REST Assured authentication is a critical aspect of secure API testing, enabling testers and developers to automate and validate secure API interactions. This guide is designed for API testers and developers who want to automate and validate secure API interactions using REST Assured. Understanding REST Assured authentication is essential for ensuring that only authorized users and systems can access sensitive resources, and for maintaining the integrity and security of your APIs.
We cover Basic, Digest, OAuth, API Key, and Form authentication, as well as best practices for secure API testing. REST Assured supports several authentication schemes for testing secured APIs, making it a powerful tool for automating authentication in API testing workflows.
Introduction to API Authentication
API authentication is the process of verifying the identity of users or applications that attempt to interact with an API. This step is essential for protecting sensitive data and ensuring that only authorized parties can access or modify resources. There are several authentication methods available, such as basic authentication, digest authentication, OAuth, and API keys. Each of these authentication schemes offers different levels of security and complexity, making it important to choose the right approach based on your API’s requirements. REST Assured simplifies the process of testing various authentication methods by providing built-in support for multiple authentication schemes, allowing you to automate and validate secure API interactions with ease.

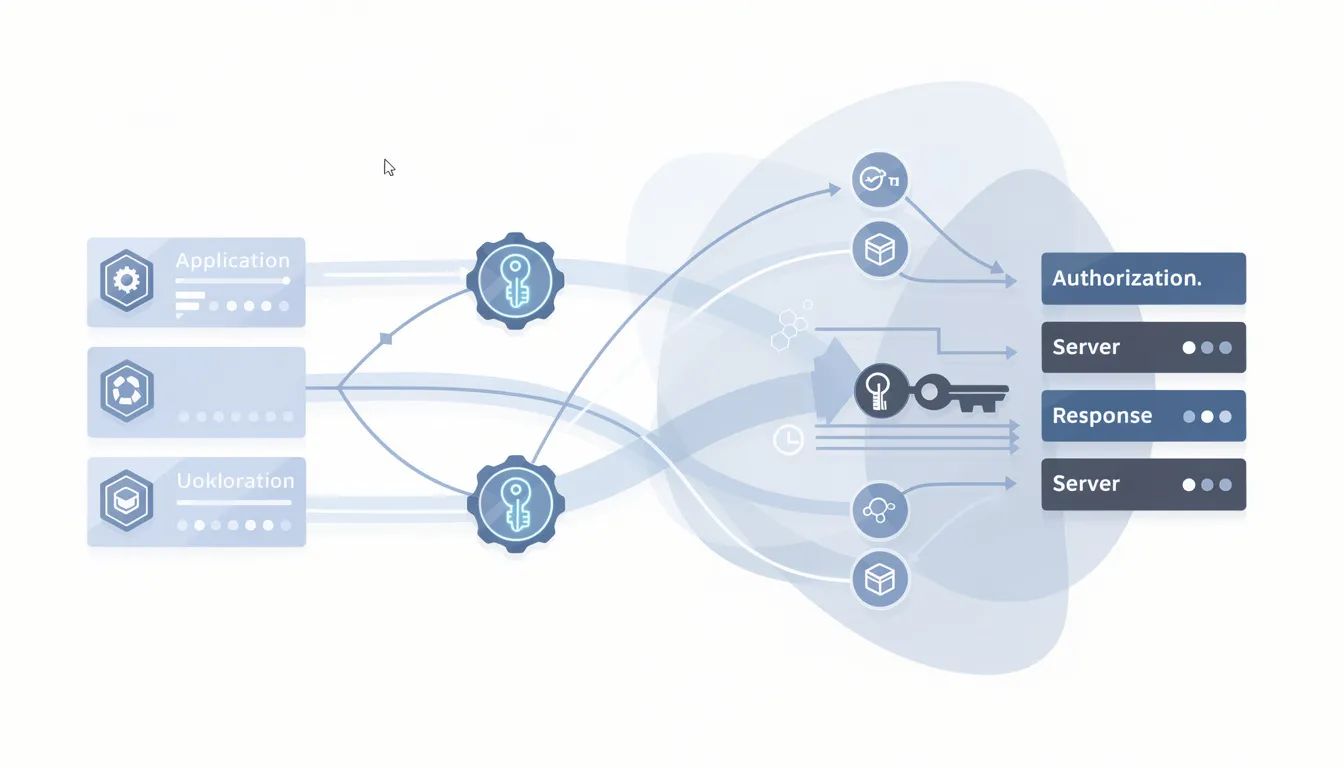
Authentication refers to confirming the user's identity, while authorization determines a user's access to resources based on their identity and permissions. Authentication verifies a user's identity, while authorization determines what access or permissions that user has within a system.
Before diving into REST Assured specifics, it's important to distinguish between authentication and authorization:
Authentication: Confirms the user's identity.
Authorization: Determines what access or permissions that user has within a system, based on their identity.
