Authentication sits at the center of every secure system. Whether protecting user accounts, enabling sensitive transactions, or facilitating online authentication across multiple applications, strong authentication design determines how effectively systems can resist modern cyber threats.
This cheat sheet is designed for IT professionals, security architects, and developers seeking practical guidance on modern authentication best practices. It covers authentication protocols, error handling, multi-factor authentication, session management, and defensive controls.
Authentication is the process of verifying that an individual, entity, or website is who it claims to be. Authentication functionality should provide generic error responses to prevent information leaks that could aid attackers. Always encrypt communication between the user’s browser and the web application, and transmit passwords only over secure channels such as TLS to prevent interception. Protect the user's authenticated session by ensuring all pages requiring login, including the login page and subsequent authenticated pages, are accessed exclusively over secure transport protocols. Transmitting session IDs or session data unencrypted can lead to session compromise. Session hijacking involves stealing active session tokens (cookies) to bypass the need for username, password, or MFA. Attackers may also target the user's browser to hijack sessions, especially if they gain temporary physical access to the device or steal session IDs. Therefore, re-authentication and secure session management are critical for sensitive features. Authentication tokens and stored credentials should be encrypted using strong hashing algorithms like Argon2 or bcrypt, combined with unique salts for each user, to prevent rainbow table attacks.
Introduction to Authentication
Authentication is the foundational process that ensures only legitimate users gain access to web applications and their sensitive resources. At its core, authentication verifies the identity of an individual, entity, or website by validating one or more authenticators — such as passwords, biometrics, or security tokens. In most web applications, this process begins at the login page, where users submit a user ID and a secret, like a password, to prove their identity.

To maintain robust authentication security, it is essential to implement secure password recovery mechanisms, maintain comprehensive user logs, and design authentication and error messages that do not reveal sensitive information. Error messages should be generic and consistent to prevent attackers from deducing valid user IDs or passwords. Authentication functionality should always provide generic responses to ensure attackers cannot infer whether a username or password is correct, thereby preventing information leaks during authentication.
Protecting user credentials requires the use of strong cryptographic authentication keys and secure transport protocols. TLS client authentication, especially when combined with securely stored cryptographic authentication keys, provides an additional layer of defense by ensuring that only authorized devices can access the system. All communication between the user’s browser and the web application — including the login page and subsequent authenticated pages — must be encrypted using TLS or equivalent protocols. This prevents attackers from intercepting or modifying authentication data, safeguarding the integrity of user sessions and the confidentiality of sensitive information.
Authentication and Error Messages
Authentication and error messages are often overlooked, yet they play a major role in preventing account enumeration and brute-force attacks. An application should respond with a generic error message regardless of whether the user ID or password was incorrect. This prevents password enumeration and avoids leaking information through authentication attempt response behavior.
Authentication and error messages should avoid confirming invalid user ID or invalid password scenarios. A generic error page with a consistent HTTP response code helps protect legitimate users and limits attacker feedback. Authentication and error messages must also avoid reflecting user input, which could otherwise expose sensitive data.
Logging and monitoring of authentication functions should be enabled to detect attacks or failures in real-time. Monitoring enable logging allows security teams to correlate failed login attempts, password failures, and suspicious user interaction patterns.
