Best Practices
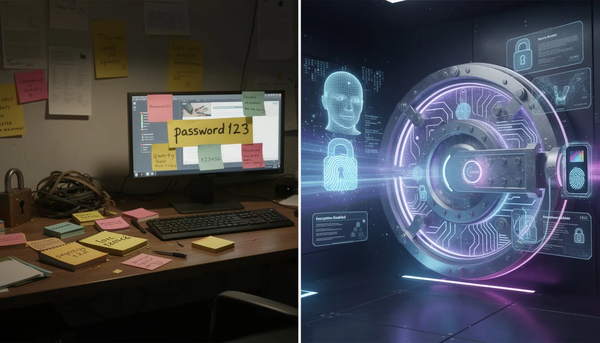
Writing Down Passwords: Is It Ever Safe in a World of Data Breaches?
When pen-and-paper password habits collide with modern password managers and MFA.
Head of Content at EveryKey with a background in tech and startup content management. Nick has driven digital content and branding across SaaS and cybersecurity — and outside work, he's a traveler, concert-goer, and cat dad.

Best Practices
When pen-and-paper password habits collide with modern password managers and MFA.
Cybersecurity Tools
How modern security platforms unify cloud security, threat detection, automation, and access control to reduce risk and scale protection across the entire environment.

Best Practices
Why password length, randomness, and modern security practices matter more than ever.
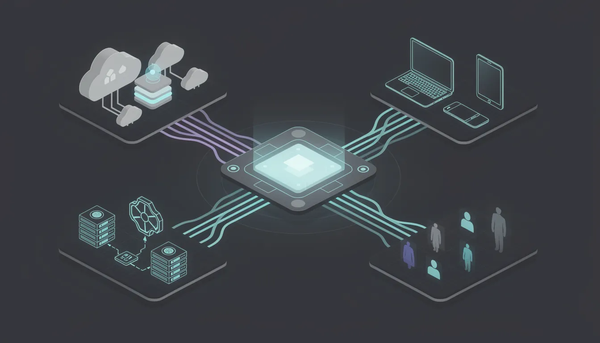
Cybersecurity Tools
We tested CrowdStrike, SentinelOne, Palo Alto, Zscaler, and 8 more cybersecurity tools across endpoint, network, and identity protection. See the 2026 rankings — updated with AI-powered threat detection.

SOC 2
A practical guide to SOC 2 cybersecurity, the Trust Services Criteria, and how organizations prove strong security controls, risk management, and data protection.

Authentication
How modern authentication replaces passwords with adaptive, multi-factor security to protect users, data, and cloud-based systems.
Cybersecurity
How administrative, technical, and physical security controls protect systems, reduce cyber risk, and strengthen organizational security posture.

MSP
Why businesses turn to MSSPs for 24/7 threat monitoring, compliance support, and scalable cybersecurity expertise.

Authentication
A Practical Guide to Secure Login Forms, Session Management, and Modern Web Authentication.

Digital Protection
A practical cybersecurity guide to SaaS security posture management, access control, and protecting sensitive data in cloud-first environments.

Identity and Access Management
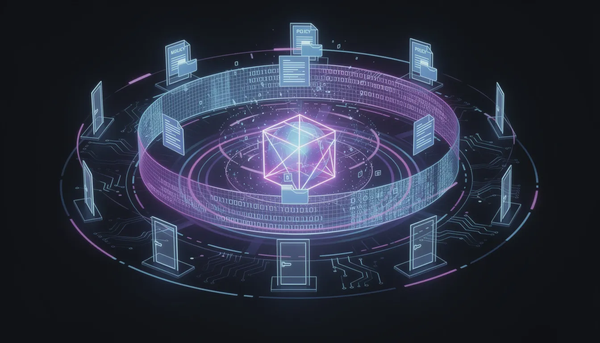
How modern access control systems protect sensitive data, prevent unauthorized access, and enforce least privilege across digital and physical environments.

Cybersecurity
Most people use the digital space oblivious to the potential dangers. However, that doesn’t change the fact that the online space is filled with them, whether we're aware of them or not. The risks that slip through unnoticed can often cause the biggest issues later on, and that’s exactly how the big