👋 Welcome to Unlocked
The second quarter of 2026 has arrived with a staggering reality check from the FBI: $20.8 billion in reported losses. If last year was defined by the chaos of integrating LLMs into the workplace, 2026 is the year of AI-Native warfare. We have entered an era where attackers no longer bypass security — they simply inherit it. We’ve transitioned from "Brute Force" to "Brute Persuasion." At machine speed, adversaries are now using the very tools we built to simplify our lives — OAuth, SSO, and Device Flows — to turn our legitimate credentials against us.
Here is the breakdown of the "Passwordless" Phishing Paradox and the surging AI fraud landscape defining 2026.
📉 The $20 Billion Warning Shot
The recently released 2025 FBI IC3 Annual Report, released this week, has confirmed our worst fears: cybercrime losses have hit a record $20.8 billion.
Why the massive jump?
The formal debut of "AI-assisted fraud" in national statistics has changed the game. Generative AI has lowered the barrier to entry, allowing low-level actors to launch near-perfect phishing lures.
Impersonation has doubled: Complaints involving scammers posing as government officials or CEOs doubled in the last year.
The "Human Element": Investment fraud and Business Email Compromise (BEC) accounted for the lion's share of losses, proving that attackers aren't just hacking code — they are hacking people.
🔑 The "Passwordless" Phishing Paradox
As organizations have moved toward "Passwordless" environments to increase security, attackers haven't gone away — they’ve simply evolved to exploit the very protocols meant to protect us.
The Rise of OAuth Device Code Hijacking: Unlike previous tools that required a human "hands-on-keyboard" approach to crack a password, these attacks leverage OAuth Device Code flows. Attackers are now leveraging legitimate Microsoft Entra ID (formerly Azure AD) flows to bypass traditional MFA.
How it works at "Machine Speed":
Triggering Legitimate Prompts: By using the
/deviceloginendpoint, AI agents generate a real code and send it to a user via a high-urgency message.Abusing "Keyboard-less" Logic: The flow was designed for Smart TVs; attackers use it to trick humans into authorizing an attacker-controlled "device" on a legitimate Microsoft page.
Persistent Access: Once the user enters the code, the attacker receives a Primary Refresh Token (PRT), bypassing the need for a password or a second MFA prompt entirely.
🤖 The Rise of "Agentic" Identity Risks
In 2026, we aren't just managing human users; we are managing AI Agents. These are autonomous systems granted API keys and OAuth tokens to perform tasks (like booking travel or summarizing emails) across multiple apps.
The "Shadow Agent" Problem: Recent breaches have highlighted a new trend where attackers don't target the employee — they target the AI Agent’s identity.
Indirect Prompt Injection: A malicious email is "read" by an AI agent, which then interprets hidden instructions to exfiltrate data or grant a new OAuth token to the attacker.
Orphaned Agents: Many organizations have "Shadow AI" agents running with excessive permissions. If an agent isn't tied to a specific human owner and monitored for anomalous behavior, it becomes a permanent backdoor.
🧵 The "Harvest Now, Decrypt Later" Reality
While "Quantum Computing" still feels like a future problem to some, Quantum-Ready Security has become a 2026 mandate. Adversaries are currently practicing "Harvest Now, Decrypt Later" — stealing encrypted sensitive data (intellectual property, state secrets) today, with the plan to decrypt it once cryptographically-relevant quantum computers arrive.
If your data needs to remain secret for 10+ years, it is already at risk. This is why 2026 has seen a massive push toward Crypto-Agility: the ability to swap out encryption algorithms instantly as new standards emerge.
🎭 "Flawless" Phishing & The Identity Trap
Remember when we told employees to look for bad grammar and suspicious sender addresses? In 2026, those cues are officially gone. Generative AI now produces Synthetic Personas that mirror the exact tone, history, and communication style of your IT help desk or a trusted vendor.
We’re seeing the rise of "Multi-Touch" OAuth scams: An employee receives a 10-second deepfake voice note on Teams from their "manager" referencing a real, ongoing project, followed immediately by an AI-written request to "re-verify" their device using a code. Because the request points to a legitimate microsoft.com domain and the context feels authentic, the human brain flags it as safe.
By the time your security team notices a new device registration in a different hemisphere, the FBI’s $20.8 billion loss statistic has already grown by one more victim. In the world of machine-speed fraud, if your defense relies on a human catching a "glitch" in the matrix, you’ve already lost.
🔌 The API & Machine Identity Explosion
The "perimeter" has moved from the firewall to the API. In 2026, Machine Identities (API keys, service accounts, and automated credentials) now outnumber human identities by a staggering ratio (often 20:1).
Most organizations have a "shadow" ecosystem of connected SaaS tools and automated workflows that are poorly governed. Attackers are moving laterally not through desktops, but through these invisible connections. A single compromised API key can offer more "internal" access than a dozen employee passwords.
🛡️ How Security Leaders Should Respond
1. Mandate Phishing-Resistant MFA
Training is no longer a silver bullet. Move beyond SMS and Push notifications. Adopt FIDO2-backed Passkeys or physical security keys. These cryptographically bind the login to the specific domain, making it impossible for a user to "accidentally" give away a token.
2. Govern Your AI Agents
Apply the same Zero Trust rigor to your AI agents that you do to your employees. Every agent should have a registered human "owner," a specific scope of permissions, and session-based tokens that expire quickly rather than persistent API keys.
3. Fight AI with AI
You cannot defend against machine-speed token theft with manual triaging. 2026 requires AI-driven defensive tools that can detect "Impossible Travel" or anomalous token usage in milliseconds and automatically kill the session.
💡 Unlocked Tip of the Week
Check your "Protocol" footprint.