Identity Provider
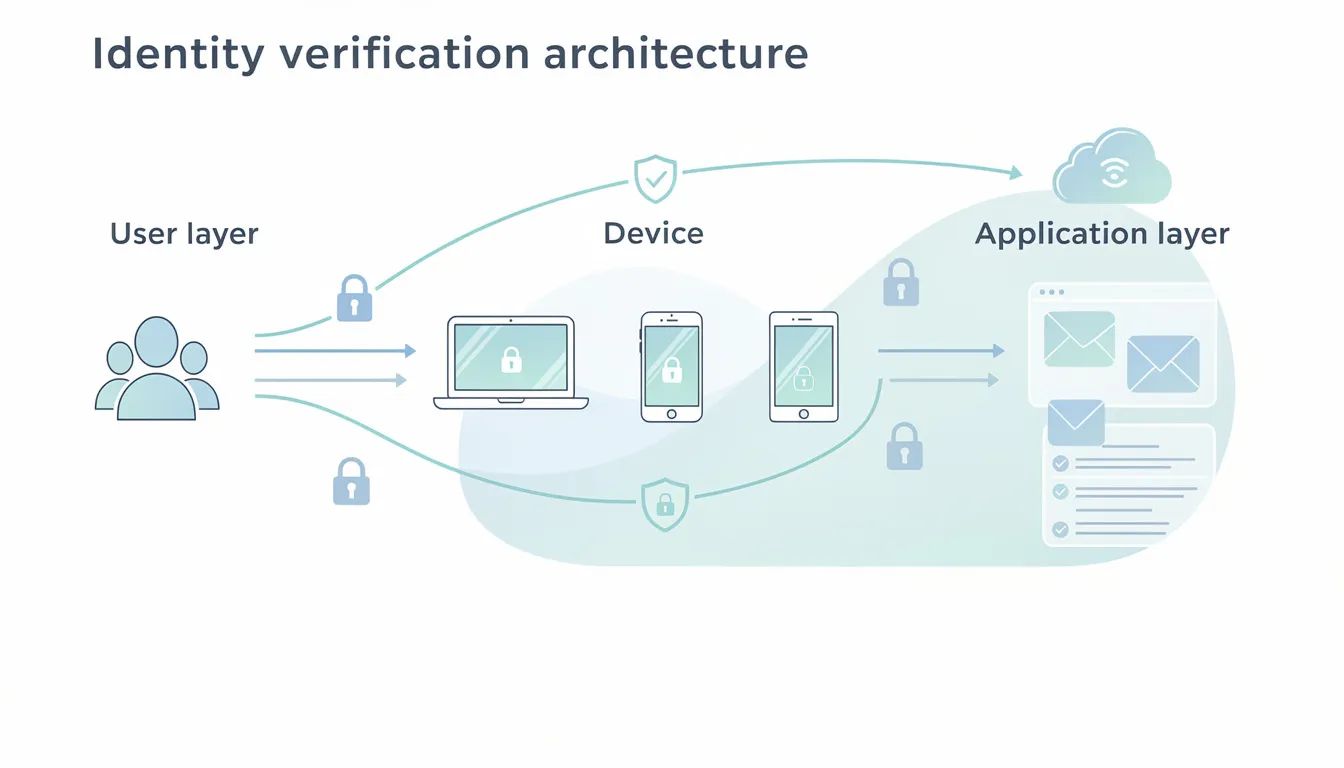
An identity provider is responsible for verifying user identity and issuing authentication responses across multiple applications. Identity providers reduce duplication by centralizing authentication and identity verification through a common authentication framework.
Enterprise environments often rely on Active Directory Federation Services, OpenID identity providers, or SAML-based identity provider integrations. SAML is often the choice for enterprise applications because there are few OpenID identity providers which are considered enterprise-class. SAML is based on browser redirects which send XML data.
OAuth 2.0 and OpenID Connect are standards for delegated, token-based authorization and authentication. OAuth is an authorization framework for delegated access to APIs, while OpenID Connect is an identity layer on top of OAuth.
The Fast Identity Online Alliance has created two protocols to facilitate online authentication: the Universal Authentication Framework protocol and the Universal Second Factor protocol. UAF focuses on passwordless authentication, while U2F allows the addition of a second factor to existing password-based authentication.
Multi Factor Authentication
Multi-Factor Authentication is the best defense against the majority of password-related attacks, including brute-force attacks. MFA enhances security by requiring multiple forms of verification before granting access to user accounts.
Authentication factors are defined as follows:
Knowledge (Something you know): Passwords, PINs, security questions.
Possession (Something you have): Hardware tokens (YubiKey), smartphone apps, SMS codes, smart cards.
Inherence (Something you are): Biometrics (fingerprint, facial recognition, iris scan).
Location (Somewhere you are): Geo-fencing, GPS tracking to restrict login to specific areas.
Behavior (Something you do): Typing speed, mouse movement patterns.
Location and behavior factors further strengthen risk-based authentication models.
