation with external identity providers. Best for AWS-centric cloud environments. |
To help you compare these solutions at a glance, see the following table.
Comparison Table
Below is a simplified comparison of leading cloud identity management solutions for enterprises in 2026.
Solution | Best For | Multi Cloud Support | Identity Governance | MFA & SSO | Ideal Enterprise Size |
|---|---|---|---|---|---|
Microsoft Entra ID | Microsoft-centric enterprises | Moderate | Strong | Strong | Mid to Large |
Okta | Heterogeneous multi cloud | Strong | Moderate | Strong | Mid to Large |
Google Cloud IAM | Google Cloud environments | Limited outside GCP | Moderate | Strong | Mid to Large |
Ping Identity | Regulated industries | Strong | Strong | Strong | Large |
SailPoint | Governance-focused enterprises | Strong | Very Strong | Moderate | Large |
CyberArk | Privileged access heavy environments | Moderate | Strong | Strong | Large |
AWS IAM | AWS-native workloads | Limited outside AWS | Moderate | Strong | Mid to Large |
Next, we’ll discuss how automation and monitoring further enhance cloud identity management.
Automated User Provisioning
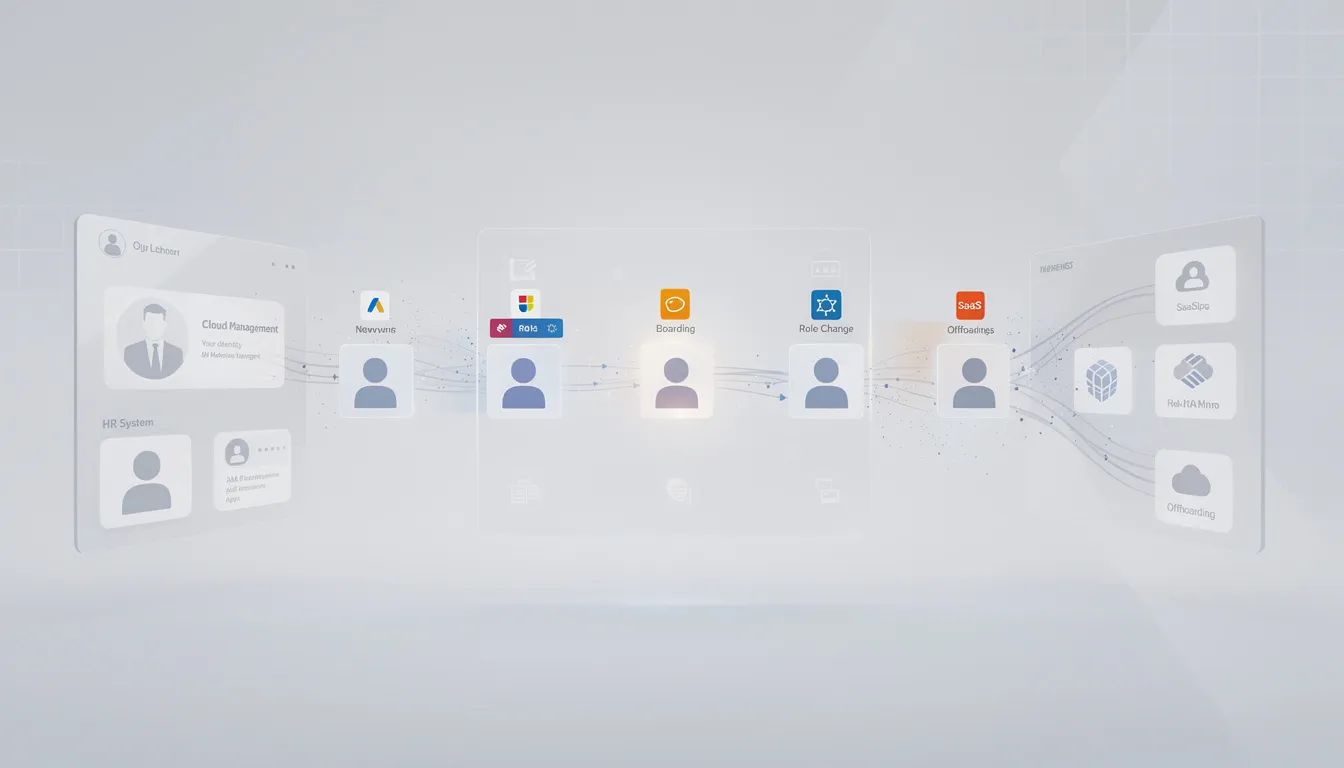
Automating user provisioning and deprovisioning ensures that users gain access quickly when they join and lose access promptly when they leave or change roles, with standards like SCIM for cross-domain identity management streamlining this lifecycle.