Authentication is the first step, and authorization follows authentication, controlling access to resources. It is important to securely pass the client's authentication credentials during API requests to maintain security and integrity.
Now that we've established these foundational concepts, let's explore how REST Assured supports multiple authentication methods for API testing.
REST Assured Authentication
REST Assured supports multiple authentication methods including Basic, Pre-emptive, Digest, Form, OAuth 2.0, and Bearer Tokens. This makes REST Assured a versatile tool for automating authentication in API testing workflows.
Credential Handling
REST Assured authentication plays a central role in validating secure access to APIs during testing. REST Assured handles authentication by managing authentication details such as tokens, client IDs, and secrets required for various authentication methods. Authentication ensures that only authorized users or systems can access sensitive resources, which is critical as APIs power modern online services.
Double-checking API documentation, endpoint URLs, and request headers is crucial for successful authentication.
Next, let's examine the main authentication methods supported by REST Assured.
Authentication Methods Overview
Common authentication methods supported by REST Assured include:
Basic Authentication
Digest Authentication
OAuth Authentication (OAuth 1.0 and OAuth 2.0)
API Key Authentication
Bearer Token Authentication
Form Authentication
Pre-emptive Authentication
Each method offers different levels of security and is suited to different use cases. The following sections will explore each method in detail.
Basic Authentication
Basic Authentication sends credentials (username and password) encoded in Base64 with each request. To successfully authenticate using Basic Authentication, users must provide valid credentials (username and password) to gain authorized access to secured APIs. Basic Authentication sends credentials (username and password) within the header of an HTTP request to validate the user’s identity.
REST Assured automatically handles technical details like Base64 encoding for Basic Auth and adding Bearer prefixes for OAuth tokens.
Key Points:
Credentials are sent with every request.
Easy to implement but introduces security vulnerabilities if used without HTTPS.
Comparison Table: Basic vs Digest vs OAuth
Method | Security Level | Credentials Sent | Use Case |
|---|---|---|---|
Basic | Low | Plain (Base64) | Simple, internal APIs |
Digest | Medium | Hashed | Enhanced security, legacy APIs |
OAuth (2.0) | High | Token-based | Public APIs, delegated access |
Next, let's look at how Digest Authentication improves upon Basic Authentication for enhanced security.
Digest Authentication
After understanding Basic Authentication, it's important to see how Digest Authentication enhances security by avoiding the transmission of credentials in plain text. Digest Authentication is a form of challenged authentication, where the server issues a challenge and the client must respond appropriately to authenticate. Digest Authentication enhances the security of Basic Authentication by using a server-generated nonce and requiring a hashed response.
This authentication mechanism is useful when credentials must be protected but token-based authentication is unavailable.
Next, let's explore how Form Authentication simulates user login for session-based APIs.
Form Authentication
Building on Digest Authentication, Form Authentication simulates logging in through an HTML form by submitting j_username and j_password. This method is useful for APIs that rely on user sessions created through an HTML form. REST Assured supports form authentication when testing legacy systems or internal applications.
Steps for Form Authentication:
Identify the login form fields (e.g., j_username, j_password).
Submit a POST request with these fields as form parameters.
Ensure the correct context path is included in the form's action attribute.
Next, let's discuss API Key Authentication and how it provides secure server-to-server communication.
API Key Authentication
After understanding Form Authentication, API Key Authentication involves passing a secret key in the query parameter or header for server-to-server security. API keys can also be included as request parameters in the URL or body of the request, depending on the API's requirements.
Key Points:
API keys provide limited access and should be protected as sensitive credentials.
The method header("Authorization", "Bearer " + token) is used for public APIs that identify the calling application via a static key.
To stay informed on the latest breaches, cyber threats, and security tips, consider subscribing to Unlocked, Everykey's weekly cybersecurity newsletter.
After understanding API key authentication, it's important to consider how OAuth provides even more secure access control.
OAuth Authentication
OAuth authentication is especially important for secure API access, as it allows clients to obtain limited access to resources without exposing user credentials.
OAuth can also serve as the foundation for an identity protocol, such as OpenID Connect, which enables user authentication and identity management on top of OAuth.
In OAuth workflows, the authorization server is responsible for authenticating users and issuing access tokens, while the resource server hosts protected resources and responds to requests from client applications using those access tokens.
REST Assured supports both OAuth 1.0 and OAuth 2.0 authentication schemes for testing secured APIs.
Next, let's clarify the OAuth 2.0 Authorization Code Flow and how REST Assured interacts with it.
OAuth 2.0 is a widely used authentication mechanism that allows limited access to user accounts without exposing sensitive credentials. The client application (often a third-party app) requests access to user resources on behalf of the resource owner. Client IDs are used to uniquely identify client applications during the OAuth authentication process. The resource owner is the user who controls access to protected resources.
Important Note: REST Assured allows configuring OAuth 2.0 access tokens to request secured resources, but does not help in obtaining the access token itself. The auth().oauth2() method in REST Assured uses a temporary access token issued by an authorization server, which is standard for public-facing APIs.