MFA reduces reliance on weak, reused, or compromised passwords, which are a leading cause of security breaches. Many industries and countries have regulations that require the use of MFA, particularly in finance and healthcare sectors. MFA is recommended for all applications to enhance security against unauthorized access.
Phishing-resistant MFA prefers hardware security keys or passkeys over SMS-based authentication. Passkeys are built on FIDO2 and WebAuthn standards, are phishing-resistant, and tied to a physical device. Passwordless MFA combines two passwordless factors, such as a passkey and a biometric scan.
Error Messages
Error messages must remain consistent across authentication flows. Authentication responses should never disclose whether a user account exists. This includes login failed scenarios, invalid password messages, and authentication attempt response logic.
Authentication and error messages should be logged internally through user logs, but externally surfaced error messages should remain generic. This reduces exposure to brute-force attacks and credential stuffing.
Authentication Protocols
Several authentication protocols coexist across modern systems. Password-based authentication remains common but increasingly vulnerable. FIDO protocols, such as FIDO UAF, leverage existing security technologies present on devices — like biometrics, Trusted Execution Environments (TEEs), and secure elements — to enable passwordless or multi-factor authentication. Hardware-based authentication methods often store cryptographic authentication keys within secure devices or elements, such as hardware tokens, SEs, or TEEs, to facilitate secure login processes.
Widely used authentication protocols include:
OAuth: An authorization framework for delegated access to APIs.
OpenID Connect: An identity layer on top of OAuth for authentication.
SAML: A protocol based on browser redirects and XML data, commonly used in enterprise environments.
TLS client authentication: Uses stored cryptographic authentication keys to authenticate a client device rather than a user’s password.
FIDO protocols: Leverage device security technologies (biometric sensors, Trusted Execution Environments, Secure Elements) for secure, passwordless or two-factor authentication.
TLS client authentication combined with strong identity verification helps secure machine-to-machine access and sensitive internal systems. Stored authentication key material must be protected using strong cryptographic techniques.
Sessions are maintained on the server by a session identifier, which is exchanged between the client and server during requests. Session identifiers should be unique per user and computationally very difficult to predict.
Microsoft is permanently retiring Basic Authentication in early 2026 in favor of OAuth 2.0, signaling a broader industry shift away from legacy authentication models.
Failed Login Attempts
Failed login attempts should be carefully managed.
The following steps help mitigate brute-force and credential stuffing attacks:
Rate limiting and throttling: Limit how many authentication attempts can occur within a defined window.
Account lockout: Prevent further login attempts for a period after repeated failures.
CAPTCHA controls: Help prevent automated attacks, but should be paired with other controls to avoid user friction.
Strong password policy: Make it difficult to guess the password through manual or automated means.
Passwords should be stored using the right cryptographic technique to ensure security.
Based Authentication
Password-based authentication remains widely deployed, but it should be treated as a baseline rather than a primary defense. Existing password-based authentication should always be paired with MFA, strong password strength rules, and secure password recovery mechanisms.
Passwords must never be transmitted in plaintext. The login page and all subsequent authenticated pages must be accessed over TLS or other strong transport. Failure to utilize TLS after login enables attackers to compromise the user’s authenticated session.
Authentication Solution
A modern authentication solution integrates identity verification, authentication protocols, session management, and risk-based authentication into a single flow.
Continuous Authentication
Continuous Authentication involves monitoring user behavior and location after login to detect anomalies. This approach helps identify session hijacking and other suspicious activities in real time, providing ongoing assurance of user identity throughout the session.
Reauthentication
Reauthentication is critical when an account has experienced high-risk activity such as password resets or suspicious behavior patterns. Strong transaction authentication should be required before users execute sensitive transactions, such as shipping a purchase to a new address, to prevent unauthorized actions. Before executing sensitive transactions, require the user's current credentials, such as the user's password, to enhance security and prevent unauthorized access. Re-authentication should also be required before changing the user’s password or email address. Requiring the user’s current credentials during sensitive actions helps prevent unauthorized access and security breaches, such as CSRF or session hijacking.