Cloud identity management automates user access management, reducing human error and improving operational efficiency. Automated remediation tools can identify and fix risky configurations and enforce least privilege principles across multiple clouds.
Automation is only effective when paired with robust monitoring, which we’ll cover next.
Continuous Monitoring
Continuous monitoring of identity-related activity is essential to detect misuse, unauthorized access, or unusual behavior.
User behavior analytics employs AI to detect anomalies in user activity that may indicate security breaches, especially when integrated into secure IAM frameworks. Insider threats remain a significant challenge for cloud IAM solutions, requiring deep visibility into user behavior and robust session logging.
Continuous monitoring supports secure access, which is a core function of cloud IAM.
Cloud Identity and Access
Cloud IAM plays a pivotal role in implementing Zero Trust security architectures, enabling organizations to enforce strict identity verification.
Adopting Zero Trust Architecture ensures that access is granted based on continuously verified identity signals. Zero Trust Architecture involves continuously verifying requests based on context rather than trusting by default.
Organizations must implement strong authentication practices consistently across all cloud environments to enhance security. Multi-Factor Authentication adds security by requiring two or more verification factors.
Role-based access control is another foundational element, which we’ll discuss next.
Role Based Access Control
Role-Based and Attribute-Based access control simplifies permission management based on user roles or dynamic attributes, forming the foundation of effective user access management.
Implementing least privilege access reduces organizational risk and strengthens enterprise security across cloud infrastructure.
As organizations expand to multi-cloud, unified identity governance becomes even more critical.
Multi Cloud
Multi cloud identity management is now essential. Managing multi-cloud environments introduces challenges due to different IAM models, terminology, and policy frameworks across cloud providers.
Unified identity governance is essential in multi-cloud environments to maintain consistent access control policies across all platforms.
Managing user identities across providers is a complex task, which we’ll address next.
User Identities
Managing user identities across multiple providers, multiple clouds, and multiple systems is complex. Cloud identity management helps organizations improve security, streamline access, and stay compliant in a complex threat landscape.
Secure access is the next critical area to consider.
Secure Access
Secure access depends on strong authentication, centralized governance, and continuous monitoring, making multifactor authentication in modern security a critical control.
Cloud IAM helps reduce security risks by controlling access permissions and enforcing the principle of least privilege. Adaptive and context-aware secure IAM systems are becoming essential components of modern cybersecurity strategies.
Access-focused platforms like EveryKey complement cloud IAM by strengthening authentication at the moment of access. By confirming user presence through proximity and continuously validating identity signals, EveryKey reinforces cloud identity workflows without adding friction for legitimate users.
Identity governance is essential for compliance and risk management, which we’ll discuss next.
Identity Governance
Compliance and governance are critical challenges in cloud IAM.
Regular audits, centralized logging, and automated remediation tools ensure consistent policy enforcement across multiple cloud environments and help organizations address multi-factor authentication vulnerabilities.
Data security is closely tied to identity management, as we’ll see in the next section.
Data Security
Data security in cloud environments depends on strong cloud identity and access management.
Data protection requires tight access controls, continuous monitoring, and enforcement of least privilege access across cloud services and cloud infrastructure, supported by robust multi factor authentication use cases.
Best Practices for Cloud Identity Management
Implementing effective cloud identity management starts with a foundation of least privilege access, ensuring that users are granted only the permissions necessary for their roles.
Principle of Least Privilege
Grant users only the permissions necessary for their roles to minimize risk.
Access Reviews
Regularly review and update access permissions to prevent privilege creep and reduce the risk of unauthorized access.
Multi-Factor Authentication
Enable multi-factor authentication (MFA) for all users, especially those with privileged access, to strengthen security in cloud environments.
Continuous Monitoring
Continuously monitor user activity and access requests to quickly detect and respond to suspicious behavior.
Automated Provisioning
Automate user provisioning and deprovisioning to streamline onboarding and offboarding, minimize manual errors, and ensure timely updates to user access.
Integration
Integrate cloud identity management with existing systems, such as HR systems, to enhance operational efficiency by automating user lifecycle management.
By following these best practices, organizations can maintain robust identity management, protect sensitive resources, and support secure cloud adoption.
Next, we’ll explore how cloud identity management supports compliance in complex environments.
