
Privileged Access Management
Your Guide to Managing Privileged User Access and Security Risks
What Privileged Users Are, Why They Matter, and How to Manage Elevated Access Safely
Head of Content at EveryKey with a background in tech and startup content management. Nick has driven digital content and branding across SaaS and cybersecurity — and outside work, he's a traveler, concert-goer, and cat dad.


Privileged Access Management
What Privileged Users Are, Why They Matter, and How to Manage Elevated Access Safely

A practical guide for IT professionals on testing password strength, reducing credential risk, and improving access hygiene.
Best Practices
A practical guide to authentication protocols, identity verification, and secure access for modern networks and applications.

Identity and Access Management
How Secure Access Portals Enable Protected, Location-Independent Access for Modern Organizations

Cyberattack
How Modern Organizations Anticipate, Prioritize, and Prevent Cyber Attacks

Authentication
A practical guide to authentication methods, authorization flows, and secure API testing with REST Assured.

Cyberattack
A practical guide for IT teams on cyber incident reporting, compliance, and building trust in a connected digital world.

Authentication
FIDO2 hardware keys, passkeys, biometrics, TOTP, and SMS-based MFA compared across security, usability, and enterprise readiness for 2026.

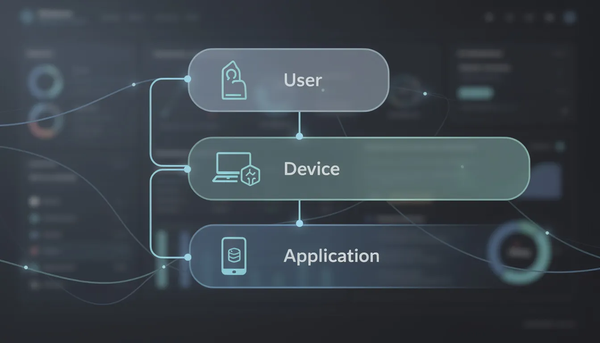
Identity and Access Management
A practical guide to how identity, access, and permissions work in modern digital systems.
Best Practices
A practical reference for modern authentication, identity verification, and secure access

Cyberattack
A practical guide to modern cyber threats, attack methods, and how organizations defend against them.

Authentication
How forms-based authentication works, security risks, and best practices For modern web applications.