Ask your IT team: “In the last 30 days, how many successful logins used the Device Code Flow, and were they authorized by a human or a machine?”
If you can’t answer that, you have a blind spot that the FBI's $20.8B report warns is a primary breach vector.
📊 Poll of the Week
With AI fraud doubling, which threat keeps you up at night?
🔥 Final Takeaway
2026 isn't about "new" problems; it's about the industrialization of deception.
The goal for security leaders this year is to move from reactive MFA to immutable identity.
We are no longer just protecting passwords; we are protecting the very tokens that represent our digital lives.
Stay ready. Stay resilient.
Until next time,
Meet Kevin Patel - Cybersecurity Researcher & Digital Risk Analyst
Kevin Patel brings a strategic eye to the evolving threat landscape, specializing in how emerging technologies change the "math" of digital risk. With a background in threat intelligence and identity security, Kevin focuses on bridging the gap between technical vulnerabilities — like OAuth exploits — and the human psychology that attackers weaponize. He believes that in 2026, the only way to beat machine-speed fraud is through cryptographically-backed trust and relentless anomaly detection.
Our Sponsor
Stop Chasing Docs. Automate Them.
Docs piling up faster than you can write them? Same.
Every team knows the feeling — product ships, docs don't. Changelogs get forgotten. Style violations quietly accumulate. Broken links go unnoticed for months.
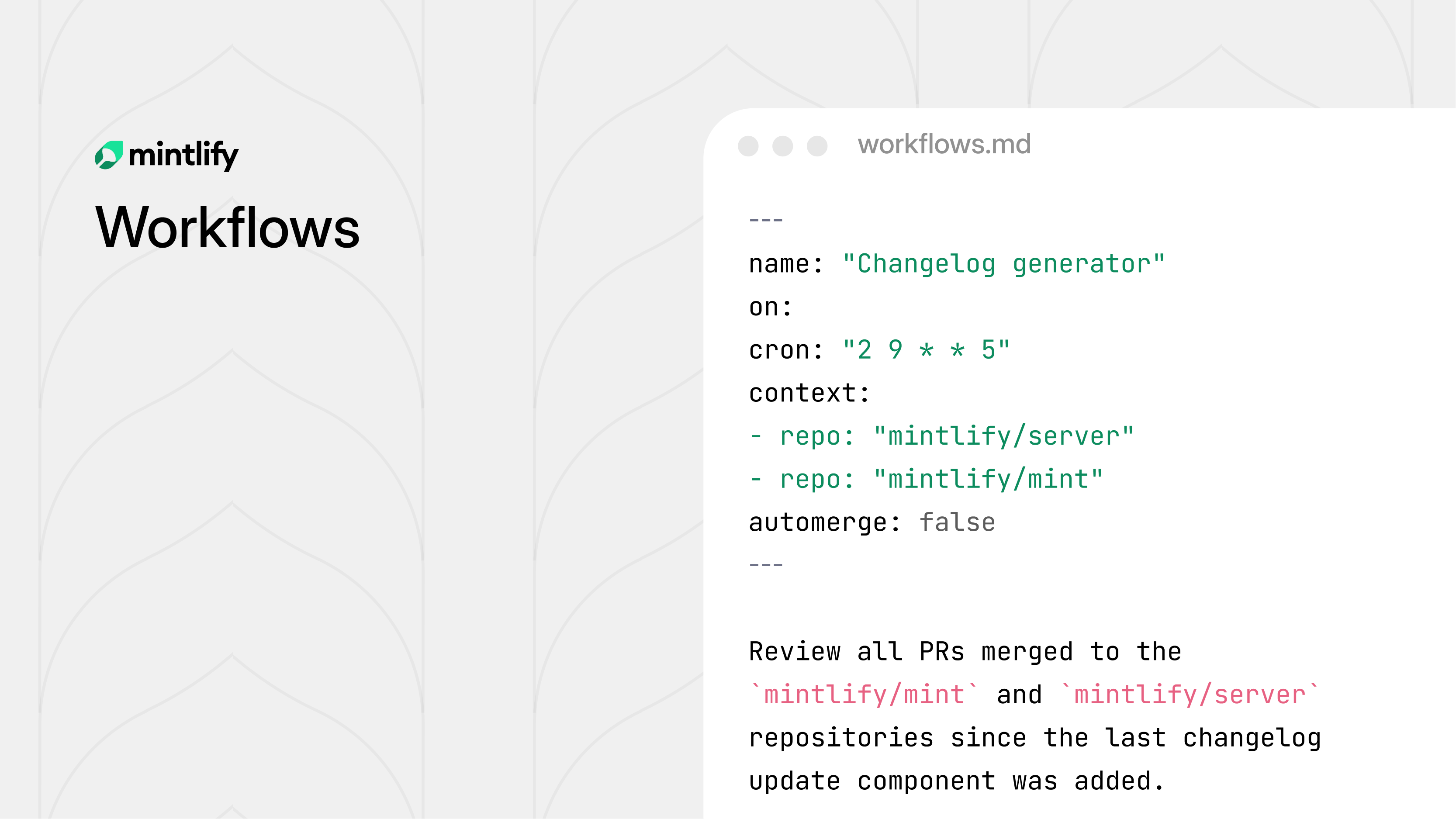
Mintlify's new Workflows feature fixes this. Define automation rules, and the agent handles the recurring maintenance work for you — on your schedule, by your rules.
Draft docs when a PR merges. Generate changelogs every Friday. Run a style audit on every push. Flag translation lag before it becomes a problem. Each workflow is version controlled, fully configurable, and fits into your existing review process.
You decide when it runs, what it checks, and whether changes get committed directly or opened as a pull request for review.
The result: documentation that actually keeps up with your product, without someone manually chasing it down.