
Multi-Factor Authentication (MFA)
History of Multi Factor Authentication
How multi factor authentication evolved from early banking controls to modern, adaptive access systems.
Head of Content at EveryKey with a background in tech and startup content management. Nick has driven digital content and branding across SaaS and cybersecurity — and outside work, he's a traveler, concert-goer, and cat dad.


Multi-Factor Authentication (MFA)
How multi factor authentication evolved from early banking controls to modern, adaptive access systems.

Why identity has become the primary security boundary — and how modern IAM failures are driving the biggest breaches of 2026.

Password Manager
What a password manager is, how password managers work, and why they remain essential for staying secure online in 2026.

Best Practices
How identity providers, MFA, and centralized identity management strengthen security while delivering seamless access across modern enterprises.

Passwordless
A Best of 2026 guide to passwordless authenticators, Microsoft Authenticator, biometrics, FIDO2 security keys, and secure passwordless login methods.

Best Practices
Best practices for creating strong passwords, using password managers, and protecting online accounts from modern cyber threats.
Documentation
A complete single sign on documentation guide covering SAML, OpenID Connect, identity providers, service providers, and secure SSO architectures for cloud and on-prem applications.

Passwordless
How multi-factor authentication methods protect accounts using codes, devices, and biometrics.
Best Practices
A modern breakdown of the CIS password policy, failed login controls, MFA adoption, and best practices for securing user accounts against evolving cyber threats.
Best Practices
How modern technical cyber security protects cloud environments, networks, endpoints, and identities against evolving cyber threats in an increasingly complex digital world.

Cybersecurity Training
How Cyber Drills Build Real-World Readiness, Resilience, and Faster Incident Response.
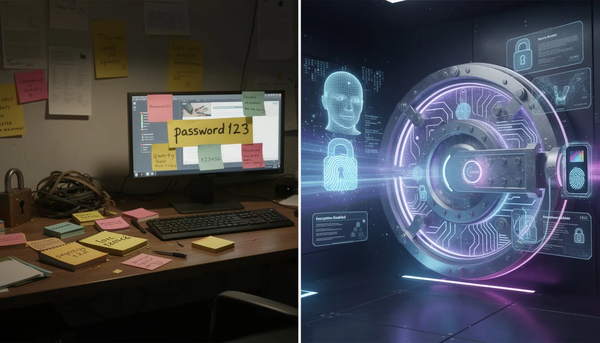
Best Practices
When pen-and-paper password habits collide with modern password managers and MFA.