Cloud Identity Management and Compliance
Enforcing Granular Access Control
Cloud identity management solutions are vital for maintaining compliance in today’s complex cloud environments. By enforcing granular access control and centralized identity management, organizations can align their cloud services with regulatory frameworks such as GDPR, HIPAA, and CCPA.
Automated Compliance Checks and Reporting
Automated compliance checks and comprehensive reporting features within cloud IAM platforms simplify the process of demonstrating adherence to regulatory requirements. Detailed audit logs and access certification workflows provide the necessary evidence for audits and help organizations maintain a state of continuous compliance.
Centralized Policy Enforcement
Centralizing identity management across multi-cloud environments ensures that access policies are consistently applied, reducing the risk of compliance gaps and streamlining the management of user identities across diverse cloud platforms.
With compliance addressed, seamless integration is the next key to effective cloud identity management.
Cloud Identity Management and Integration
Integration with Existing Systems
Seamless integration is a cornerstone of effective cloud identity management. Modern cloud IAM solutions are designed to work with existing systems, including on-premises directories like Microsoft Active Directory, HR systems, and a wide range of cloud services.
Automated Provisioning and Centralized Management
This integration enables automated user provisioning, centralized management of user identities, and consistent enforcement of access policies across all platforms.
Support for Industry Standards
Support for industry-standard protocols such as Security Assertion Markup Language (SAML), OpenID Connect, and OAuth ensures secure federation and single sign-on (SSO) capabilities, allowing users to access multiple applications with a single set of credentials.
Enhanced Monitoring and Incident Response
Integration with security information and event management (SIEM) systems enhances monitoring and incident response, providing security teams with real-time visibility into identity-related events.
Multi-Cloud Support
Additionally, cloud IAM solutions that integrate with leading cloud providers — including AWS, Microsoft Azure, and Google Cloud — empower organizations to manage user identities and access across multi-cloud environments, supporting diverse business needs and multi-cloud strategies.
A seamless user experience is also essential for adoption and productivity, as we’ll discuss next.
Cloud Identity Management and User Experience
Secure and Seamless Access
A robust cloud identity management system should deliver both security and a seamless user experience. Features like single sign on (SSO) portals and multi-factor authentication (MFA) provide secure access to cloud resources while minimizing login fatigue and streamlining workflows.
Self-Service Capabilities
Self-service capabilities, such as password resets and access request portals, empower users to manage their own digital identities and reduce the burden on IT support.
Conditional Access and Least Privilege
Conditional access policies, which adapt to user behavior and context, ensure that access is granted according to the principle of least privilege without unnecessarily restricting legitimate activity.
Visibility and Accountability
By giving users visibility into their access permissions and the ability to request changes, organizations foster a culture of security awareness and accountability.
Productivity and Security Balance
Ultimately, cloud IAM solutions that prioritize user experience help maintain productivity while upholding strong security and compliance standards.
As organizations grow, scalability becomes a critical requirement for cloud identity management.
Cloud Identity Management and Scalability
Supporting Organizational Growth
As organizations expand and adopt more cloud services, their cloud identity management solutions must scale to meet growing demands for secure and efficient access management.
Automation and Performance
Scalable cloud IAM platforms can accommodate increasing numbers of users, applications, and cloud environments without sacrificing performance or security. Automation of user provisioning, access reviews, and compliance reporting reduces administrative overhead and ensures that identity management processes keep pace with organizational growth.
Multi-Cloud and AI/ML Capabilities
Support for multi-cloud environments is essential, enabling consistent management of user identities and access across diverse cloud platforms. Advanced cloud IAM solutions leverage artificial intelligence (AI) and machine learning (ML) to provide predictive analytics and automated threat responses, helping security teams stay ahead of emerging risks.
Future-Proofing Identity Management
By investing in scalable cloud identity management solutions, organizations can confidently support business growth, regulatory changes, and the adoption of more cloud services.
FAQ
What is the best cloud identity management solution in 2026?
There is no single best solution. The right cloud identity manager depends on your cloud provider footprint, compliance requirements, and identity governance needs.
Why is multi cloud identity management important?
Because enterprises operate across multiple cloud providers, unified governance and consistent access control are essential.
What features should enterprises prioritize?
Automated user provisioning, continuous monitoring, multi factor authentication, role based access control, and unified identity governance.
How does cloud IAM support Zero Trust?
Cloud IAM enforces strict identity verification and continuously evaluates access decisions before granting access.