OAuth is technically an authorization framework and does not define any mechanism for authenticating a user.
Next, let's review how Bearer Tokens are used in token-based authentication.
Bearer Token Authentication
Bearer tokens are commonly used with OAuth 2.0 for token-based authentication.
Key Points:
Token-based authentication uses tokens to authenticate users, providing an additional layer of security by requiring possession of a physical or digital token.
Token-based authentication authenticates users through a service that issues tokens instead of directly handling their credentials.
Now that we've covered the main authentication methods, let's discuss best practices for API testing and automation.
API Testing: Validating Authentication and Access Controls
Authentication is a core part of API testing because access controls must be validated alongside functionality. Debugging authentication issues can be challenging in API testing.
Common Authentication Issues
Incorrect tokens
Expired credentials
Misconfigured security settings
When debugging authentication issues, it is essential to capture and analyze the authentication flow. Enabling basic logging can help in analyzing authentication issues.
Next, let's look at how to automate authentication in your API testing workflows.
API Automation: Integrating Authentication into Automated Tests
Integrating authentication into automated tests ensures that your APIs' security is not compromised during the testing process.
Automation in CI/CD Pipelines
REST Assured can be integrated into CI/CD pipelines to ensure that security mechanisms remain functional after code changes.
Negative Testing
Testing scenarios where incorrect or missing credentials lead to authentication failures is crucial for ensuring proper API security.
Next, let's review best practices for building reliable and maintainable API test suites.
API Automation Best Practices
When automating API testing, following best practices is crucial for building reliable and maintainable test suites. Using a robust automation tool like REST Assured streamlines the process of scripting and executing API interactions.
Best Practices:
Design modular test cases that focus on specific endpoints or features.
Implement proper authentication and authorization in your automated tests.
Simulate real-world usage and protect your API from unauthorized access.
By adhering to these best practices, you can maximize the effectiveness of your API testing and maintain the integrity of your application.
Next, let's discuss security considerations for API authentication.
Security Considerations for API Authentication
Security should be at the forefront of any API testing strategy. Employing secure authentication and authorization mechanisms, such as OAuth and API keys, helps safeguard your API from unauthorized access.
Encryption and Data Protection
Use encryption protocols like SSL/TLS to protect data as it travels between clients and servers.
Validate and sanitize all API inputs to prevent common vulnerabilities such as SQL injection and cross-site scripting (XSS).
REST Assured supports secure API interactions by enabling you to test with various authentication schemes and ensuring that your API keys and credentials are handled safely during automated tests.
Next, let's address common authentication issues and troubleshooting tips.
Troubleshooting Common Authentication Issues
Testing APIs often involves troubleshooting common authentication issues, such as invalid or expired credentials, misconfigured authentication settings, or incorrect implementation of authentication schemes. These problems can disrupt the testing process and lead to inaccurate results.
Debugging Tips
Leverage REST Assured’s built-in support for multiple authentication schemes.
Utilize logging and tracing features to pinpoint the root cause of authentication failures.
By combining robust automation tools with effective debugging techniques, you can streamline your API interactions and ensure that your authentication processes are both reliable and secure.
Next, let's explore modern access models and how they complement API authentication.
Modern Access and API Authentication
Modern API authentication emphasizes access over friction. Identity-aware access models reduce reliance on static credentials and improve user experience.
Solutions like EveryKey complement API authentication strategies by continuously confirming identity through presence and proximity. This reduces reliance on exposed credentials while maintaining seamless access across systems.
Now, let's summarize the key takeaways from this guide.
Conclusion
In summary, authentication and authorization are fundamental to securing APIs, and REST Assured offers a comprehensive framework for automating these critical processes. By understanding and implementing different authentication methods, you can ensure that your API interactions are both secure and efficient. Following best practices, addressing security considerations, and proactively resolving authentication issues will help you build reliable automated tests and maintain the integrity of your APIs. With REST Assured, testing and validating various authentication methods becomes straightforward, empowering you to deliver robust and secure API solutions.
Frequently Asked Questions
What authentication methods does REST Assured support?
REST Assured supports the following authentication methods:
Basic Authentication
Pre-emptive Authentication
Digest Authentication
Form Authentication
OAuth 1.0
OAuth 2.0
API Key Authentication
Bearer Token Authentication
What is the difference between authentication and authorization?
Authentication verifies a user's identity.
Authorization determines what access or permissions that user has within a system.
Why do APIs return 401 or 403 errors?
401 indicates missing or invalid credentials.
403 indicates valid credentials without sufficient permissions.
Is OAuth an authentication protocol?
OAuth is technically an authorization framework and does not define any mechanism for authenticating a user.
Why is authentication testing important in CI/CD?
Integrating authentication into automated tests ensures APIs remain protected after changes and prevents accidental exposure.

