
cyberattack
Understanding Server Crime: Types, Threats, and Prevention Strategies
How Server Crime, Cyber Threats, and Law Enforcement Collaboration Are Reshaping Enterprise Cybersecurity

cyberattack
How Server Crime, Cyber Threats, and Law Enforcement Collaboration Are Reshaping Enterprise Cybersecurity

the breach report
Hello and welcome back to The Breach Report! January 2026 kicked off the new year with a relentless surge in activity, proving that there is no "post-holiday lull" in the current threat landscape. Organizations worldwide faced an average of 2,090 cyberattacks per week, a 17% increase over

the breach report
Hello and welcome back to The Breach Report! December 2025 closed the year with a stark reminder: cyber risk is now systemic, relentless, and indiscriminate. While the holiday season usually brings a slowdown in business, threat actors leveraged the "seasonal shift" to exploit skeletal staffing and holiday-themed social

the breach report
Hello and welcome back to The Breach Report! November 2025 was a month of relentless pressure, marked by a critical shift in how threats materialize. While the world watched a temporary U.S. government shutdown freeze federal breach reporting, the private sector and global entities faced a sophisticated "identity-first&
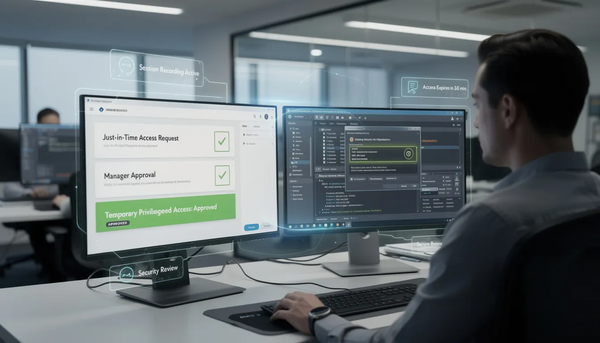
privileged access management
How privileged access management reduces risk, protects sensitive systems, and supports compliance through least privilege and secure credential control.
best practices
Explore key methods and best practices in cryptographic authentication to enhance your security.

cyberattack
A technical analysis of the increase in cyberattacks, emerging cybersecurity threats, ransomware trends, AI driven threats, and strategies organizations can use to strengthen cyber resilience.

access control
Explore the latest access control tech solutions that boost security and streamline operations. Discover effective strategies to enhance your safety.

best practices
How the pillars of cybersecurity strengthen risk management, protect sensitive data, and support business continuity.
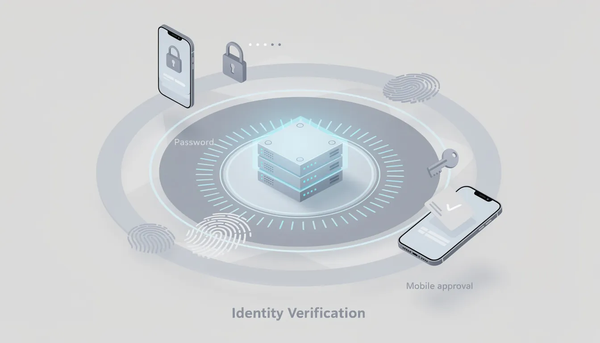
best practices
Discover the importance of two-factor authentication (2FA) for protecting your online accounts.

cybersecurity policy
How a SOC for cybersecurity strengthens risk management, proves compliance, and improves organizational resilience.

privileged access management
Learn how Azure Privileged Identity Management enhances security by managing access and roles effectively.