Zero Trust Architecture
Implement Zero Trust Architecture by never trusting and always verifying every access request, regardless of origin (internal or external). This model assumes that threats can exist both inside and outside the network, so every request must be authenticated and authorized.
Attackers gaining access to the user's browser pose a significant risk, so session protection and re-authentication are essential. Some organizations are moving toward proximity-based authentication models, where user presence continuously confirms identity. Platforms like EveryKey approach authentication by focusing on access that adapts to user presence and device context, reducing reliance on repeated password prompts while maintaining strong authentication security.
Password Managers
Password managers help users store passwords securely and reduce password reuse. Password managers encrypt stored authentication keys and help enforce proper password strength across multiple applications.
Password managers reduce the burden on the average user while lowering the risk of compromised passwords. They should be considered a complementary control alongside MFA, not a replacement.
Password Management
Effective password management is fundamental to protecting user accounts from unauthorized access and credential-based attacks. One of the most critical components of password management is implementing a secure password recovery mechanism. Without proper safeguards, password recovery processes can become a weak link, allowing attackers to bypass authentication and compromise user accounts.
A secure password recovery mechanism should never reveal sensitive information about user accounts, such as whether a specific email or username exists in the system. Instead, the process should use generic responses and require multiple steps to verify the user’s identity. For example, sending a password reset link to a registered email address or mobile device ensures that only the legitimate account owner can initiate a reset.
Authentication Responses
Authentication responses should be uniform, predictable, and non-descriptive. Session management is a process by which a server maintains the state of an entity interacting with it. Sessions are maintained using session identifiers that must be unique and computationally difficult to predict.
To mitigate CSRF and session hijacking, systems should require current credentials before updating sensitive account information.
Brute Force Attacks
Brute-force attacks involve repeatedly guessing passwords to gain unauthorized access. MFA significantly reduces the success of brute-force attacks. Rate limiting, account lockout, CAPTCHA controls, and strong password policies form an effective defense-in-depth strategy.
Credential stuffing uses stolen credentials from unrelated breaches. MFA and phishing-resistant authentication significantly reduce this risk.
Identity Verification
Identity verification confirms that a legitimate user is who they claim to be. Identity verification is strong authentication to confirm user or device legitimacy. User IDs should be unique and ideally randomly generated to prevent predictable or sequential IDs.
Usernames should be case insensitive and unique within a system. Continuous Authentication enhances identity verification by validating identity throughout a user’s authenticated session, not only at login.
In 2026, cybersecurity authentication has shifted toward phishing-resistant and passwordless models as traditional passwords and SMS codes have become increasingly vulnerable to AI-driven attacks.
Conclusion
In conclusion, authentication is a cornerstone of web application security, playing a vital role in safeguarding user accounts and sensitive data. Implementing a secure password recovery mechanism, maintaining detailed user logs, and crafting careful authentication and error messages are all essential elements of a strong authentication framework.
Relying on both a password and a second factor — such as a hardware token or TLS client authentication — significantly enhances protection against unauthorized access. The adoption of passwordless authentication, supported by protocols like the Universal Authentication Framework, further strengthens authentication security by reducing reliance on traditional passwords.
Risk-based authentication, combined with continuous monitoring and logging of authentication functions, helps detect and respond to brute force attacks and other evolving threats. Best practices such as using generic error messages, deploying plugin-based login pages, and enforcing role-based access control ensure that authentication protocols remain resilient against common attack vectors.
By integrating these measures with existing security technologies, organizations can build a comprehensive authentication solution that supports secure online authentication and protects sensitive transactions. Ultimately, a layered approach to authentication — leveraging both established and emerging technologies — enables web applications to verify user identity with confidence, maintain the integrity of user sessions, and deliver a seamless, secure experience for every user.
FAQ
What is the biggest authentication mistake organizations make?
Leaking information through error messages and relying on password-only authentication.
Is MFA enough on its own?
MFA is critical, but it works best when combined with secure session management, logging, and phishing-resistant methods.
Are passwords going away?
Passwords are declining, but most systems still support them. Passkeys and passwordless authentication are rapidly growing.
Why is continuous authentication important?
It detects session hijacking and anomalous behavior after login, closing a major security gap.

